docker容器网络
Docker在安装后自动提供3种网络,可以使用docker network ls命令查看
[root@localhost ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
3664f5f52f3e bridge bridge local
8ab40bae74b5 host host local
6ae96818bcac none null local
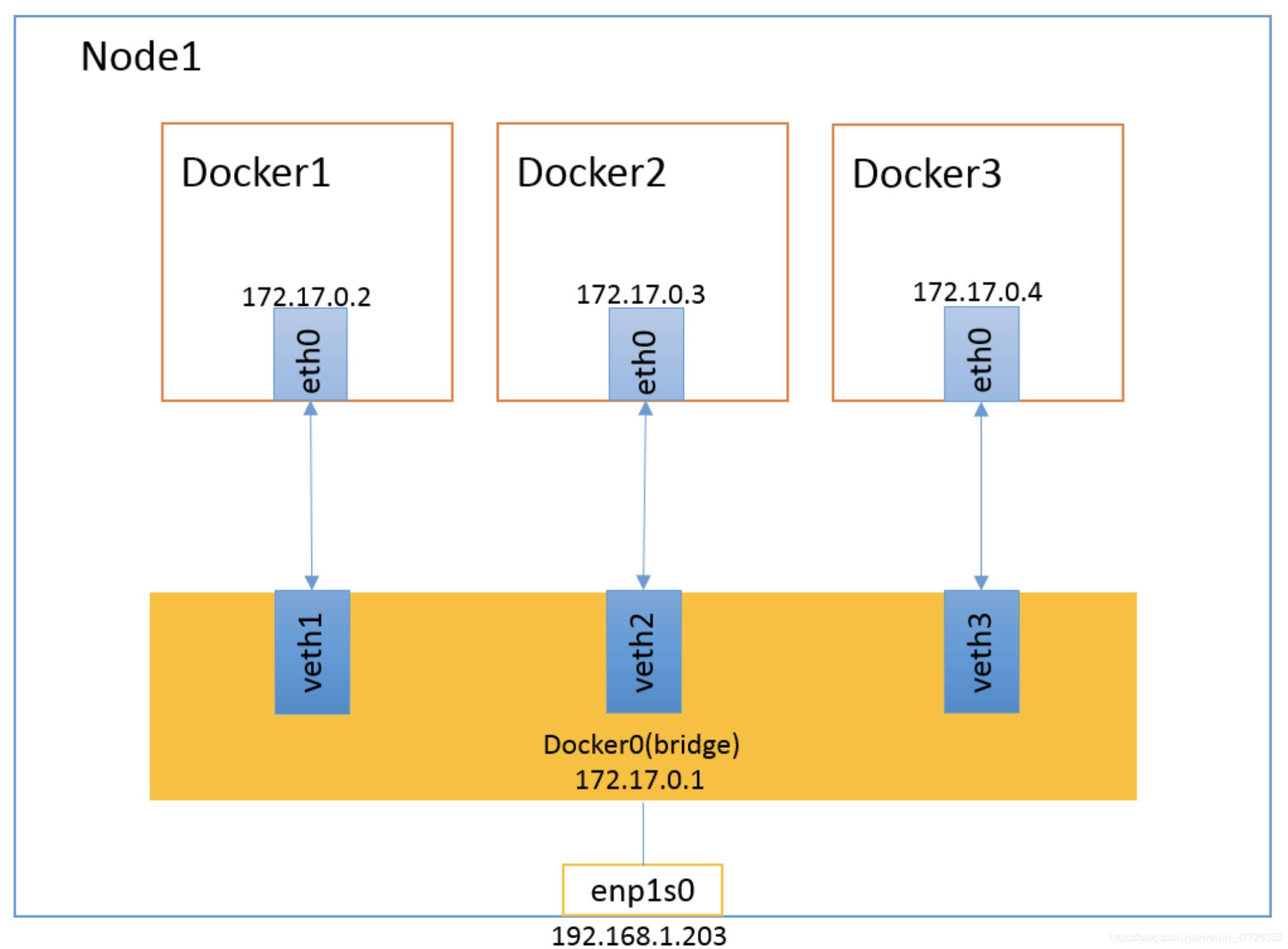
Docker使用Linux桥接,在宿主机虚拟一个Docker容器网桥(docker0),Docker启动一个容器时会根据Docker网桥的网段分配给容器一个IP地址,称为Container-IP,同时Docker网桥是每个容器的默认网关。因为在同一宿主机内的容器都接入同一个网桥,这样容器之间就能够通过容器的Container-IP直接通信。
查看IP去进入容器去ping本机的IP看是否能够ping通
[root@localhost ~]# docker inspect 65553cae95be
结果省略
[root@localhost ~]# docker exec -it ef0c6e61571c /bin/sh
/ # ping 172.17.0.3 //进入另一个容器去ping
PING 172.17.0.3 (172.17.0.3): 56 data bytes
64 bytes from 172.17.0.3: seq=0 ttl=64 time=0.415 ms
64 bytes from 172.17.0.3: seq=1 ttl=64 time=0.311 ms
64 bytes from 172.17.0.3: seq=2 ttl=64 time=0.321 ms
^C
--- 172.17.0.3 ping statistics ---
3 packets transmitted, 3 packets received, 0% packet loss
round-trip min/avg/max = 0.311/0.349/0.415 ms
/ # wget 172.17.0.3
Connecting to 172.17.0.3 (172.17.0.3:80)
saving to 'index.html'
index.html 100% |*****************************************| 612 0:00:00 ETA
'index.html' saved
docker的4种网络模式
| 网络模式 | 配置 | 说明 |
|---|
| host | –network host | 容器和宿主机共享Network namespace |
| container | –network container:NAME_OR_ID | 容器和另外一个容器共享Network namespace |
| none | –network none | 容器有独立的Network namespace,但并没有对其进行任何网络设置 |
| bridge | –network bridge | 默认模式 |

bridge模式
当Docker进程启动时,会在主机上创建一个名为docker0的虚拟网桥,此主机上启动的Docker容器会连接到这个虚拟网桥上。虚拟网桥的工作方式和物理交换机类似,这样主机上的所有容器就通过交换机连在了一个二层网络中。
从docker0子网中分配一个IP给容器使用,并设置docker0的IP地址为容器的默认网关。在主机上创建一对虚拟网卡veth pair设备,Docker将veth pair设备的一端放在新创建的容器中,并命名为eth0(容器的网卡),另一端放在主机中,以vethxxx这样类似的名字命名,并将这个网络设备加入到docker0网桥中。可以通过brctl show命令查看。
可以看到网卡是一对一对出现,34和35是一对。
[root@localhost ~]# docker network ls
NETWORK ID NAME DRIVER SCOPE
3664f5f52f3e bridge bridge local
8ab40bae74b5 host host local
6ae96818bcac none null local
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
ef0c6e61571c yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 22 hours ago Up 22 hours intelligent_hermann
[root@localhost ~]# docker exec -it ef0c6e61571c /bin/sh
/ # ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
34: eth0@if35: <BROADCAST,MULTICAST,UP,LOWER_UP,M-DOWN> mtu 1500 qdisc noqueue //网卡为34
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
/ # exit
[root@localhost ~]# ip a 本机ip为35
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:1e:69:85 brd ff:ff:ff:ff:ff:ff
inet 192.168.175.100/24 brd 192.168.175.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::ea80:e71e:f5fc:9a2c/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP
link/ether 02:42:a5:12:84:e8 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:a5ff:fe12:84e8/64 scope link
valid_lft forever preferred_lft forever
35: veth5c45d5b@if34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0 state UP
link/ether 36:a5:11:b3:b4:39 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet6 fe80::34a5:11ff:feb3:b439/64 scope link
valid_lft forever preferred_lft forever
安装
[root@localhost ~]# yum -y install bridge-utils
[root@localhost ~]# brctl show 可以看到绑定了两个网卡,下面也运行了两个容器
bridge name bridge id STP enabled interfaces
docker0 8000.0242a51284e8 no veth5c45d5b
veth8b885b6
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
65553cae95be nginx "/docker-entrypoint.…" 22 minutes ago Up 22 minutes 80/tcp clever_jang
ef0c6e61571c yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 23 hours ago Up 23 hours intelligent_hermann
bridge模式是docker的默认网络模式,不写–network参数,就是bridge模式。使用docker run -p时,docker实际是在iptables做了DNAT规则,实现端口转发功能。可以使用iptables -t nat -vnL查看。
启动一个容器
[root@localhost ~]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
yangcan1121/nginx v0.2 dba666d3304f 23 hours ago 1.22MB
nginx latest 4bb46517cac3 2 weeks ago 133MB
busybox latest 018c9d7b792b 4 weeks ago 1.22MB
[root@localhost ~]# docker run -d -p 8080:80 yangcan1121/nginx:v0.2 //映射端口
9757c6f88315285a01f8c6a9935e99c98691c97670db509a9f0b51a06b3a3d74
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
9757c6f88315 yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 6 seconds ago Up 5 seconds 0.0.0.0:8080->80/tcp jolly_satoshi
65553cae95be nginx "/docker-entrypoint.…" 30 minutes ago Up 29 minutes 80/tcp clever_jang
ef0c6e61571c yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 23 hours ago Up 23 hours intelligent_hermann
页面测试

[root@localhost ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
bridge模式如下图所示:
只需把容器停掉就没有ip
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
9757c6f88315 yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 5 minutes ago Up 5 minutes 0.0.0.0:8080->80/tcp jolly_satoshi
65553cae95be nginx "/docker-entrypoint.…" 35 minutes ago Up 35 minutes 80/tcp clever_jang
ef0c6e61571c yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 23 hours ago Up 23 hours intelligent_hermann
[root@localhost ~]# docker stop 9757c6f88315
9757c6f88315
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
65553cae95be nginx "/docker-entrypoint.…" 36 minutes ago Up 36 minutes 80/tcp clever_jang
ef0c6e61571c yangcan1121/nginx:v0.2 "/bin/httpd -f -h /d…" 23 hours ago Up 23 hours intelligent_hermann
[root@localhost ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:1e:69:85 brd ff:ff:ff:ff:ff:ff
inet 192.168.175.100/24 brd 192.168.175.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::ea80:e71e:f5fc:9a2c/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP
link/ether 02:42:a5:12:84:e8 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:a5ff:fe12:84e8/64 scope link
valid_lft forever preferred_lft forever
35: veth5c45d5b@if34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0 state UP
link/ether 36:a5:11:b3:b4:39 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet6 fe80::34a5:11ff:feb3:b439/64 scope link
valid_lft forever preferred_lft forever
37: veth8b885b6@if36: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0 state UP
link/ether 72:c8:f7:ca:19:39 brd ff:ff:ff:ff:ff:ff link-netnsid 1
inet6 fe80::70c8:f7ff:feca:1939/64 scope link
valid_lft forever preferred_lft forever
假设上图的docker2中运行了一个nginx,大家来想几个问题:
同主机间两个容器间是否可以直接通信?比如在docker1上能不能直接访问到docker2的nginx站点?
在宿主机上能否直接访问到docker2的nginx站点?
在另一台主机上如何访问node1上的这个nginx站点呢?DNAT发布?
Docker网桥是宿主机虚拟出来的,并不是真实存在的网络设备,外部网络是无法寻址到的,这也意味着外部网络无法通过直接Container-IP访问到容器。如果容器希望外部访问能够访问到,可以通过映射容器端口到宿主主机(端口映射),即docker run创建容器时候通过 -p 或 -P 参数来启用,访问容器的时候就通过[宿主机IP]:[容器端口]访问容器。
container模式
这个模式指定新创建的容器和已经存在的一个容器共享一个 Network Namespace,而不是和宿主机共享。新创建的容器不会创建自己的网卡,配置自己的 IP,而是和一个指定的容器共享 IP、端口范围等。同样,两个容器除了网络方面,其他的如文件系统、进程列表等还是隔离的。两个容器的进程可以通过 lo 网卡设备通信。
container模式如下图所示:

启动一个nginx的容器
[root@localhost ~]# docker run -d nginx
80630f306c51397e3549c2c7b0ce796221554c290da5eeae0e0ff2962e2b1a78
创建一个容器网络,跟以上容器用一个ID
[root@localhost ~]# docker run -it --network container:80630f306c51 busybox /bin/sh
/ #
[root@localhost ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
e82605989bed busybox "/bin/sh" 38 seconds ago Up 37 seconds silly_chandrasekhar
80630f306c51 nginx "/docker-entrypoint.…" 6 minutes ago Up 6 minutes 80/tcp funny_williamson
[root@localhost ~]# docker inspect e82605989bed //发现没有IP
[
{
"Id": "e82605989bed6f4b767bcc20687977cb1d4b8b4ff851ab55f5c9b2f7e06e3914",
查看另一个,可以看到IP
[root@localhost ~]# docker inspect 80630f306c51
省略。。。。。。
00e66a238",
"Gateway": "172.17.0.1",
"IPAddress": "172.17.0.2",
"IPPrefixLen": 16,
"IPv6Gateway": "",
"GlobalIPv6Address": "",
"GlobalIPv6PrefixLen": 0,
"MacAddress": "02:42:ac:11:00:02",
"DriverOpts": null
}
}
}
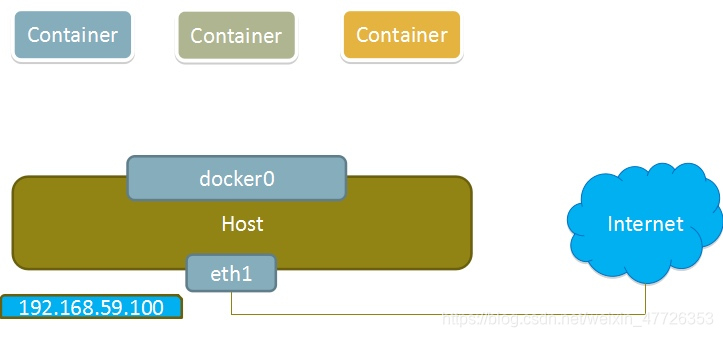
host模式
如果启动容器的时候使用host模式,那么这个容器将不会获得一个独立的Network Namespace,而是和宿主机共用一个Network Namespace。容器将不会虚拟出自己的网卡,配置自己的IP等,而是使用宿主机的IP和端口。但是,容器的其他方面,如文件系统、进程列表等还是和宿主机隔离的。
使用host模式的容器可以直接使用宿主机的IP地址与外界通信,容器内部的服务端口也可以使用宿主机的端口,不需要进行NAT,host最大的优势就是网络性能比较好,但是docker host上已经使用的端口就不能再用了,网络的隔离性不好。
Host模式如下图所示:

容器里面创建目录,真机里面不会存在
[root@localhost ~]# docker run -it --network host centos /bin/bash
[root@localhost /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:1e:69:85 brd ff:ff:ff:ff:ff:ff
inet 192.168.175.100/24 brd 192.168.175.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::ea80:e71e:f5fc:9a2c/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether 02:42:a5:12:84:e8 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:a5ff:fe12:84e8/64 scope link
valid_lft forever preferred_lft forever
[root@localhost /]# ls
bin etc lib lost+found mnt proc run srv tmp var
dev home lib64 media opt root sbin sys usr
[root@localhost /]# mkdir /data
[root@localhost /]# echo 'hello world' > data/index.html
[root@localhost /]# ls /
bin dev home lib64 media opt root sbin sys usr
data etc lib lost+found mnt proc run srv tmp var
真机查看
[root@localhost ~]# ls /
bin dev home lib64 mnt proc run srv tmp var
boot etc lib media opt root sbin sys usr
none模式
使用none模式,Docker容器拥有自己的Network Namespace,但是,并不为Docker容器进行任何网络配置。也就是说,这个Docker容器没有网卡、IP、路由等信息。需要我们自己为Docker容器添加网卡、配置IP等。
这种网络模式下容器只有lo回环网络,没有其他网卡。none模式可以在容器创建时通过–network none来指定。这种类型的网络没有办法联网,封闭的网络能很好的保证容器的安全性。
应用场景:
启动一个容器处理数据,比如转换数据格式
一些后台的计算和处理任务
none模式如下图所示:
[root@localhost ~]# docker run -it --network none centos /bin/bash
[root@fbf1cca80d09 /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
容器创建目录真机也不会创建
[root@fbf1cca80d09 /]# mkdir /data
[root@fbf1cca80d09 /]# ls /
bin dev home lib64 media opt root sbin sys usr
data etc lib lost+found mnt proc run srv tmp var
[root@localhost ~]# ls /
bin dev home lib64 mnt proc run srv tmp var
boot etc lib media opt root sbin sys usr
查看bridge网络的详细配置
[root@localhost ~]# docker network inspect bridge
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)