为service编写sepolicy
由init启动的service服务要在各自的selinux domain中运行。具体flow如下:
init.devices.rc中声明service,将在init时启动:
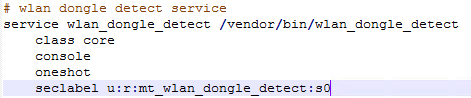
Note:seclabel标签用作设定service运行domain,如果设置了如下的init_daemon_domain便不需要该标签,该标签的优先级比init_daemon_domain要高
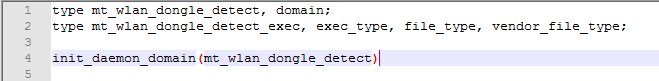
1 创建一个新的domain及file type
创建sepolicy文件device/manufacturer/device-name/sepolicy/mt_wlan_dongle_detect.te
内容如下:
Note:不是一定要使用目录device/manufacturer/device-name/sepolicy,以BOARD_SEPOLICY_DIRS宏为准 指定device sepolicy目录
L1 创建mt_wlan_dongle_detect domain
L2 创建mt_wlan_dongle_detect_exec file type
L3 声明为init的 service domain
init_daemin_damain实现如下, 主要是设置selinux,在init执行service bin时,允许由init domain自动转到service对应的domain:
/system/sepolicy/prebuilts/api/30.0/public/te_macros
#####################################
159 # init_daemon_domain(domain)
160 # Set up a transition from init to the daemon domain
161 # upon executing its binary.
162 define(`init_daemon_domain', `
163 domain_auto_trans(init, $1_exec, $1)
164 ')
#####################################
24 # domain_auto_trans(olddomain, type, newdomain)
25 # Automatically transition from olddomain to newdomain
26 # upon executing a file labeled with type.
27 #
28 define(`domain_auto_trans', `
29 # Allow the necessary permissions.
30 domain_trans($1,$2,$3)
31 # Make the transition occur by default.
32 type_transition $1 $2:process $3;
33 ')
#####################################
2 # domain_trans(olddomain, type, newdomain)
3 # Allow a transition from olddomain to newdomain
4 # upon executing a file labeled with type.
5 # This only allows the transition; it does not
6 # cause it to occur automatically - use domain_auto_trans
7 # if that is what you want.
8 #
9 define(`domain_trans', `
10 # Old domain may exec the file and transition to the new domain.
11 allow $1 $2:file { getattr open read execute map };
12 allow $1 $3:process transition;
13 # New domain is entered by executing the file.
14 allow $3 $2:file { entrypoint open read execute getattr map };
15 # New domain can send SIGCHLD to its caller.
16 ifelse($1, `init', `', `allow $3 $1:process sigchld;')
17 # Enable AT_SECURE, i.e. libc secure mode.
18 dontaudit $1 $3:process noatsecure;
19 # XXX dontaudit candidate but requires further study.
20 allow $1 $3:process { siginh rlimitinh };
21 ')
2 标记exec_bin到对应的file type
增加如下内容到 device/manufacturer/device-name/sepolicy/file_contexts

其中 u代表user用户,object_r代表是文件类型,mt_wlan_dongle_detect_exec是file type, s0是安全等级
sepolicy语法可参考https://www.cnblogs.com/jiangzhaowei/p/11830992.html详细介绍
3 编译并烧录 boot及system image
4 重定义sepolicy
经典的解Selinux问题的步骤
1、将平台以permissive模式运行,cmd如下
### set on mboot
### set permissive
<< MStar >># ac androidboot.selinux permissive
### set enforcing
<< MStar >># ac androidboot.selinux enforcing
### set on linux
su
setenforce 0 (0 for permissive 1 for enforcing)
2、获取logcat 或者dmesg,其中"avc: denied …“字样为selinux deny log
avc: denied { execute_no_trans } for path=”/vendor/bin/iwpriv" dev=“dm-5” ino=150 scontext=u:r:vendor_shell:s0 tcontext=u:object_r:mt_wifi_set_exec:s0 tclass=file permissive=0
3、通过audit2allow工具,生成建议的sepolicy
# run on build server. sepolicy.logcat is the logcat file
~ cat sepolicy.logcat | gerp wlan_dongle_detect |audit2allow
会生成类似如下
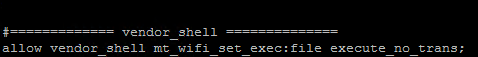
4、根据建议的条目,添加至对应sepolicy文件中device/manufacturer/device-name/sepolicy/mt_wlan_dongle_detect.te
有些添加原则可以参考如下url:
https://source.android.com/security/selinux/customize
5、重新build image,并验证service可正常运行
sepolicy的一些限制及解决方法
hal service 不允许execute_no_trans权限
/system/sepolicy/public/hal_neverallows.te
30 ###
31 # HALs are defined as an attribute and so a given domain could hypothetically
32 # have multiple HALs in it (or even all of them) with the subsequent policy of
33 # the domain comprised of the union of all the HALs.
34 #
35 # This is a problem because
36 # 1) Security sensitive components should only be accessed by specific HALs.
37 # 2) hwbinder_call and the restrictions it provides cannot be reasoned about in
38 # the platform.
39 # 3) The platform cannot reason about defense in depth if there are
40 # monolithic domains etc.
41 #
42 # As an example, hal_keymaster and hal_gatekeeper can access the TEE and while
43 # its OK for them to share a process its not OK with them to share processes
44 # with other hals.
45 #
46 # The following neverallow rules, in conjuntion with CTS tests, assert that
47 # these security principles are adhered to.
48 #
49 # Do not allow a hal to exec another process without a domain transition.
50 # TODO remove exemptions.
51 neverallow {
52 halserverdomain
53 -hal_dumpstate_server
54 -hal_telephony_server
55 } { file_type fs_type }:file execute_no_trans;
当HAL Service添加execute_no_trans权限是 会由于与hal_neverallows.te冲突导致,无法build pass.
从上面code可以发现 hal service不允许execute_no_trans权限。
解决方法
当HAL Service运行execv系列、fork等API时,会以domain不改变的方式执行新的程序,所以需要execute_no_trans权限。
如下logcat fail,hal_networkproxy_mediatek hal service需要执行/vendor/bin/sh
avc: denied { execute_no_trans } for
path="/vendor/bin/sh" dev="dm-5" ino=232
scontext=u:r:hal_networkproxy_mediatek:s0
tcontext=u:object_r:vendor_shell_exec:s0
tclass=file permissive=0
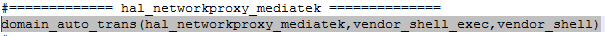
因execute_no_trans权限无法使用,可以使用domain_auto_trans宏,使得当hal service执行其他bin档时,可以转到对应domain中。
如下增加的sepolicy,hal_networkproxy_mediatek执行vend_shell_exec时,会自动转到vend_shell domain中
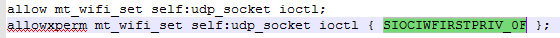
ioctl权限除了allow之外 还需要allowxperm
avc: denied { ioctl } for path=“socket:[38698]” dev=“sockfs” ino=38698 ioctlcmd=0x8bef scontext=u:r:mt_wifi_set:s0 tcontext=u:r:mt_wifi_set:s0 tclass=udp_socket permissive=1
1、找到ioctlcmd=0x8bef对应的CMD
/system/sepolicy/public/ioctl_defines
define(`SIOCIWFIRSTPRIV_0F', `0x00008bef')
2、编写sepolicy
单独编译及单独升级方法
Partial Build
you can partial build selinux with the following commands
cd $(ANDROID_BUILD_TOP)
touch system/sepolicy/private/genfs_contexts
mmm system/sepolicy
Partial Update
Windows ADB
adb root
adb remount
adb push out\target\product\$(DEVICE)\vendor\etc\selinux /vendor/etc/
adb push out\target\product\$(DEVICE)\system\etc\selinux /system/etc/
adb shell sync; sync; sync;
adb reboot
Linux ADB
adb root
adb remount
adb push out/target/product/$(DEVICE)/vendor/etc/selinux /vendor/etc/selinux
adb push out/target/product/$(DEVICE)/system/etc/selinux /system/etc/selinux
adb shell sync; sync; sync;
adb reboot
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)