说明
kubeadm方式部署的k8s默认证书的年限为1一年,当集群更新时,证书也会更新,如果集群每年都会更新,那么证书年限就不用修改。但是大部分情况下,为了保证线上环境稳定,集群很少去修改。所以需要将证书时间修改一下。
查看集群证书有效期
进入目录
cd /etc/kubernetes/pki/
查看有效期
openssl x509 -in apiserver.crt -text -noout

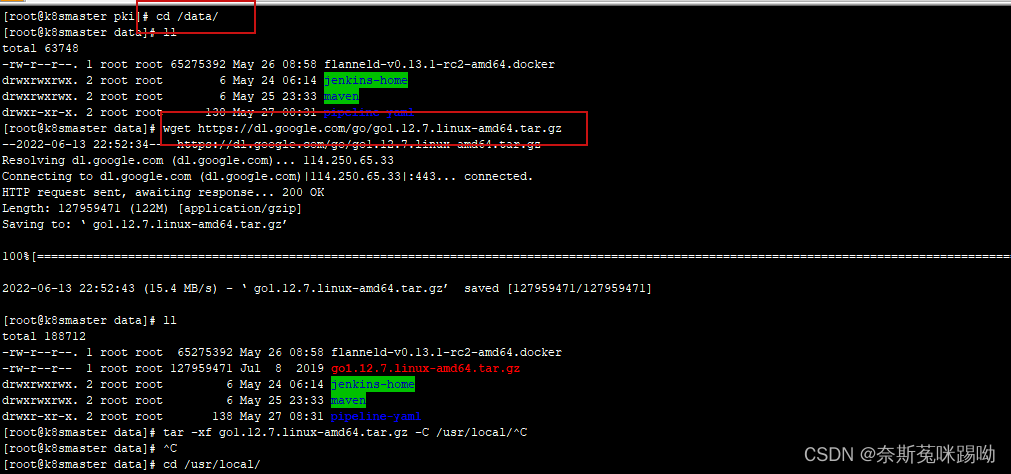
安装go环境
cd /data/
wget https://dl.google.com/go/go1.13.4.linux-amd64.tar.gz
tar -xf go1.12.7.linux-amd64.tar.gz -C /usr/local/
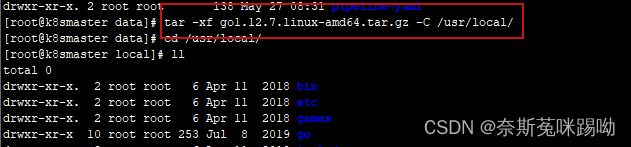
配置go环境变量
/etc/profile最末尾添加
export PATH=$PATH:/usr/local/go/bin
vim /etc/profile
刷新配置变量生效
source /etc/profile
此时安装完毕,查看版本
go version
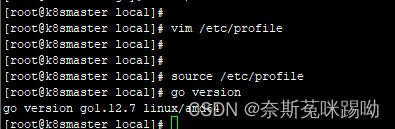
克隆k8s的项目(需要一段时间)
git clone https://github.com/kubernetes/kubernetes.git
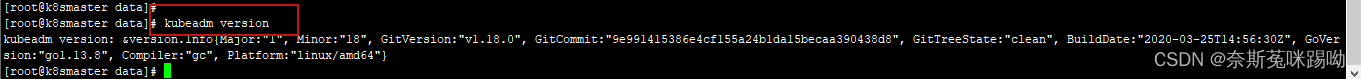
查看kubeadm版本
kubeadm version
kubeadm version: &version.Info{Major:"1", Minor:"18", GitVersion:"v1.18.0", GitCommit:"9e991415386e4cf155a24b1da15becaa390438d8", GitTreeState:"clean", BuildDate:"2020-03-25T14:56:30Z", GoVersion:"go1.13.8", Compiler:"gc", Platform:"linux/amd64"}
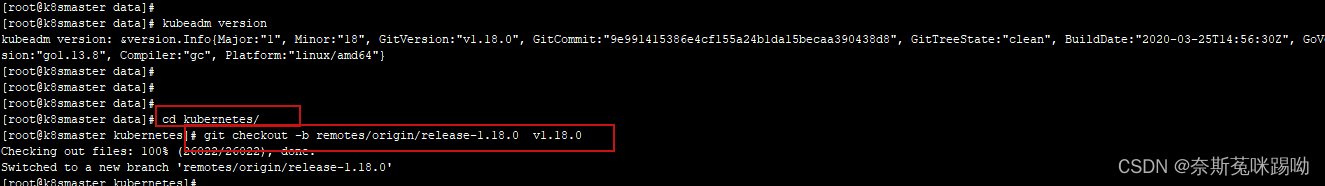
切换到新的版本
cd kubernetes/
git checkout -b remotes/origin/release-1.18.0 v1.18.0
修改 Kubeadm 源码包更新证书策略
vim cmd/kubeadm/app/util/pkiutil/pki_helpers.go
找到NewSignedCert方法
// NewSignedCert creates a signed certificate using the given CA certificate and key
func NewSignedCert(cfg *certutil.Config, key crypto.Signer, caCert *x509.Certificate, caKey crypto.Signer) (*x509.Certificate, error) {
const duration365d = time.Hour * 24 * 365 * 10 #新增一个常量,这个意思是1个小时*24*365*10=10年
serial, err := cryptorand.Int(cryptorand.Reader, new(big.Int).SetInt64(math.MaxInt64))
if err != nil {
return nil, err
}
if len(cfg.CommonName) == 0 {
return nil, errors.New("must specify a CommonName")
}
if len(cfg.Usages) == 0 {
return nil, errors.New("must specify at least one ExtKeyUsage")
}
certTmpl := x509.Certificate{
Subject: pkix.Name{
CommonName: cfg.CommonName,
Organization: cfg.Organization,
},
DNSNames: cfg.AltNames.DNSNames,
IPAddresses: cfg.AltNames.IPs,
SerialNumber: serial,
NotBefore: caCert.NotBefore,
NotAfter: time.Now().Add(kubeadmconstants.CertificateValidity).UTC(), #改为time.Now().Add(duration365d).UTC(),
KeyUsage: x509.KeyUsageKeyEncipherment | x509.KeyUsageDigitalSignature,
ExtKeyUsage: cfg.Usages,
}
certDERBytes, err := x509.CreateCertificate(cryptorand.Reader, &certTmpl, caCert, key.Public(), caKey)
if err != nil {
return nil, err
}
编译kubeadm
在当前源码路径下
cd kubernetes/
make WHAT=cmd/kubeadm GOFLAGS=-v
cp _output/bin/kubeadm /root/kubeadm-new
更新 kubeadm(更新之前先备份)
将 kubeadm 进行替换
[root@k8s-master ~]# cp /usr/bin/kubeadm /usr/bin/kubeadm.old
[root@k8s-master ~]# cp /root/kubeadm-new /usr/bin/kubeadm
cp:是否覆盖"/usr/bin/kubeadm"? y
[root@k8s-master ~]# chmod +x /usr/bin/kubeadm
备份pki目录
cp -r /etc/kubernetes/pki /etc/kubernetes/pki.old
生成证书文件(这个config文件是初始化集群时候的配置)
kubeadm alpha certs renew all --config=/data/kubeadm-config.yaml
生成集群的配置文件及查看
如果集群没有kubeadm-config.yaml文件,可以生成一个k8s的初始化文件
kubeadm config view > /data/kubeadm-config.yaml
[root@k8s-master ~]# kubeadm alpha certs renew all --config=/data/kubeadm-config.yaml
certificate embedded in the kubeconfig file for the admin to use and for kubeadm itself renewed
certificate for serving the Kubernetes API renewed
certificate the apiserver uses to access etcd renewed
certificate for the API server to connect to kubelet renewed
certificate embedded in the kubeconfig file for the controller manager to use renewed
certificate for liveness probes to healtcheck etcd renewed
certificate for etcd nodes to communicate with each other renewed
certificate for serving etcd renewed
certificate for the front proxy client renewed
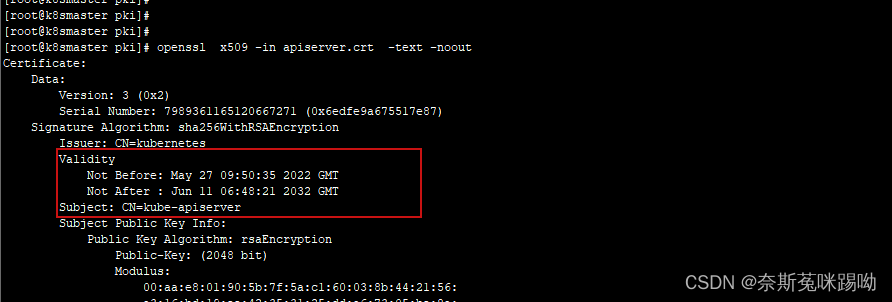
查看证书的年限
[root@k8s-master ~]# cd /etc/kubernetes/pki
[root@k8s-master pki]# openssl x509 -in apiserver.crt -text -noout
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 3637387775685121508 (0x327a98e9080f55e4)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN=kubernetes
Validity
Not Before: Apr 27 09:50:35 2022 GMT
Not After : Apr 11 06:48:21 2032 GMT
更新各节点证书
master上执行,替换xx.xx.xxx为各个节点ip
[root@k8s-node01 pki]# scp root@xx.xx.xxx:/etc/kubernetes/pki/ca.crt ./
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)