新添功能
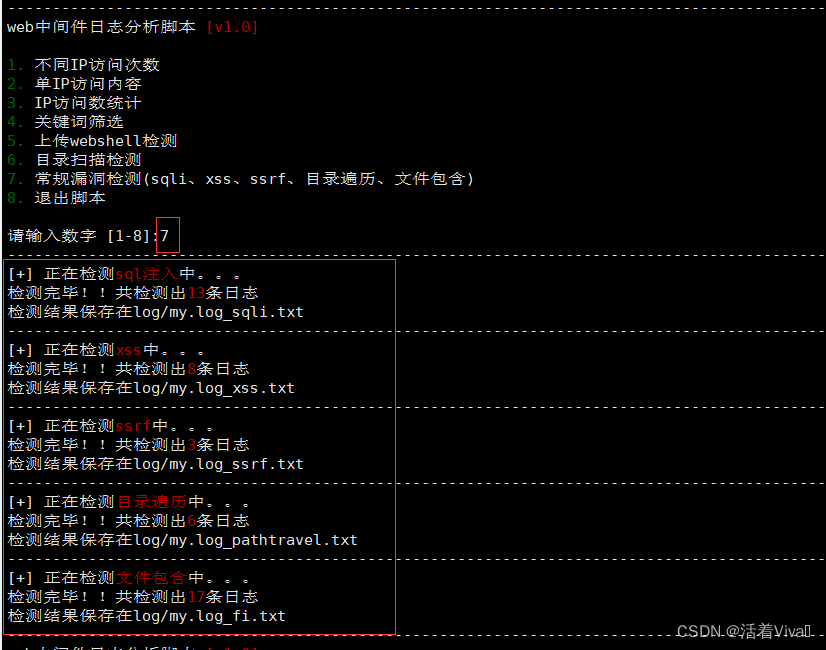
3.0版本加了ssrf、目录遍历文件包含、优化自动创建目录功能。
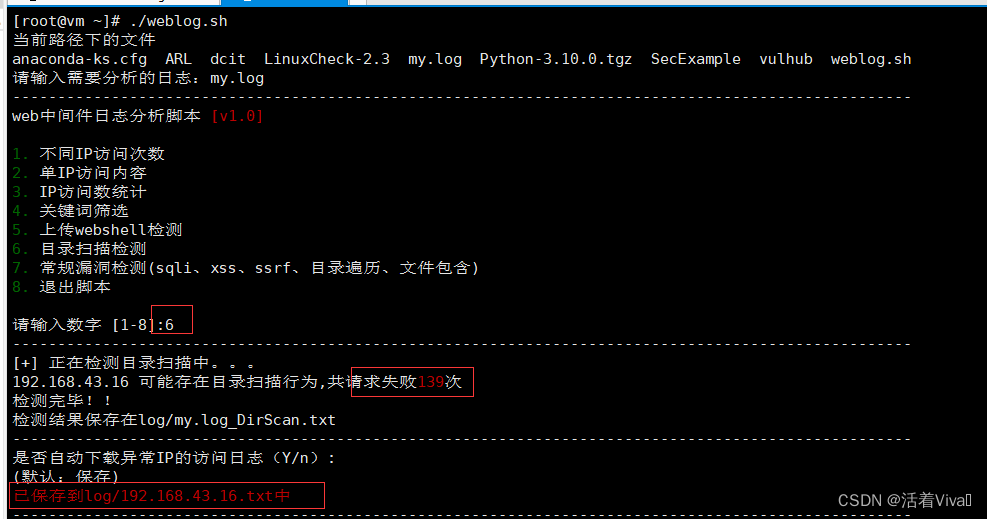
一般使用1、6、7即可
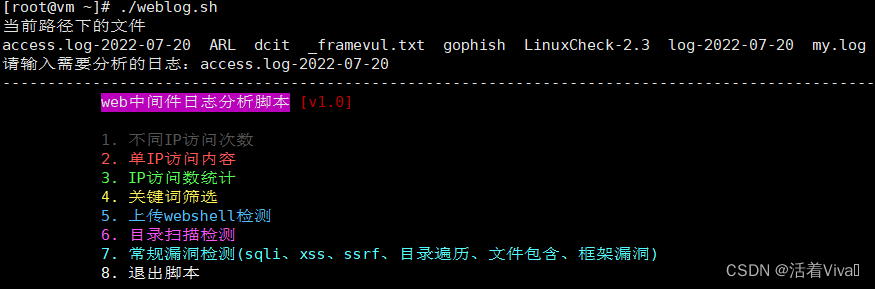
3.1版本
框架漏洞检测、封面字体颜色改变
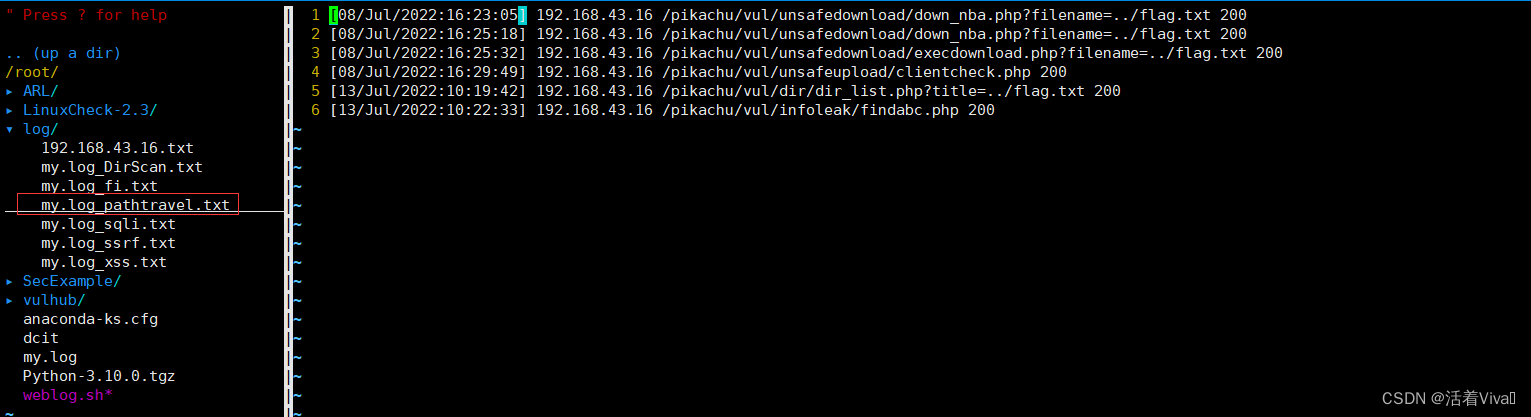
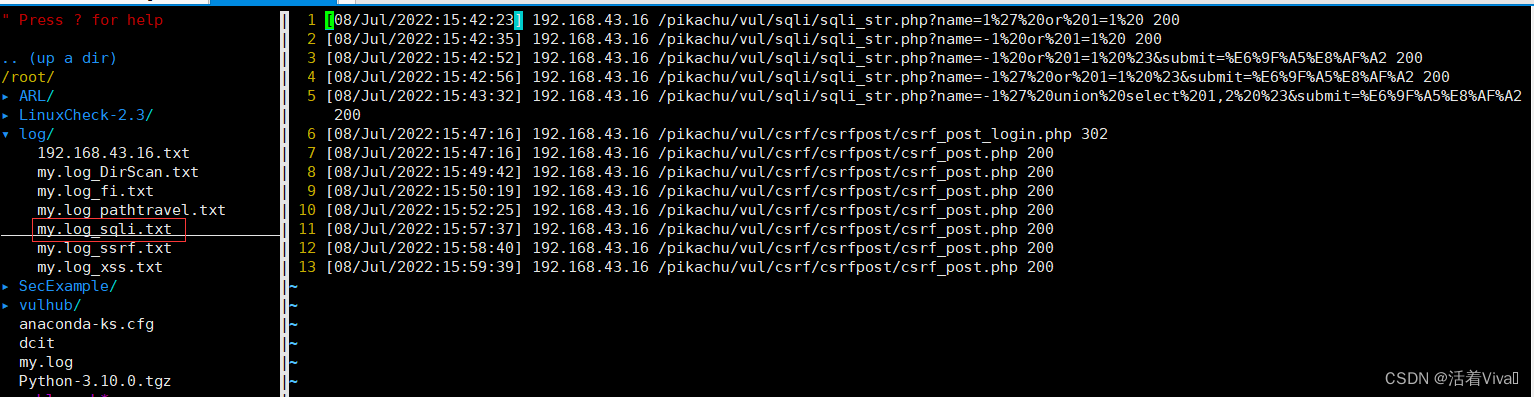
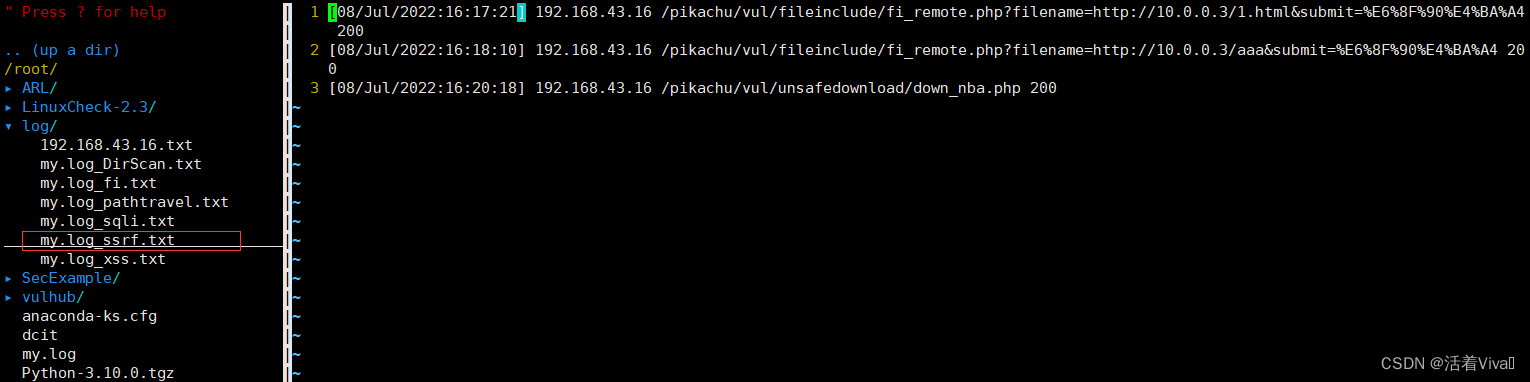
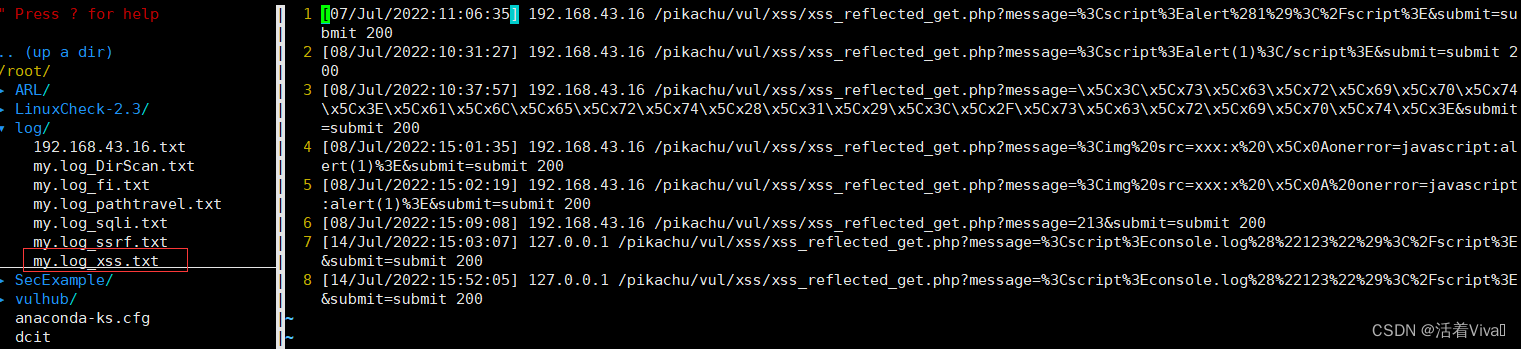
保存的日志
fi
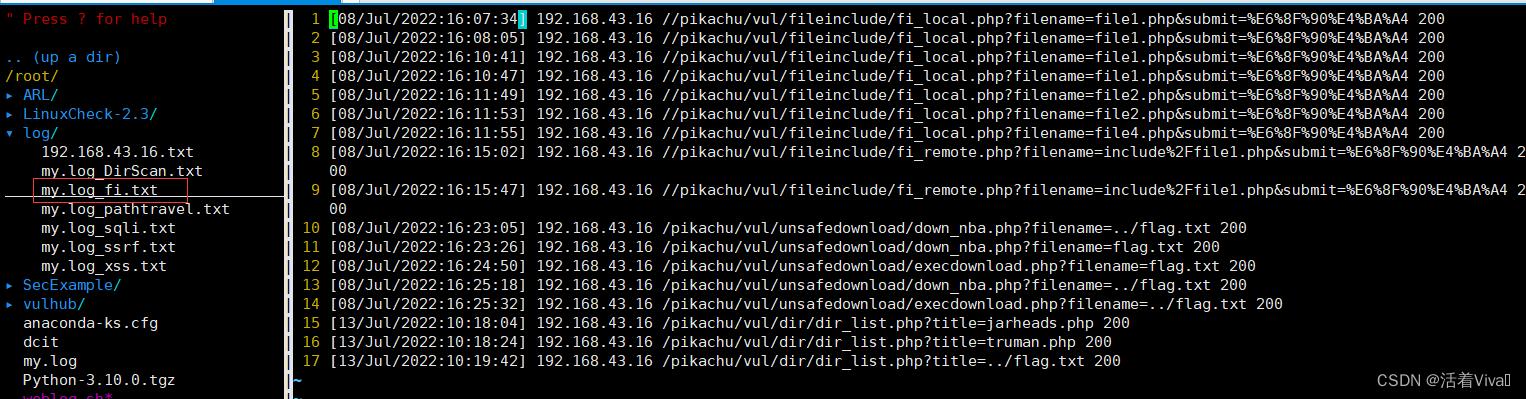
目录遍历
sqli
ssrf
xss
代码
#!/bin/bash
Green_font_prefix="\033[32m"
Red_font_prefix="\033[31m"
Font_color_suffix="\033[0m"
line(){
for i in {1..100};do
if [ $i -ne 100 ];then
echo -ne "-"
else
echo -e "-"
fi
done
}
diffip(){
line
echo -e "查看排名前(数字):"
read -e -p "(默认:全部)" num
[[ -z $num ]] && cut -d- -f 1 "$logfile"|sort| uniq -c | sort -rn || cut -d- -f 1 "$logfile"|sort| uniq -c | sort -rn | head -n $num
}
oneip(){
while true;do
echo -e "请输入需要分析的IP:"
read -e ip
line
if [ "$(grep ^$ip $logfile |wc -l)" -ne 0 ];then
grep ^$ip $logfile| awk '{print $4."]",$1,$7,$9}'
break
else
echo -e "${Red_font_prefix}未找到该IP!请重新输入!!${Font_color_suffix}"
line
continue
fi
done
}
savefile(){
echo -e "是否保存到文件中(Y/n):"
read -e -p "(默认:保存)" choose
[[ -z $choose ]] || [[ $choose == [Yy] ]] && grep ^$ip $logfile| awk '{print $4."]",$1,$7,$9}' > "$path$ip.txt" && echo -e "${Red_font_prefix}已保存到$path$ip.txt中${Font_color_suffix}"
}
howmanyip(){
line
awk '{print $1}' $logfile|sort|uniq|wc -l
}
keyword(){
while true;do
line
read -e -p "请输入关键词(q为退出):" key
if [ $key == "q" ];then
break
fi
more "$logfile" | grep "$key" | awk '{print $4."]",$1,$7,$9}'
done
}
webshell(){
line
echo -e "请输入文件上传的URI(如upload.php):"
read -e -p "(默认:退出)" upload
[[ -z $upload ]] || cat $logfile |grep -nP "POST.*$upload.*$upload" > ""$path$filename"_webshell.txt"
time=$(cat ""$path$filename"_webshell.txt" |wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_"webshell.txt""
}
dirscan(){
line
echo -e "[+] 正在检测目录扫描中。。。"
for i in $(awk '{print $1}' $logfile|sort|uniq);do
time=$(cat $logfile | grep -P "^$i.*\b404\b" | wc -l)
[[ time -gt 20 ]] && echo -e "$i 可能存在目录扫描行为,共请求失败${Red_font_prefix}$time${Font_color_suffix}次" && echo -e "$i 可能存在目录扫描行为,共请求失败${Red_font_prefix}$time${Font_color_suffix}次" >> "$path$filename"_"DirScan.txt"
done
echo -e "检测完毕!!"
echo -e "检测结果保存在"$path$filename"_"DirScan.txt""
line
echo -e "是否自动下载异常IP的访问日志(Y/n):"
read -e -p "(默认:保存)" choose1
ip_list=$(cat "$path$filename"_"DirScan.txt" | grep -oE '.* ')
if [[ -z $choose1 ]];then
for ip in $ip_list;do
grep ^$ip $logfile| awk '{print $4."]",$1,$7,$9}' > "$path$ip.txt" && echo -e "${Red_font_prefix}已保存到$path$ip.txt中${Font_color_suffix}"
done
fi
}
sqlicheck(){
line
echo -e "[+] 正在检测${Red_font_prefix}sql注入${Font_color_suffix}中。。。"
word="%20select%20|%20and%20|%20or%20|%20exec|%27exec| information_schema.tables|%20information_schema.tables|%20where%20|%20union%20|%20SELECT%20|%2ctable_name%20|cmdshell|%20table_schema"
grep -E "$word" $logfile | awk '{print $4."]",$1,$7,$9}'> ""$path$filename"_sqli.txt"
time=$(cat ""$path$filename"_sqli.txt" |wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_sqli.txt"
}
xsscheck(){
line
echo -e "[+] 正在检测${Red_font_prefix}xss${Font_color_suffix}中。。。"
grep -E "alert|script|<|>|%3C|%3c|%3e|%3E" $logfile | awk '{print $4."]",$1,$7,$9}' > ""$path$filename"_xss.txt"
time=$(cat ""$path$filename"_xss.txt" | wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_xss.txt"
}
ssrfcheck(){
line
echo -e "[+] 正在检测${Red_font_prefix}ssrf${Font_color_suffix}中。。。"
grep -E "=http://|=https://" $logfile | awk '{print $4."]",$1,$7,$9}' > ""$path$filename"_ssrf.txt"
time=$(cat ""$path$filename"_ssrf.txt" | wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_ssrf.txt"
}
pathtravelcheck(){
line
echo -e "[+] 正在检测${Red_font_prefix}目录遍历${Font_color_suffix}中。。。"
grep -E "\.\.|\.%2e/|\.%%32%65|%2e%2e" $logfile | awk '{print $4."]",$1,$7,$9}' > ""$path$filename"_pathtravel.txt"
time=$(cat ""$path$filename"_pathtravel.txt" | wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_pathtravel.txt"
}
fileinclude(){
line
echo -e "[+] 正在检测${Red_font_prefix}文件包含${Font_color_suffix}中。。。"
awk '{print $4."]",$1,$7,$9}' $logfile | grep -E "=.*jsp\b|=.*php\b|=.*txt\b|=.*jpg\b" > ""$path$filename"_fi.txt"
time=$(cat ""$path$filename"_fi.txt" | wc -l )
echo -e "检测完毕!!共检测出${Red_font_prefix}$time${Font_color_suffix}条日志"
echo -e "检测结果保存在"$path$filename"_fi.txt"
}
echo -e "当前路径下的文件" && ls
while true;do
read -e -p "请输入需要分析的日志:" logfile
find "$logfile" &>/dev/null
if [ $? -ne 0 ];then
echo -e "${Red_font_prefix}未找到日志,请输入文件名或绝对路径!!${Font_color_suffix}"
line
else
break
fi
done
filename=$(echo -e "$logfile"| awk -F '/' '{print $NF}')
if [[ $logfile == */* ]];then
path=$(echo -e "$logfile"|grep -o '.*/')
dirName=$(echo -e "$filename"| awk -F '.' '{print $2}')
[[ -d $dirName ]] || mkdir $path$dirName
path="$path$dirName/"
else
dirName=$(echo -e "$logfile"| awk -F '.' '{print $2}')
[[ -d $dirName ]] || mkdir $path$dirName
path="$dirName/"
fi
line
while true; do
echo -e "web中间件日志分析脚本 ${Red_font_prefix}[v1.0]${Font_color_suffix}
${Green_font_prefix}1.${Font_color_suffix} 不同IP访问次数
${Green_font_prefix}2.${Font_color_suffix} 单IP访问内容
${Green_font_prefix}3.${Font_color_suffix} IP访问数统计
${Green_font_prefix}4.${Font_color_suffix} 关键词筛选
${Green_font_prefix}5.${Font_color_suffix} 上传webshell检测
${Green_font_prefix}6.${Font_color_suffix} 目录扫描检测
${Green_font_prefix}7.${Font_color_suffix} 常规漏洞检测(sqli、xss、ssrf、目录遍历、文件包含)
${Green_font_prefix}8.${Font_color_suffix} 退出脚本
"
read -e -p "请输入数字 [1-8]:" num
if [ "$num" == "1" ];then
diffip
elif [ "$num" == "2" ];then
oneip
savefile
elif [ "$num" == "3" ];then
howmanyip
elif [ "$num" == "4" ];then
keyword
elif [ "$num" == "5" ];then
webshell
elif [ "$num" == "6" ];then
dirscan
elif [ "$num" == "7" ];then
sqlicheck
xsscheck
ssrfcheck
pathtravelcheck
fileinclude
elif [ "$num" == "8" ];then
echo -e ""
echo -e "${Green_font_prefix}
*****************************************
*********** 谢谢您的使用,再见************
*****************************************
${Font_color_suffix}"
exit 0
else
echo -e "${Red_font_prefix}请输入正确数字!!${Font_color_suffix}"
line
continue
fi
line
done
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)