第四届2021美团网络安全 MT-CTF
MISC
Un(ix)zip




flag{Welc0me_Unz1p_Wonder4}
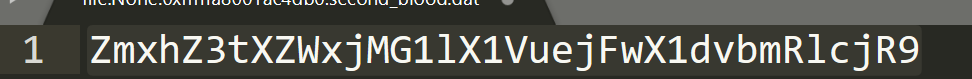
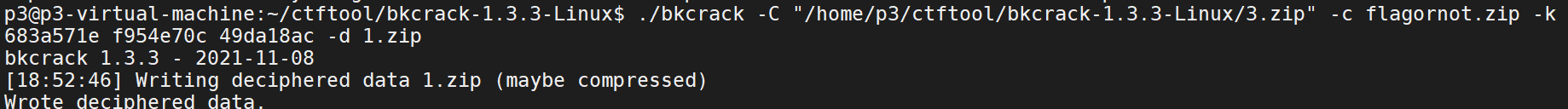
오징어 게임 鱿鱼游戏


7-zip可以看到加密算法ZipCrypto Store

再加上备注里提示flagornot.txt,采用明文爆破

明文爆破参考:https://blog.csdn.net/q851579181q/article/details/109767425
工具下载:bkcrack:https://github.com/kimci86/bkcrack
./bkcrack -C 3.zip -c flagornot.zip -p p.txt -o 30 -x 0 504B0304
#Keys: 683a571e f954e70c 49da18ac

./bkcrack -C "/home/p3/ctftool/bkcrack-1.3.3-Linux/3.zip" -c flagornot.zip -k 683a571e f954e70c 49da18ac -d 1.zip


然后是图片盲水印提取,比赛的时候没做出来

Boom

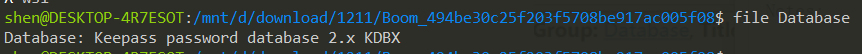
发现是 Keepass的数据库
Hashcat进行Keepass密码爆破:https://luxswf.github.io/2020/05/14/Hashcat%E7%88%86%E7%A0%B4/
https://www.rubydevices.com.au/blog/how-to-hack-keepass
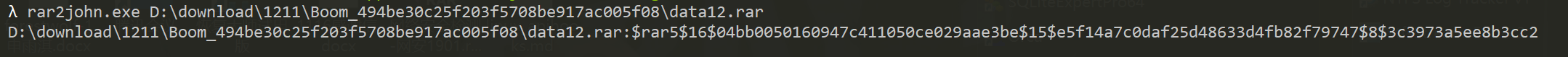
1.利用John the Ripper 解析出Hash值
keepass2john.exe Database
# $keepass$*2*60000*0*25798eeae830af9553a0d2beecfef834aba3a2f36cd78ec177287fdc102ca566*35287f29a42862c3b3522234f285fb091c1cac0e9bc7452dcc47a98599850083*9eb177215208b631b9a84c04a128f972*dbbfbd8653604286bb5e8d43c72cee9ce9f18074e0b8f202c79bb2475f906b1b*1bea912d6925ed287227ac86746402ee8c04df083b95859fbdc1203b50a620e7:
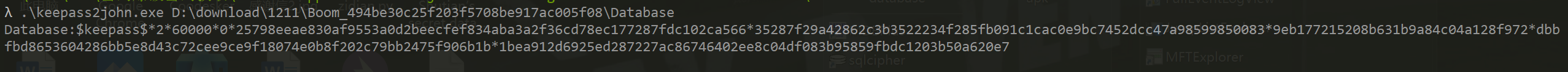
Hashcat破解Hash值
Hashcat64.exe -m 13400 hash.txt -a0 wordlist.dic -o found.txt

发现密码是个换行符(* ̄m ̄)

解压密码kqucm2u2ZIrq4DLyER2C,解压得到flag.png
zsteg分析png隐写
zsteg -a [png图片]

导出数据
zsteg -E "extradata:0" /home/kali/Desktop/flag.png > data
有点像是rar压缩包,补上文件头52 61 72 21
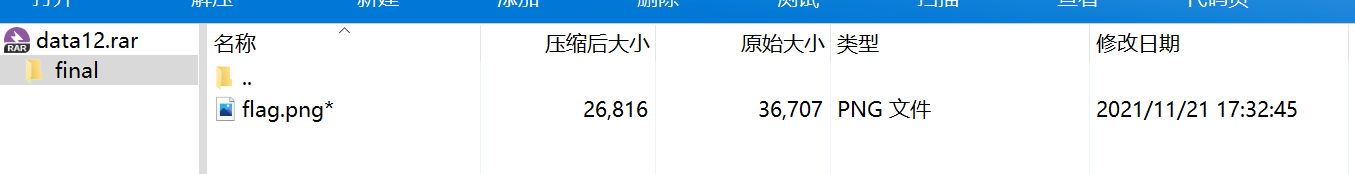
看了大佬的wp,哈哈,密码是783d793c313030,我是真的想不到,x=y<100,为什么
https://mp.weixin.qq.com/s?__biz=Mzg5NDY4NTc4NQ==&mid=2247484083&idx=1&sn=e28f921dee8b9a95524159556a74989f&chksm=c01a8585f76d0c93fa44f8368465b5953c2b91457dbb7b75683daf810e64e5d8e0b1d3fa6644&mpshare=1&scene=23&srcid=1212Tg9rishWwQX0pSg6dSav&sharer_sharetime=1639297811835&sharer_shareid=2cd15dd5abca7cee0fa30d6c72437d05#rd
解压得到的图片crc错误

crc爆破没出来

Crypto
Symbol

http://detexify.kirelabs.org/classify.html
https://blog.csdn.net/anscor/article/details/80878285
flag{fun_LaTeX_Math}

flag{e1b217dc3b5e90b237b45e0a636e5a86}