提示:以下是本篇文章正文内容,下面案例可供参考
一、漏洞描述
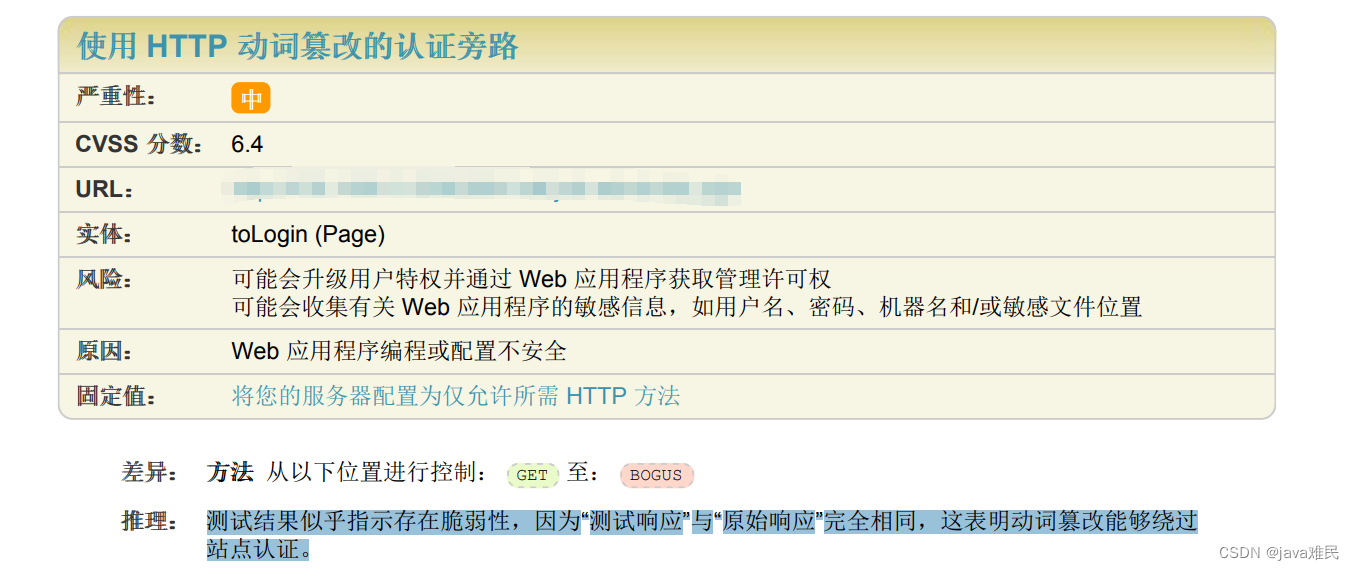
可能会升级用户特权并通过 Web 应用程序获取管理许可权可能会收集有关 Web 应用程序的敏感信息,如用户名、密码、机器名和/或敏感文件位置。
测试结果似乎指示存在脆弱性,因为“测试响应”与“原始响应”完全相同,这表明动词篡改能够绕过站点认证。
二、解决建议
增加拦截器,判断请求方式是否合法,合法则放行。
三、解决方法
Springboot 配置文件增加配置
# 信息安全
security:
#http请求方式配置
http:
#是否开启(开启:true 关闭:false)
enable: false
#允许的请求方式
allow:
- POST
- GET
编写配置类
/**
* @author wcs
* @desccription: 安全配置类
* @Date: 14:13 2022/2/28
*/
@Component
@Configuration
@ConfigurationProperties(prefix = "security")
public class SecurityConfig implements InitializingBean, DisposableBean {
private static Logger logger = LoggerFactory.getLogger(AspctConfig.class);
/**
* http防篡改
*/
private HttpConfig http;
/**
* xss攻击
*/
private XssConfig xss;
public HttpConfig getHttp() {
return http;
}
public void setHttp(HttpConfig http) {
this.http = http;
}
public XssConfig getXss() {
return xss;
}
public void setXss(XssConfig xss) {
this.xss = xss;
}
@Override
public void destroy() throws Exception {
}
@Override
public void afterPropertiesSet() throws Exception {
}
/**
* 实例化Http过滤器
*
* @return
*/
@Bean
@ConditionalOnProperty(prefix = "security", name = "http.enable", havingValue = "true")
public FilterRegistrationBean httpFilterRegistration() {
logger.info("hhtp过滤器初始化");
FilterRegistrationBean registration = new FilterRegistrationBean();
registration.setName("httpFilter");
registration.setOrder(3);
registration.addUrlPatterns("/*");
registration.setFilter(new HttpFilter());
return registration;
}
}
/**
* @author wcs
* @desccription: Http请求方式配置类
* @Date: 19:30 2022/2/28
*/
public class HttpConfig {
/**
* 是否启用
*/
private boolean enable;
/**
* 忽略的URL
*/
private List<String> allow;
public boolean isEnable() {
return enable;
}
public void setEnable(boolean enable) {
this.enable = enable;
}
public List<String> getAllow() {
return allow;
}
public void setAllow(List<String> allow) {
this.allow = allow;
}
}
编写过滤器
/**
* @author wcs 防止http 篡改过滤器
* @desccription:
* @Date: 19:03 2022/2/28
*/
public class HttpFilter implements Filter {
private static Logger LOGGER = LoggerFactory.getLogger(CsrfFilter.class);
/**
* 过滤器配置对象
*/
FilterConfig filterConfig = null;
private SecurityConfig security;
@Override
public void init(FilterConfig filterConfig) throws ServletException {
security = SpringUtils.getBean(SecurityConfig.class);
this.filterConfig = filterConfig;
}
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
HttpServletRequest request = (HttpServletRequest) servletRequest;
String method = request.getMethod();
if (isExcludeMethod(method)) {
filterChain.doFilter(servletRequest, servletResponse);
return;
} else {
servletResponse.setContentType("application/json; charset=UTF-8");
servletResponse.getWriter().write(JacksonUtil.writeValueAsString(new ReturnT<>(ReturnT.FAIL_CODE, "不支持的请求方式!")));
LOGGER.error("不支持的请求方式", method);
}
}
@Override
public void destroy() {
Filter.super.destroy();
}
/**
* 判断是否为忽略的URL
*
* @param method URL路径
* @return true-忽略,false-过滤
*/
private boolean isExcludeMethod(String method) {
if (security.getHttp().getAllow() == null || security.getHttp().getAllow().isEmpty()) {
return false;
}
return security.getHttp().getAllow().stream().map(pattern -> Pattern.compile("^" + pattern)).map(p -> p.matcher(method))
.anyMatch(Matcher::find);
}
}