TLS/SSL测试神器:testssl.sh安装使用说明
- 安装
- 各功能Cmd支持
- 测试
- Test All(全集)
- Test Ciphersuites(密码套件集)
- Test Vulnerable(漏洞)
- Test Server Defaults
- Test Server Preference
- Web网页版testssl.sh(免安装):
- 附
- 博主热门文章推荐:
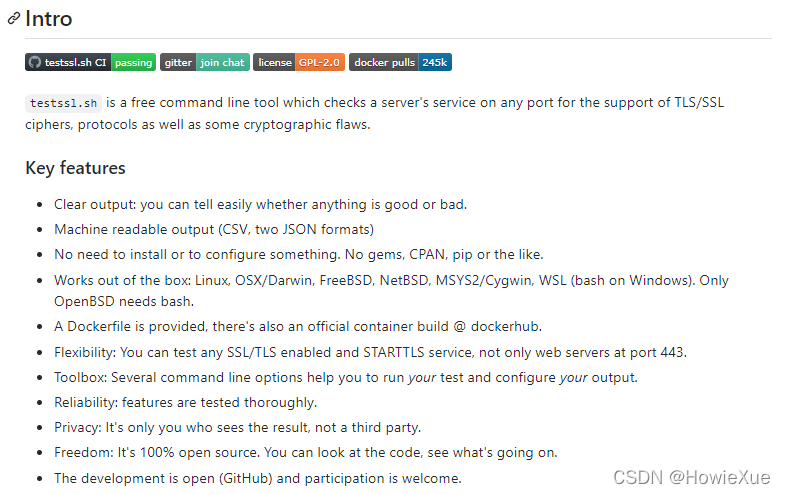
TLS/SSL测试神器:testssl.sh 是一款好用的TLS/SSL命令行测试工具,且完全免费开源。
testssl.sh可以对TLS/SSL Server端Cipher、Protocol进行检测,还可以进行CCS注入(CCS injection)、heartbleed等安全漏洞测试,功能全面丰富,可运行在Linux/BSD端,目前可以说是TLS Server端首选的测试工具。。
- 官网:https://testssl.sh/
- GitHub:https://github.com/drwetter/testssl.sh
其他检测工具常用的还有:https://myssl.com/ 和 https://www.ssllabs.com/ssltest/
安装
git clone --depth 1 https://github.com/drwetter/testssl.sh.git
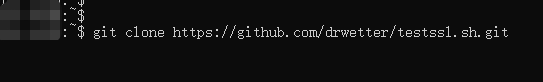
clone完后进入目录 cd testssl.sh/
就可以看到testssl.sh
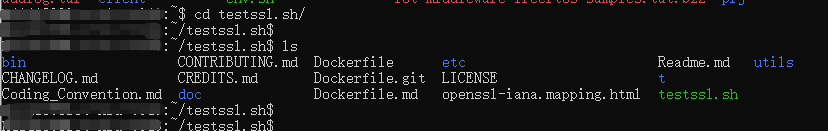
或者在官网https://testssl.sh/ 下载 package:
各功能Cmd支持
testssl.sh支持很多功能,testssl.sh --help如下:
其中常用的有
-E, --cipher-per-proto checks those per protocol, 检测各Protocol ciphersuites加密算法套件
-P, --server-preference displays the server’s picks: protocol+cipher,Server的首选协议+密码
-S, --server-defaults displays the server’s default picks and certificate info,Server的默认选择和证书信息
-U, --vulnerable tests all (of the following) vulnerabilities (if applicable), 检测所有漏洞
testssl.sh --help:
"testssl.sh [options] <URI>" or "testssl.sh <options>"
"testssl.sh <options>", where <options> is:
--help what you're looking at
-b, --banner displays banner + version of testssl.sh
-v, --version same as previous
-V, --local pretty print all local ciphers
-V, --local <pattern> which local ciphers with <pattern> are available? If pattern is not a number: word match
<pattern> is always an ignore case word pattern of cipher hexcode or any other string in the name, kx or bits
"testssl.sh <URI>", where <URI> is:
<URI> host|host:port|URL|URL:port port 443 is default, URL can only contain HTTPS protocol)
"testssl.sh [options] <URI>", where [options] is:
-t, --starttls <protocol> Does a default run against a STARTTLS enabled <protocol,
protocol is <ftp|smtp|lmtp|pop3|imap|xmpp|telnet|ldap|nntp|postgres|mysql>
--xmpphost <to_domain> For STARTTLS enabled XMPP it supplies the XML stream to-'' domain -- sometimes needed
--mx <domain/host> Tests MX records from high to low priority (STARTTLS, port 25)
--file/-iL <fname> Mass testing option: Reads one testssl.sh command line per line from <fname>.
Can be combined with --serial or --parallel. Implicitly turns on "--warnings batch".
Text format 1: Comments via
Text format 2: nmap output in greppable format (-oG), 1 port per line allowed
--mode <serial|parallel> Mass testing to be done serial (default) or parallel (--parallel is shortcut for the latter)
--warnings <batch|off> "batch" doesn't continue when a testing error is encountered, off continues and skips warnings
--connect-timeout <seconds> useful to avoid hangers. Max <seconds> to wait for the TCP socket connect to return
--openssl-timeout <seconds> useful to avoid hangers. Max <seconds> to wait before openssl connect will be terminated
single check as <options> ("testssl.sh URI" does everything except -E and -g):
-e, --each-cipher checks each local cipher remotely
-E, --cipher-per-proto checks those per protocol
-s, --std, --standard tests certain lists of cipher suites by strength
-p, --protocols checks TLS/SSL protocols (including SPDY/HTTP2)
-g, --grease tests several server implementation bugs like GREASE and size limitations
-S, --server-defaults displays the server's default picks and certificate info
-P, --server-preference displays the server's picks: protocol+cipher
-x, --single-cipher <pattern> tests matched <pattern> of ciphers
(if <pattern> not a number: word match)
-c, --client-simulation test client simulations, see which client negotiates with cipher and protocol
-h, --header, --headers tests HSTS, HPKP, server/app banner, security headers, cookie, reverse proxy, IPv4 address
-U, --vulnerable tests all (of the following) vulnerabilities (if applicable)
-H, --heartbleed tests for Heartbleed vulnerability
-I, --ccs, --ccs-injection tests for CCS injection vulnerability
-T, --ticketbleed tests for Ticketbleed vulnerability in BigIP loadbalancers
-BB, --robot tests for Return of Bleichenbacher's Oracle Threat (ROBOT) vulnerability
-R, --renegotiation tests for renegotiation vulnerabilities
-C, --compression, --crime tests for CRIME vulnerability (TLS compression issue)
-B, --breach tests for BREACH vulnerability (HTTP compression issue)
-O, --poodle tests for POODLE (SSL) vulnerability
-Z, --tls-fallback checks TLS_FALLBACK_SCSV mitigation
-W, --sweet32 tests 64 bit block ciphers (3DES, RC2 and IDEA): SWEET32 vulnerability
-A, --beast tests for BEAST vulnerability
-L, --lucky13 tests for LUCKY13
-F, --freak tests for FREAK vulnerability
-J, --logjam tests for LOGJAM vulnerability
-D, --drown tests for DROWN vulnerability
-f, --pfs, --fs, --nsa checks (perfect) forward secrecy settings
-4, --rc4, --appelbaum which RC4 ciphers are being offered?
tuning / connect options (most also can be preset via environment variables):
--fast omits some checks: using openssl for all ciphers (-e), show only first preferred cipher.
-9, --full includes tests for implementation bugs and cipher per protocol (could disappear)
--bugs enables the "-bugs" option of s_client, needed e.g. for some buggy F5s
--assume-http if protocol check fails it assumes HTTP protocol and enforces HTTP checks
--ssl-native fallback to checks with OpenSSL where sockets are normally used
--openssl <PATH> use this openssl binary (default: look in $PATH, $RUN_DIR of testssl.sh)
--proxy <host:port|auto> (experimental) proxy connects via <host:port>, auto: values from $env ($http(s)_proxy)
-6 also use IPv6. Works only with supporting OpenSSL version and IPv6 connectivity
--ip <ip> a) tests the supplied <ip> v4 or v6 address instead of resolving host(s) in URI
b) arg "one" means: just test the first DNS returns (useful for multiple IPs)
-n, --nodns <min|none> if "none": do not try any DNS lookups, "min" queries A, AAAA and MX records
--sneaky leave less traces in target logs: user agent, referer
--ids-friendly skips a few vulnerability checks which may cause IDSs to block the scanning IP
--phone-out allow to contact external servers for CRL download and querying OCSP responder
--add-ca <cafile> path to <cafile> or a comma separated list of CA files enables test against additional CAs.
--basicauth <user:pass> provide HTTP basic auth information.
output options (can also be preset via environment variables):
--quiet don't output the banner. By doing this you acknowledge usage terms normally appearing in the banner
--wide wide output for tests like RC4, BEAST. PFS also with hexcode, kx, strength, RFC name
--show-each for wide outputs: display all ciphers tested -- not only succeeded ones
--mapping <openssl| openssl: use the OpenSSL cipher suite name as the primary name cipher suite name form (default)
iana|rfc -> use the IANA/(RFC) cipher suite name as the primary name cipher suite name form
no-openssl| -> don't display the OpenSSL cipher suite name, display IANA/(RFC) names only
no-iana|no-rfc> -> don't display the IANA/(RFC) cipher suite name, display OpenSSL names only
--color <0|1|2|3> 0: no escape or other codes, 1: b/w escape codes, 2: color (default), 3: extra color (color all ciphers)
--colorblind swap green and blue in the output
--debug <0-6> 1: screen output normal but keeps debug output in /tmp/. 2-6: see "grep -A 5 '^DEBUG=' testssl.sh"
file output options (can also be preset via environment variables)
--log, --logging logs stdout to '${NODE}-p${port}${YYYYMMDD-HHMM}.log' in current working directory (cwd)
--logfile|-oL <logfile> logs stdout to 'dir/${NODE}-p${port}${YYYYMMDD-HHMM}.log'. If 'logfile' is a dir or to a specified 'logfile'
--json additional output of findings to flat JSON file '${NODE}-p${port}${YYYYMMDD-HHMM}.json' in cwd
--jsonfile|-oj <jsonfile> additional output to the specified flat JSON file or directory, similar to --logfile
--json-pretty additional JSON structured output of findings to a file '${NODE}-p${port}${YYYYMMDD-HHMM}.json' in cwd
--jsonfile-pretty|-oJ <jsonfile> additional JSON structured output to the specified file or directory, similar to --logfile
--csv additional output of findings to CSV file '${NODE}-p${port}${YYYYMMDD-HHMM}.csv' in cwd or directory
--csvfile|-oC <csvfile> additional output as CSV to the specified file or directory, similar to --logfile
--html additional output as HTML to file '${NODE}-p${port}${YYYYMMDD-HHMM}.html'
--htmlfile|-oH <htmlfile> additional output as HTML to the specified file or directory, similar to --logfile
--out(f,F)ile|-oa/-oA <fname> log to a LOG,JSON,CSV,HTML file (see nmap). -oA/-oa: pretty/flat JSON.
"auto" uses '${NODE}-p${port}${YYYYMMDD-HHMM}'. If fname if a dir uses 'dir/${NODE}-p${port}${YYYYMMDD-HHMM}'
--hints additional hints to findings
--severity <severity> severities with lower level will be filtered for CSV+JSON, possible values <LOW|MEDIUM|HIGH|CRITICAL>
--append if (non-empty) <logfile>, <csvfile>, <jsonfile> or <htmlfile> exists, append to file. Omits any header
--outprefix <fname_prefix> before '${NODE}.' above prepend <fname_prefix>
Options requiring a value can also be called with '=' e.g. testssl.sh -t=smtp --wide --openssl=/usr/bin/openssl <URI>.
<URI> always needs to be the last parameter.
测试
Test All(全集)
直接后面接URL 或URL:Port,则开始对URL全部功能的Check测试
./testssl.sh TARGET_HOST
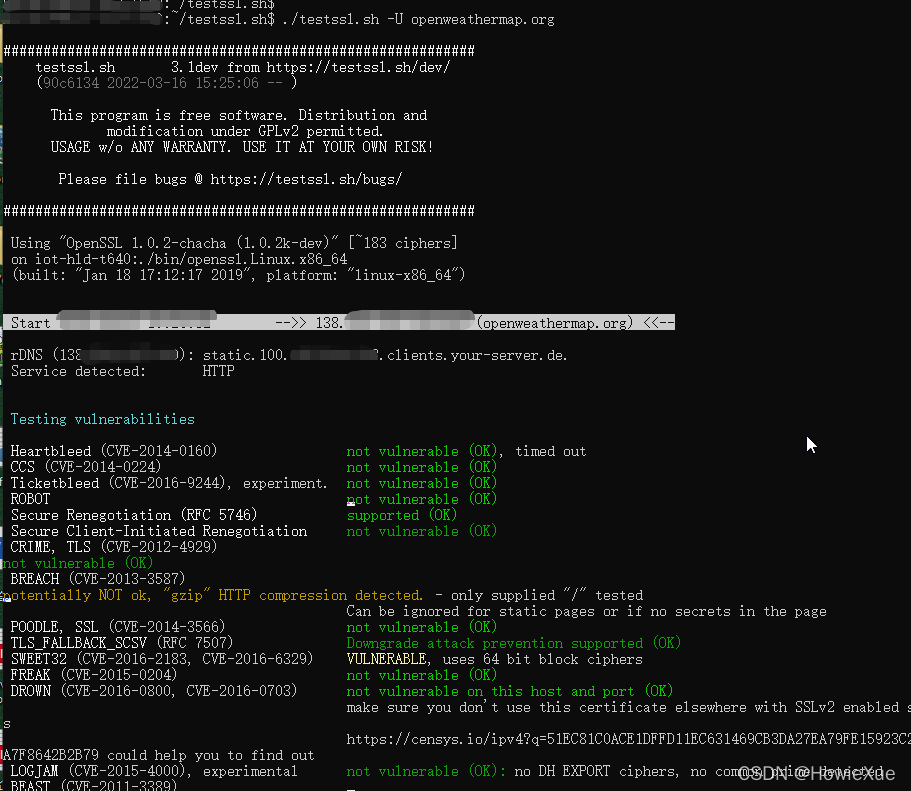
这里以一个天气(openweathermap)网站 举例:
./testssl.sh openweathermap.org
or
./testssl.sh https://openweathermap.org/
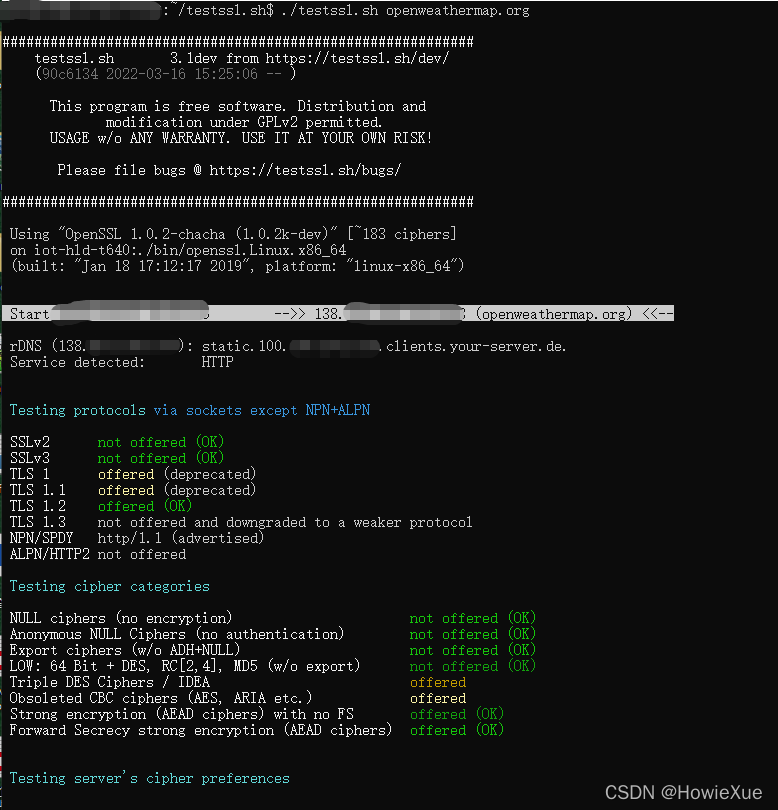
Test all 全部output如下:
~/testssl.sh$ ./testssl.sh openweathermap.org
testssl.sh 3.1dev from https://testssl.sh/dev/
(90c6134 2022-03-16 15:25:06 -- )
This program is free software. Distribution and
modification under GPLv2 permitted.
USAGE w/o ANY WARRANTY. USE IT AT YOUR OWN RISK!
Please file bugs @ https://testssl.sh/bugs/
Using "OpenSSL 1.0.2-chacha (1.0.2k-dev)" [~183 ciphers]
on iot-hld-t640:./bin/openssl.Linux.x86_64
(built: "Jan 18 17:12:17 2019", platform: "linux-x86_64")
Service detected: HTTP
Testing protocols via sockets except NPN+ALPN
SSLv2 not offered (OK)
SSLv3 not offered (OK)
TLS 1 offered (deprecated)
TLS 1.1 offered (deprecated)
TLS 1.2 offered (OK)
TLS 1.3 not offered and downgraded to a weaker protocol
NPN/SPDY http/1.1 (advertised)
ALPN/HTTP2 not offered
Testing cipher categories
NULL ciphers (no encryption) not offered (OK)
Anonymous NULL Ciphers (no authentication) not offered (OK)
Export ciphers (w/o ADH+NULL) not offered (OK)
LOW: 64 Bit + DES, RC[2,4], MD5 (w/o export) not offered (OK)
Triple DES Ciphers / IDEA offered
Obsoleted CBC ciphers (AES, ARIA etc.) offered
Strong encryption (AEAD ciphers) with no FS offered (OK)
Forward Secrecy strong encryption (AEAD ciphers) offered (OK)
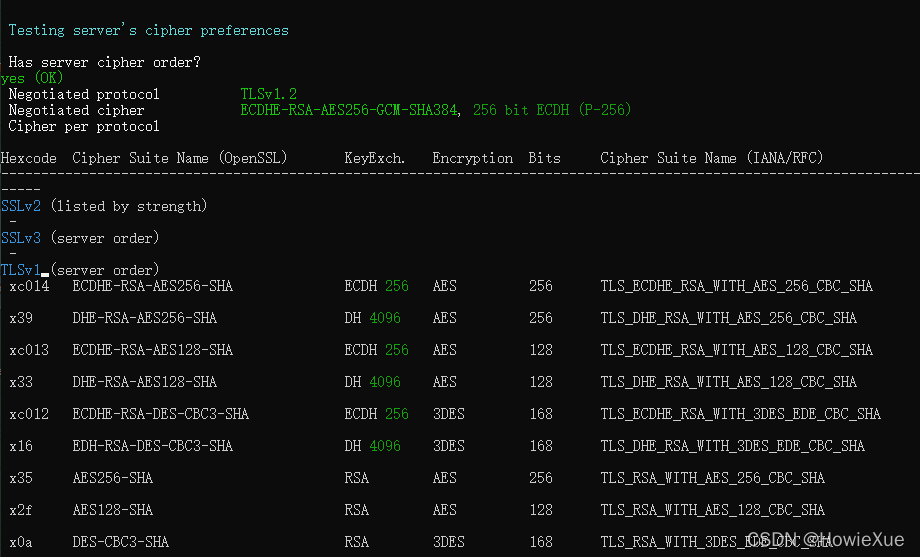
Testing server's cipher preferences
Has server cipher order? yes (OK)
Negotiated protocol TLSv1.2
Negotiated cipher ECDHE-RSA-AES256-GCM-SHA384, 256 bit ECDH (P-256)
Cipher per protocol
Hexcode Cipher Suite Name (OpenSSL) KeyExch. Encryption Bits Cipher Suite Name (IANA/RFC)
-----------------------------------------------------------------------------------------------------------------------------
SSLv2
-
SSLv3
-
TLSv1 (server order)
xc014 ECDHE-RSA-AES256-SHA ECDH 256 AES 256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
x39 DHE-RSA-AES256-SHA DH 4096 AES 256 TLS_DHE_RSA_WITH_AES_256_CBC_SHA
xc013 ECDHE-RSA-AES128-SHA ECDH 256 AES 128 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
x33 DHE-RSA-AES128-SHA DH 4096 AES 128 TLS_DHE_RSA_WITH_AES_128_CBC_SHA
xc012 ECDHE-RSA-DES-CBC3-SHA ECDH 256 3DES 168 TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
x16 EDH-RSA-DES-CBC3-SHA DH 4096 3DES 168 TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
x35 AES256-SHA RSA AES 256 TLS_RSA_WITH_AES_256_CBC_SHA
x2f AES128-SHA RSA AES 128 TLS_RSA_WITH_AES_128_CBC_SHA
x0a DES-CBC3-SHA RSA 3DES 168 TLS_RSA_WITH_3DES_EDE_CBC_SHA
TLSv1.1 (server order)
xc014 ECDHE-RSA-AES256-SHA ECDH 256 AES 256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
x39 DHE-RSA-AES256-SHA DH 4096 AES 256 TLS_DHE_RSA_WITH_AES_256_CBC_SHA
xc013 ECDHE-RSA-AES128-SHA ECDH 256 AES 128 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
x33 DHE-RSA-AES128-SHA DH 4096 AES 128 TLS_DHE_RSA_WITH_AES_128_CBC_SHA
xc012 ECDHE-RSA-DES-CBC3-SHA ECDH 256 3DES 168 TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
x16 EDH-RSA-DES-CBC3-SHA DH 4096 3DES 168 TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
x35 AES256-SHA RSA AES 256 TLS_RSA_WITH_AES_256_CBC_SHA
x2f AES128-SHA RSA AES 128 TLS_RSA_WITH_AES_128_CBC_SHA
x0a DES-CBC3-SHA RSA 3DES 168 TLS_RSA_WITH_3DES_EDE_CBC_SHA
TLSv1.2 (server order)
xc030 ECDHE-RSA-AES256-GCM-SHA384 ECDH 256 AESGCM 256 TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
xc02f ECDHE-RSA-AES128-GCM-SHA256 ECDH 256 AESGCM 128 TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
x9f DHE-RSA-AES256-GCM-SHA384 DH 4096 AESGCM 256 TLS_DHE_RSA_WITH_AES_256_GCM_SHA384
x9e DHE-RSA-AES128-GCM-SHA256 DH 4096 AESGCM 128 TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
xc028 ECDHE-RSA-AES256-SHA384 ECDH 256 AES 256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
xc014 ECDHE-RSA-AES256-SHA ECDH 256 AES 256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
x6b DHE-RSA-AES256-SHA256 DH 4096 AES 256 TLS_DHE_RSA_WITH_AES_256_CBC_SHA256
x39 DHE-RSA-AES256-SHA DH 4096 AES 256 TLS_DHE_RSA_WITH_AES_256_CBC_SHA
xc027 ECDHE-RSA-AES128-SHA256 ECDH 256 AES 128 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
xc013 ECDHE-RSA-AES128-SHA ECDH 256 AES 128 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
x67 DHE-RSA-AES128-SHA256 DH 4096 AES 128 TLS_DHE_RSA_WITH_AES_128_CBC_SHA256
x33 DHE-RSA-AES128-SHA DH 4096 AES 128 TLS_DHE_RSA_WITH_AES_128_CBC_SHA
xc012 ECDHE-RSA-DES-CBC3-SHA ECDH 256 3DES 168 TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
x16 EDH-RSA-DES-CBC3-SHA DH 4096 3DES 168 TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
x9d AES256-GCM-SHA384 RSA AESGCM 256 TLS_RSA_WITH_AES_256_GCM_SHA384
x9c AES128-GCM-SHA256 RSA AESGCM 128 TLS_RSA_WITH_AES_128_GCM_SHA256
x3d AES256-SHA256 RSA AES 256 TLS_RSA_WITH_AES_256_CBC_SHA256
x3c AES128-SHA256 RSA AES 128 TLS_RSA_WITH_AES_128_CBC_SHA256
x35 AES256-SHA RSA AES 256 TLS_RSA_WITH_AES_256_CBC_SHA
x2f AES128-SHA RSA AES 128 TLS_RSA_WITH_AES_128_CBC_SHA
x0a DES-CBC3-SHA RSA 3DES 168 TLS_RSA_WITH_3DES_EDE_CBC_SHA
TLSv1.3
-
Testing robust forward secrecy (FS) -- omitting Null Authentication/Encryption, 3DES, RC4
FS is offered (OK) ECDHE-RSA-AES256-GCM-SHA384 ECDHE-RSA-AES256-SHA384 ECDHE-RSA-AES256-SHA
DHE-RSA-AES256-GCM-SHA384 DHE-RSA-AES256-SHA256 DHE-RSA-AES256-SHA
ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES128-SHA256 ECDHE-RSA-AES128-SHA
DHE-RSA-AES128-GCM-SHA256
Elliptic curves offered: prime256v1
DH group offered: Unknown DH group (4096 bits)
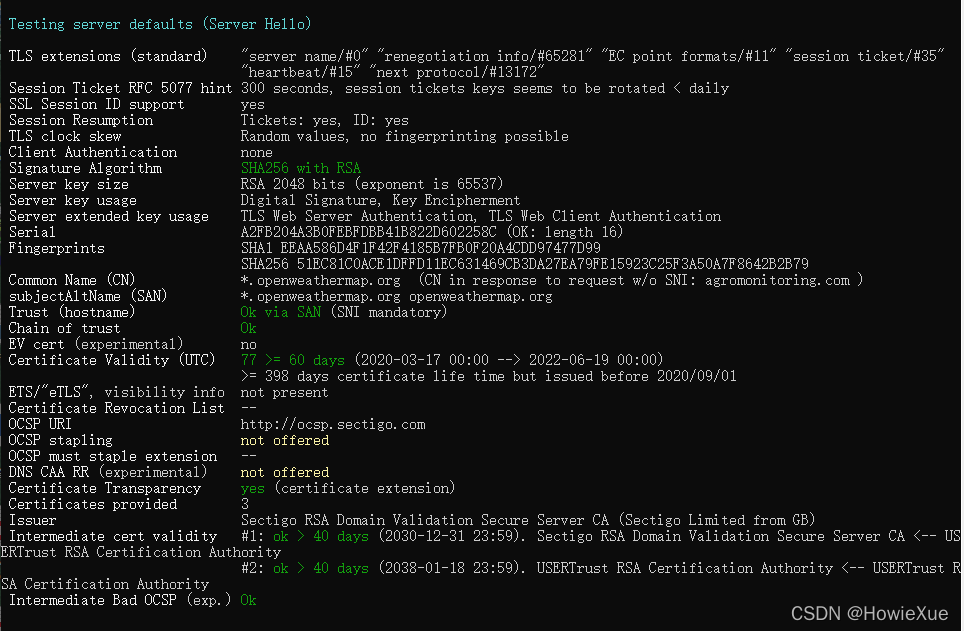
Testing server defaults (Server Hello)
TLS extensions (standard) "server name/#0" "renegotiation info/#65281" "EC point formats/#11" "session ticket/#35"
"heartbeat/#15" "next protocol/#13172"
Session Ticket RFC 5077 hint 300 seconds, session tickets keys seems to be rotated < daily
SSL Session ID support yes
Session Resumption Tickets: yes, ID: yes
TLS clock skew Random values, no fingerprinting possible
Client Authentication none
Signature Algorithm SHA256 with RSA
Server key size RSA 2048 bits (exponent is 65537)
Server key usage Digital Signature, Key Encipherment
Server extended key usage TLS Web Server Authentication, TLS Web Client Authentication
Serial A2FB204A3B0FEBFDBB41B822D602258C (OK: length 16)
Fingerprints SHA1 EEAA586D4F1F42F4185B7FB0F20A4CDD97477D99
SHA256 51EC81C0ACE1DFFD11EC631469CB3DA27EA79FE15923C25F3A50A7F8642B2B79
Common Name (CN) *.openweathermap.org (CN in response to request w/o SNI: agromonitoring.com )
subjectAltName (SAN) *.openweathermap.org openweathermap.org
Trust (hostname) Ok via SAN (SNI mandatory)
Chain of trust Ok
EV cert (experimental) no
Certificate Validity (UTC) 77 >= 60 days (2020-03-17 00:00 --> 2022-06-19 00:00)
>= 398 days certificate life time but issued before 2020/09/01
ETS/"eTLS", visibility info not present
Certificate Revocation List --
OCSP URI http://ocsp.sectigo.com
OCSP stapling not offered
OCSP must staple extension --
DNS CAA RR (experimental) not offered
Certificate Transparency yes (certificate extension)
Certificates provided 3
Issuer Sectigo RSA Domain Validation Secure Server CA (Sectigo Limited from GB)
Intermediate cert validity
Intermediate Bad OCSP (exp.) Ok
Testing HTTP header response @ "/"
HTTP Status Code 200 OK
HTTP clock skew -1 sec from localtime
Strict Transport Security not offered
Public Key Pinning --
Server banner openresty/1.9.7.1
Application banner X-Powered-By: PHP/7.2.15
Cookie(s) 1 issued: NOT secure, 1/1 HttpOnly
Security headers Cache-Control: private, must-revalidate
Pragma: no-cache
Reverse Proxy banner --
Testing vulnerabilities
Heartbleed (CVE-2014-0160) not vulnerable (OK), timed out
CCS (CVE-2014-0224) not vulnerable (OK)
Ticketbleed (CVE-2016-9244), experiment. not vulnerable (OK)
ROBOT not vulnerable (OK)
Secure Renegotiation (RFC 5746) supported (OK)
Secure Client-Initiated Renegotiation not vulnerable (OK)
CRIME, TLS (CVE-2012-4929) not vulnerable (OK)
BREACH (CVE-2013-3587) potentially NOT ok, "gzip" HTTP compression detected. - only supplied "/" tested
Can be ignored for static pages or if no secrets in the page
POODLE, SSL (CVE-2014-3566) not vulnerable (OK), no SSLv3 support
TLS_FALLBACK_SCSV (RFC 7507) Downgrade attack prevention supported (OK)
SWEET32 (CVE-2016-2183, CVE-2016-6329) VULNERABLE, uses 64 bit block ciphers
FREAK (CVE-2015-0204) not vulnerable (OK)
DROWN (CVE-2016-0800, CVE-2016-0703) not vulnerable on this host and port (OK)
make sure you don't use this certificate elsewhere with SSLv2 enabled services
https://censys.io/ipv4?q=51EC81C0ACE1DFFD11EC631469CB3DA27EA79FE15923C25F3A50A7F8642B2B79 could help you to find out
LOGJAM (CVE-2015-4000), experimental not vulnerable (OK): no DH EXPORT ciphers, no common prime detected
BEAST (CVE-2011-3389) TLS1: ECDHE-RSA-AES256-SHA DHE-RSA-AES256-SHA ECDHE-RSA-AES128-SHA
DHE-RSA-AES128-SHA ECDHE-RSA-DES-CBC3-SHA EDH-RSA-DES-CBC3-SHA
AES256-SHA AES128-SHA DES-CBC3-SHA
VULNERABLE -- but also supports higher protocols TLSv1.1 TLSv1.2 (likely mitigated)
LUCKY13 (CVE-2013-0169), experimental potentially VULNERABLE, uses cipher block chaining (CBC) ciphers with TLS. Check patches
Winshock (CVE-2014-6321), experimental not vulnerable (OK) - CAMELLIA or ECDHE_RSA GCM ciphers found
RC4 (CVE-2013-2566, CVE-2015-2808) no RC4 ciphers detected (OK)
Running client simulations (HTTP) via sockets
Browser Protocol Cipher Suite Name (OpenSSL) Forward Secrecy
------------------------------------------------------------------------------------------------
Android 4.4.2 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Android 5.0.0 TLSv1.2 ECDHE-RSA-AES128-GCM-SHA256 256 bit ECDH (P-256)
Android 6.0 TLSv1.2 ECDHE-RSA-AES128-GCM-SHA256 256 bit ECDH (P-256)
Android 7.0 (native) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Android 8.1 (native) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Android 9.0 (native) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Android 10.0 (native) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Chrome 74 (Win 10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Chrome 79 (Win 10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Firefox 66 (Win 8.1/10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Firefox 71 (Win 10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
IE 6 XP No connection
IE 8 Win 7 TLSv1.0 ECDHE-RSA-AES256-SHA 256 bit ECDH (P-256)
IE 8 XP TLSv1.0 DES-CBC3-SHA No FS
IE 11 Win 7 TLSv1.2 DHE-RSA-AES256-GCM-SHA384 4096 bit DH
IE 11 Win 8.1 TLSv1.2 DHE-RSA-AES256-GCM-SHA384 4096 bit DH
IE 11 Win Phone 8.1 TLSv1.2 ECDHE-RSA-AES256-SHA 256 bit ECDH (P-256)
IE 11 Win 10 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Edge 15 Win 10 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Edge 17 (Win 10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Opera 66 (Win 10) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Safari 9 iOS 9 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Safari 9 OS X 10.11 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Safari 10 OS X 10.12 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Safari 12.1 (iOS 12.2) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Safari 13.0 (macOS 10.14.6) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Apple ATS 9 iOS 9 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Java 6u45 No connection
Java 7u25 TLSv1.0 ECDHE-RSA-AES128-SHA 256 bit ECDH (P-256)
Java 8u161 TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Java 11.0.2 (OpenJDK) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Java 12.0.1 (OpenJDK) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
OpenSSL 1.0.2e TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
OpenSSL 1.1.0l (Debian) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
OpenSSL 1.1.1d (Debian) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Thunderbird (68.3) TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384 256 bit ECDH (P-256)
Rating (experimental)
Rating specs (not complete) SSL Labs's 'SSL Server Rating Guide' (version 2009q from 2020-01-30)
Specification documentation https://github.com/ssllabs/research/wiki/SSL-Server-Rating-Guide
Protocol Support (weighted) 95 (28)
Key Exchange (weighted) 90 (27)
Cipher Strength (weighted) 90 (36)
Final Score 91
Overall Grade B
Grade cap reasons Grade capped to B. TLS 1.1 offered
Grade capped to B. TLS 1.0 offered
Grade capped to A. HSTS is not offered
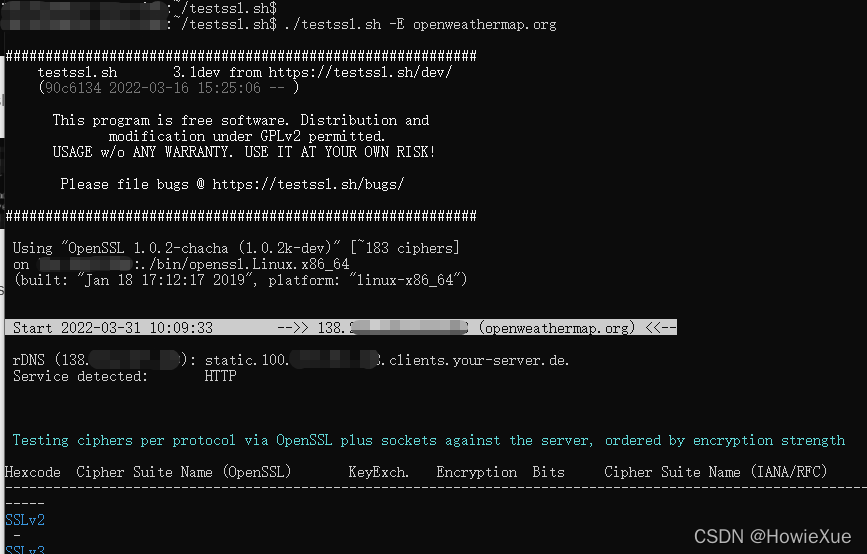
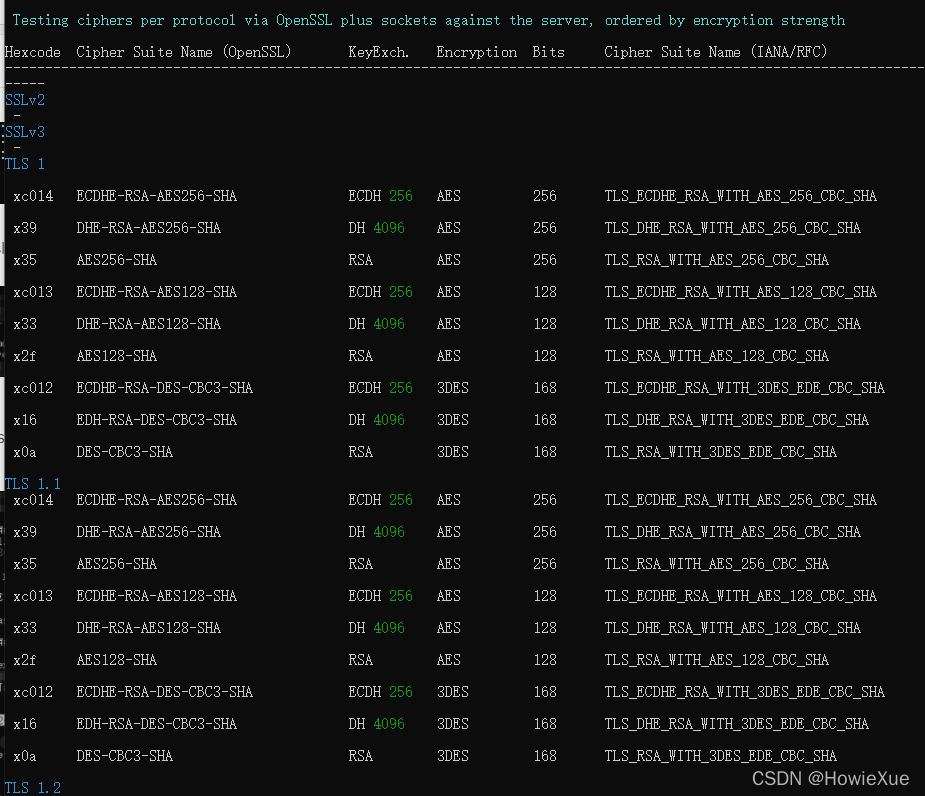
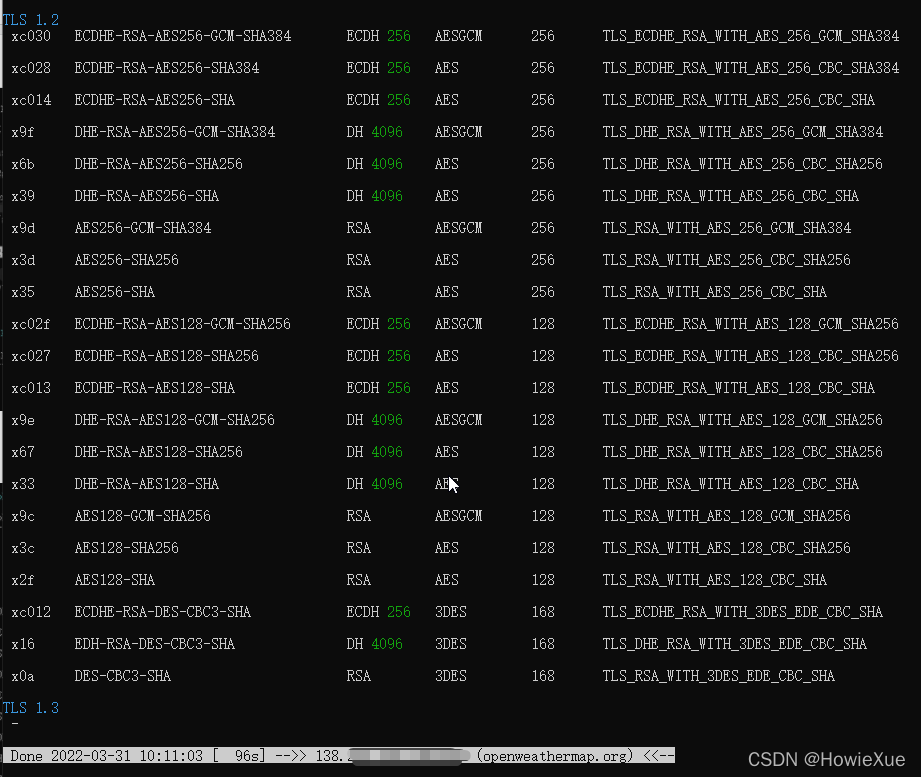
Test Ciphersuites(密码套件集)
使用-E 可以查看Server支持的各Protocol Ciphersuites
./testssl.sh -E openweathermap.org
Test Vulnerable(漏洞)
./testssl.sh -U openweathermap.org
Test Server Defaults
./testssl.sh -S openweathermap.org
Test Server Preference
./testssl.sh -P openweathermap.org
Web网页版testssl.sh(免安装):
Web版可以不用安装,直接使用
传送门:https://inspect.rapydblok.com
注:网页版使用要注意隐私,自用server推荐还是用cmb版测试

Web版在浏览器输入URL点击Scan即可

附
https://openweathermap.org/
博主热门文章推荐:
一篇读懂系列:
- 一篇读懂无线充电技术(附方案选型及原理分析)
- 一篇读懂:Android/iOS手机如何通过音频接口(耳机孔)与外设通信
- 一篇读懂:Android手机如何通过USB接口与外设通信(附原理分析及方案选型)
LoRa Mesh系列:
- LoRa学习:LoRa关键参数(扩频因子,编码率,带宽)的设定及解释
- LoRa学习:信道占用检测原理(CAD)
- LoRa/FSK 无线频谱波形分析(频谱分析仪测试LoRa/FSK带宽、功率、频率误差等)
网络安全系列:
- ATECC508A芯片开发笔记(一):初识加密芯片
- SHA/HMAC/AES-CBC/CTR 算法执行效率及RAM消耗 测试结果
- 常见加密/签名/哈希算法性能比较 (多平台 AES/DES, DH, ECDSA, RSA等)
- AES加解密效率测试(纯软件AES128/256)–以嵌入式Cortex-M0与M3 平台为例
嵌入式开发系列:
- 嵌入式学习中较好的练手项目和课题整理(附代码资料、学习视频和嵌入式学习规划)
- IAR调试使用技巧汇总:数据断点、CallStack、设置堆栈、查看栈使用和栈深度、Memory、Set Next Statement等
- Linux内核编译配置(Menuconfig)、制作文件系统 详细步骤
- Android底层调用C代码(JNI实现)
- 树莓派到手第一步:上电启动、安装中文字体、虚拟键盘、开启SSH等
- Android/Linux设备有线&无线 双网共存(同时上内、外网)
AI / 机器学习系列:
- AI: 机器学习必须懂的几个术语:Lable、Feature、Model…
- AI:卷积神经网络CNN 解决过拟合的方法 (Overcome Overfitting)
- AI: 什么是机器学习的数据清洗(Data Cleaning)
- AI: 机器学习的模型是如何训练的?(在试错中学习)
- 数据可视化:TensorboardX安装及使用(安装测试+实例演示)
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)