CVE-2012-0002/CVE-2012-0152 漏洞处理
发现漏洞
- 通过nmap扫描windows server 发现上述 CVE-2012-002/ CVE-2012-0152,扫描结果如下
Host is up (0.053s latency).
Not shown: 954 closed tcp ports (reset), 34 filtered tcp ports (no-response)
PORT STATE SERVICE
3389/tcp open ms-wbt-server
|_ssl-ccs-injection: No reply from server (TIMEOUT)
| rdp-vuln-ms12-020:
| VULNERABLE:
| MS12-020 Remote Desktop Protocol Denial Of Service Vulnerability
| State: VULNERABLE
| IDs: CVE:CVE-2012-0152
| Risk factor: Medium CVSSv2: 4.3 (MEDIUM) (AV:N/AC:M/Au:N/C:N/I:N/A:P)
| Remote Desktop Protocol vulnerability that could allow remote attackers to cause a denial of service.
|
| Disclosure date: 2012-03-13
| References:
| http://technet.microsoft.com/en-us/security/bulletin/ms12-020
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0152
|
| MS12-020 Remote Desktop Protocol Remote Code Execution Vulnerability
| State: VULNERABLE
| IDs: CVE:CVE-2012-0002
| Risk factor: High CVSSv2: 9.3 (HIGH) (AV:N/AC:M/Au:N/C:C/I:C/A:C)
| Remote Desktop Protocol vulnerability that could allow remote attackers to execute arbitrary code on the targeted system.
|
| Disclosure date: 2012-03-13
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0002
|_ http://technet.microsoft.com/en-us/security/bulletin/ms12-020
补丁信息查找
- 访问国家信息安全漏洞库地址或CVE HOME,查找相关补丁。
- 国家信息安全漏洞库 http://www.cnnvd.org.cn
- CVE HOME https://cve.mitre.org/cve/
过程示例
- 本文以登录国家信息安全漏洞库为例,登录后搜索相关CVE编号
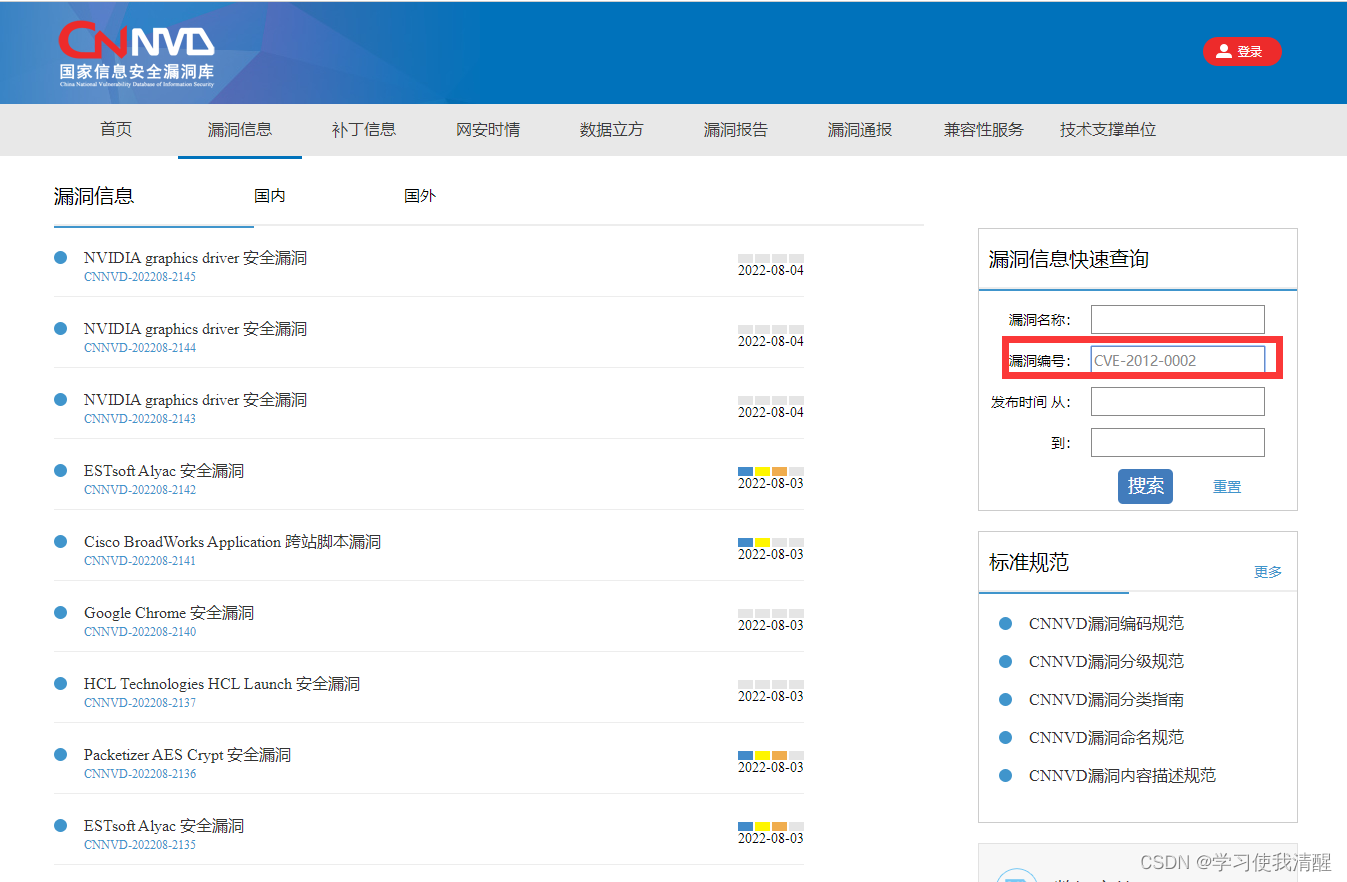
- 查询到漏洞相关信息,包含 危害等级、发布时间、威胁类型,关联厂商、CNNVD编号等

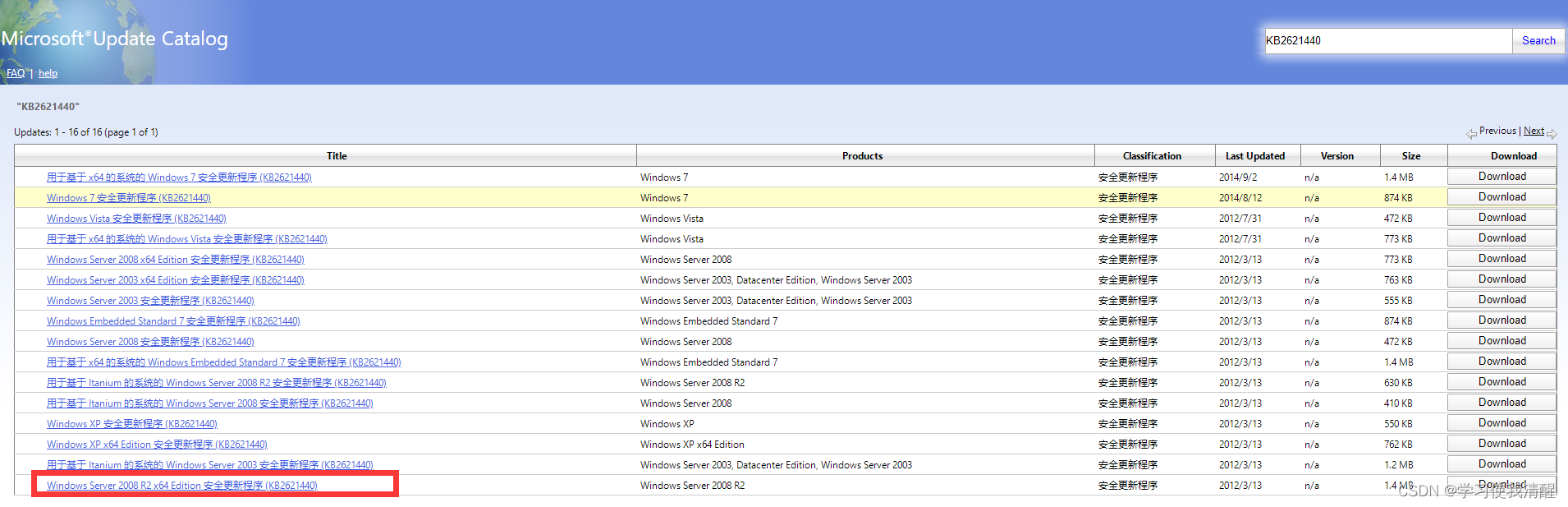
- 根据漏洞公告相关提示点击补丁获取链接地址,本文以 server 2008 R2 为例。
http://technet.microsoft.com/zh-cn/security/bulletin/ms12-020

下载补丁
https://www.catalog.update.microsoft.com/Home.aspx
补丁安装
- 下载后直接运行安装即可,如需重启Server,务必重启,重启后查询已安装的补
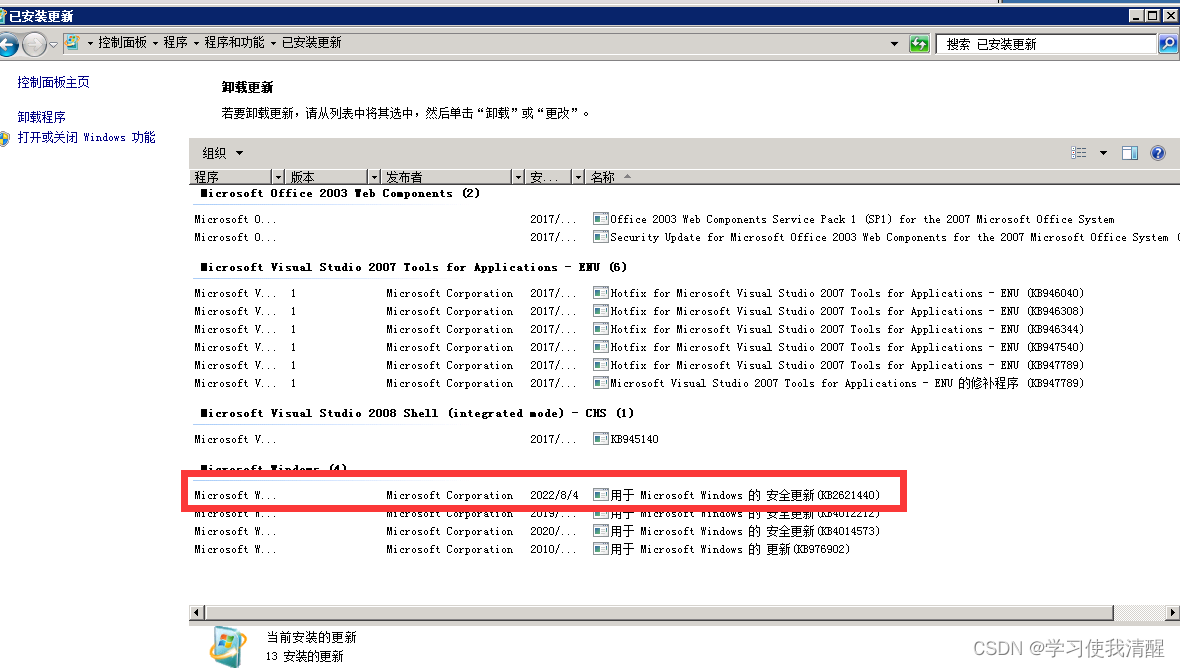
- msi补丁安装完毕后,可通过KALI msfconsle进行漏洞复现或nmap扫描,使用nmap进行常见漏洞扫描后,未发现该漏洞,处理完成。
漏洞处理结束