这里写目录标题
- 一、TLS加密通讯的概述
- 二、TLS加密通讯的部署
- 2.1、搭建环境
- 2.2 部署过程
- 2.3 验证加密通讯
一、TLS加密通讯的概述
- 用TLS加密通讯原因:
为了防止链路劫持、会话劫持等问题导致 Docker 通信时被中 间人攻击,c/s 两端应该通过加密方式通讯。 - 对称密钥,例如DES、3DES、AES,长度不同,长度越长安全越高,解密速度越慢。
- 非对称密钥,分为公钥和私钥,例如RSA 公钥:所有人可知(锁),私钥(钥匙)个人身份信息,不可抵赖。
- 封装在证书中:个人信息,密钥,有效期
二、TLS加密通讯的部署
2.1、搭建环境
| 节点 | 地址 | 安装软件 |
|---|
| master | 20.0.0.50 | docker-ce |
| Client | 20.0.0.60 | docker-ce |
2.2 部署过程
[root@cgroup ~]
[root@cgroup ~]
[root@master ~]
[root@master ~]
[root@master ~]
[root@master ~]
[root@master tls]
127.0.0.1 master
[root@master tls]
Generating RSA private key, 4096 bit long modulus
......................................................................................................................................++
.........................++
e is 65537 (0x10001)
Enter pass phrase for ca-key.pem:
Verifying - Enter pass phrase for ca-key.pem:
[root@master tls]
Enter pass phrase for ca-key.pem:
[root@master tls]
Generating RSA private key, 4096 bit long modulus
.........................................++
......................................++
e is 65537 (0x10001)
[root@master tls]
[root@master tls]
Signature ok
subject=/CN=*
Getting CA Private Key
Enter pass phrase for ca-key.pem:
[root@master tls]
Generating RSA private key, 4096 bit long modulus
........................................................................................................................................................................................................++
..++
e is 65537 (0x10001)
[root@master tls]
[root@master tls]
[root@master tls]
Signature ok
subject=/CN=client
Getting CA Private Key
Enter pass phrase for ca-key.pem:
[root@master tls]
[root@master tls]
ca-key.pem ca.pem cert.pem key.pem server-cert.pem server-key.pem
-
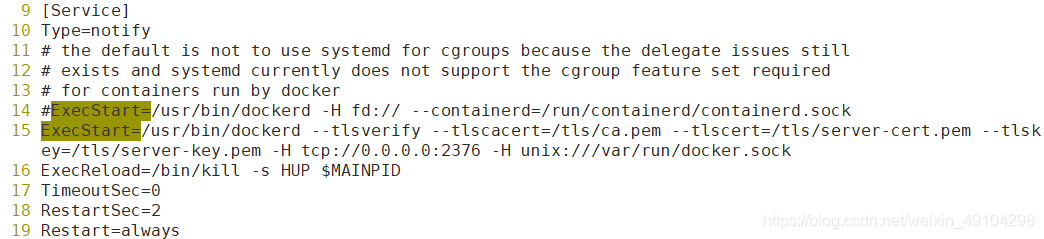
配置docker
vim /lib/systemd/system/docker.service
-
重启进程
systemctl daemon-reload
-
重启docker服务
systemctl restart docker
-
将 /tls/ca.pem /tls/cert.pem /tls/key.pem 三个文件复制到另一台主机
[root@master tls]# scp ca.pem root@20.0.0.60:/etc/docker/
The authenticity of host '20.0.0.60 (20.0.0.60)' can't be established.
ECDSA key fingerprint is SHA256:N36uwPtXA/RHGdEsLwiaV6x0pMPitNj+MSO3APPZtC4.
ECDSA key fingerprint is MD5:14:cf:b4:13:36:a1:ea:c6:dc:01:f5:83:65:ca:b0:39.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '20.0.0.60' (ECDSA) to the list of known hosts.
root@20.0.0.60's password:
ca.pem 100% 1765 2.6MB/s 00:00
[root@master tls]# scp cert.pem root@20.0.0.60:/etc/docker/
root@20.0.0.60's password:
cert.pem 100% 1696 1.3MB/s 00:00
[root@master tls]# scp key.pem root@20.0.0.60:/etc/docker/
root@20.0.0.60's password:
key.pem 100% 3247 1.3MB/s 00:00
2.3 验证加密通讯
[root@master tls]
Client: Docker Engine - Community
Version: 19.03.13
API version: 1.40
Go version: go1.13.15
Git commit: 4484c46d9d
Built: Wed Sep 16 17:03:45 2020
OS/Arch: linux/amd64
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.13
API version: 1.40 (minimum version 1.12)
Go version: go1.13.15
Git commit: 4484c46d9d
Built: Wed Sep 16 17:02:21 2020
OS/Arch: linux/amd64
Experimental: false
containerd:
Version: 1.3.7
GitCommit: 8fba4e9a7d01810a393d5d25a3621dc101981175
runc:
Version: 1.0.0-rc10
GitCommit: dc9208a3303feef5b3839f4323d9beb36df0a9dd
docker-init:
Version: 0.18.0
GitCommit: fec3683
[root@client ~]
20.0.0.50 master
[root@client ~]
[root@client docker]
Client: Docker Engine - Community
Version: 19.03.13
API version: 1.40
Go version: go1.13.15
Git commit: 4484c46d9d
Built: Wed Sep 16 17:03:45 2020
OS/Arch: linux/amd64
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.13
API version: 1.40 (minimum version 1.12)
Go version: go1.13.15
Git commit: 4484c46d9d
Built: Wed Sep 16 17:02:21 2020
OS/Arch: linux/amd64
Experimental: false
containerd:
Version: 1.3.7
GitCommit: 8fba4e9a7d01810a393d5d25a3621dc101981175
runc:
Version: 1.0.0-rc10
GitCommit: dc9208a3303feef5b3839f4323d9beb36df0a9dd
docker-init:
Version: 0.18.0
GitCommit: fec3683
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系:hwhale#tublm.com(使用前将#替换为@)